Cybersecurity 101
Explore the fundamentals of cybersecurity
Explore the fundamentals of cybersecurity
XDR looks across multiple streams of data to provide a clear overview and analysis of all security layers.
EPP technology includes anti-virus protection, data encryption, intrusion prevention, data loss prevention, and more.
The MITRE ATT&CK Framework helps cybersecurity professionals better understand adversary behavior to protect against attacks.
Learn more about ransomware, how it's deployed, and how to prevent becoming a victim of a ransomware attack yourself.
Endpoint Detection and Response (EDR) can be used to instantly remediate by killing processes, quarantining files, removing persistence mechanisms, preventing file execution and isolating machines.
Traditional antivirus can't keep pace with today's highly sophisticated, 0-day attacks. NGAV solutions are rising to meet the challenge.
Learn more about Threat Hunting and how organizations can transform their cybersecurity methods from reactive to proactive.
Learn more about MDR (Managed Detection and Response) and how it extends your security team's capabilities to detect and prevent malicious operations.
APT attacks are sophisticated in planning and operation, but they often use relatively unsophisticated means of intrusion, like social engineering, email phishing, or zero-day viruses.
Gain a better understanding of what malware is, what it isn't, and how you can prevent and detect its presence in your environment before the crown jewels are compromised.
Digital evidence is often involved in crimes, and every serious security incident or data breach requires a post-mortem investigation that only DFIR personnel can provide.
Zero Trust remains a misunderstood term in security. Learn more about Zero Trust and what it means for your organization.
 Analyst Report
Analyst Report
Cybereason has been named a Leader in the recently released 2022 Gartner Magic Quadrant for Endpoint Protection Platforms. This is Cybereason’s second appearance in the Gartner Magic Quadrant, previously a Visionary and now a Leader.
Learn Why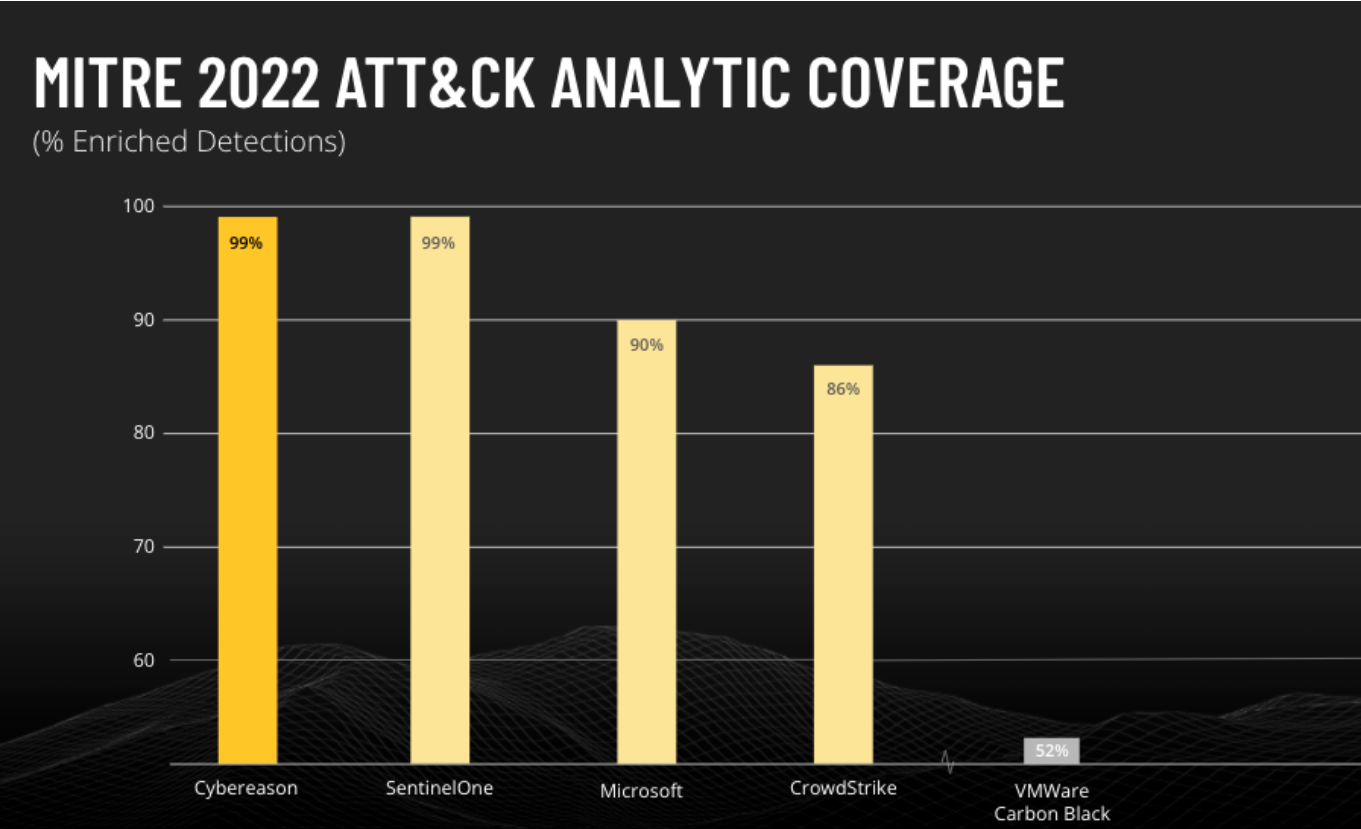 Analyst Report
Analyst Report
Cybereason received the highest scores in history from MITRE ATT&CK Evaluations, scoring 100% in prevention tests, 100% in real-time detection coverage, and was the only vendor to deliver 100% visibility across all operating systems.
Learn More Analyst Report
Analyst Report
Find out why Forrester stated in the 2020 Endpoint Detection & Response Wave that, "Cybereason futureproofed their EDR product by architecting it with the vision of combining the detection analytics synonymous with the EDR Market."
Read the Report