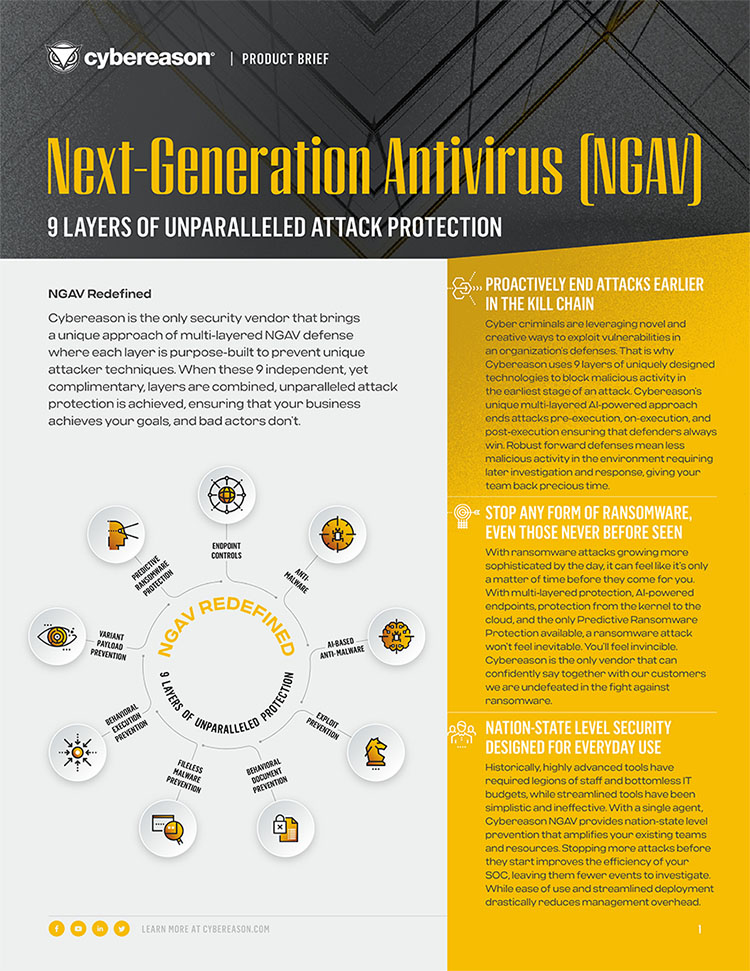
9 Layers of Unparalleled Attack Protection
Cybereason NGAV leverages 9 unique prevention layers enabling security practitioners to defend forward and proactively end attacks earlier in the kill chain, stop any form of ransomware even those never before seen, and achieve nation-state level prevention without losing operational simplicity.
Read the Data Sheet