Cybereason Compromise Assessment
A Cybereason Compromise Assessment will help organizations identify past or present malicious activity within their network. The Cybereason Services Team leverages the Cybereason Defense Platform and Nocturnus Intelligence to hunt for, respond to, and remediate any malicious operations (MalOps) within the network. The result is a reduction in dwell time, attack mitigation, and expulsion of malicious operations before further damage can be done.
Methodology
Mergers & Acquisitions
Ensure that a cyber-attack isn’t part of an acquisition. As part of it’s due-diligence, the acquiring company should conduct a Compromise Assessment for the company-to-be-acquired, ensuring that there are no ongoing attacks or MalOps that will be assumed.
New Security Team
Oftentimes CISOs and security teams inherit legacy security tools and solutions. A Compromise Assessment will give a security team a clear understanding of whether or not the network has been breached in the past, and present.
Suspicion of an Attack
Take the guesswork and suspension out of an attack, by knowing exactly what machines were compromised, how they were compromised and when the attack took place. A Compromise Assessment will answer the question: “Have we been breached.”
Customer Outcomes
Why Cybereason Services
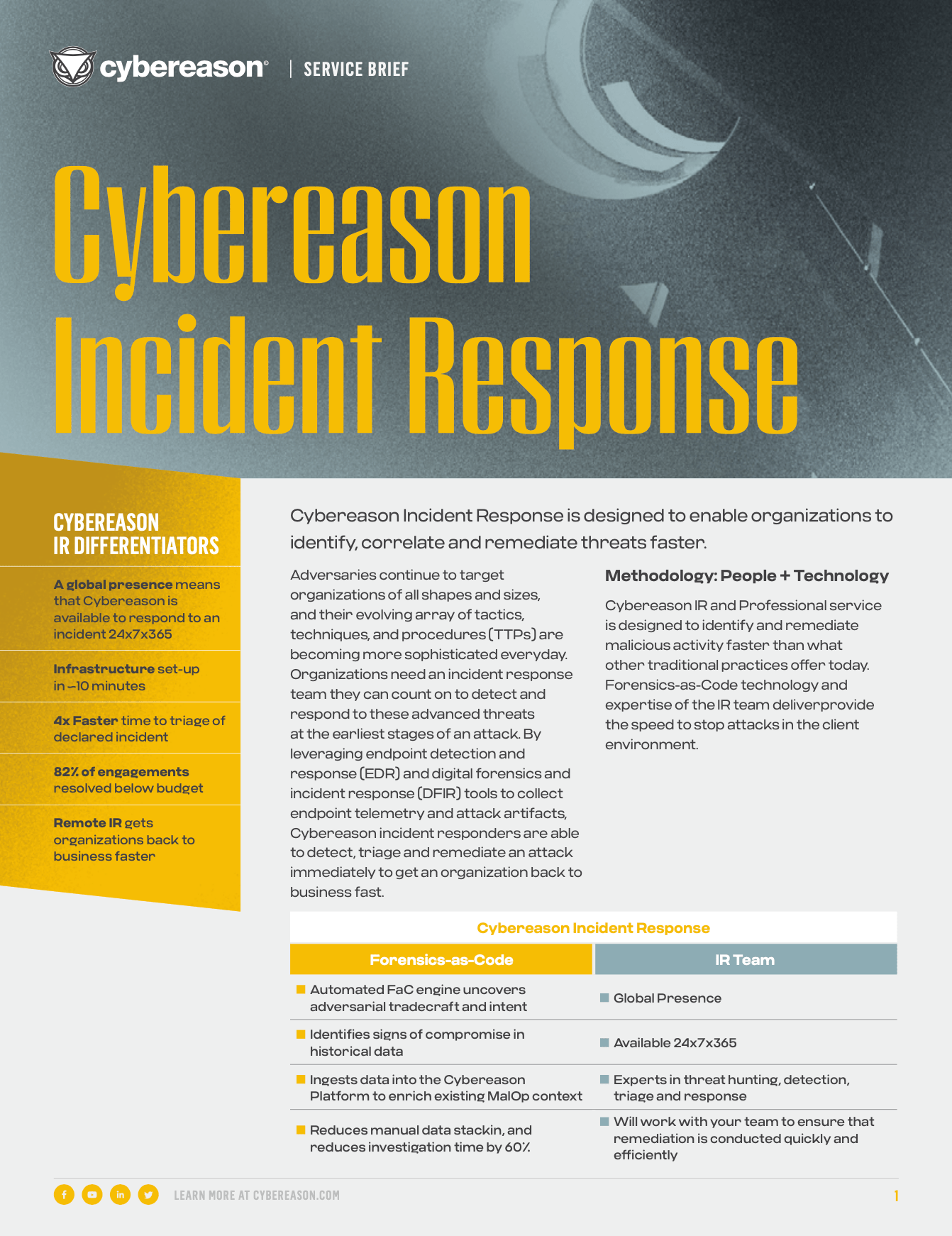
The Cybereason Defense Platform provides threat hunters with the tools and visibility needed to quickly detect, respond to, and remediate threats across the entire network.
Cybereason’s Nocturnus threat intelligence team delivers deep insights on the tools, techniques, and procedures of threat actors from around the world. This robust library of intelligence helps Cybereason Incident Responders identify, predict, and prevent the spread of an attack.
The Cybereason IR Team is comprised of threat hunters and security experts with decades of experience from some of the most respected organizations within both public and private sectors. A dedicated incident responder will be with you every step of the way from deployment through remediation.
Leveraging robust tools such as EDR, Forensics-as-Code, FaC and DFIR, Cybereason’s threat hunters deliver fast and efficient incident response that quickly restores back to business.
INCIDENT RESPONSE RESOURCES
Data Sheet
Compromise Assessment Data Sheet
Understand if your network has been breached
Read the Data SheetData Sheet
Cybereason IR & Professional Services
Learn more about Cybereason IR & Pro Services Bundles and Cybereason’s unlimited IR.
Read the Data Sheet