Security 101 Assessment
Analyze managed and unmanaged systems across the entire environment
Security 101 Assessment
Cybereason’s Security 101 Assessment service provides a security hygiene check of all managed and unmanaged systems to uncover weaknesses, vulnerabilities, and legacy tools and software that may leave organizations susceptible to an attack.
Identify Commonly Targeted Tools, Software, and Vulnerabilities
Discover surfaces that are commonly attacked by adversaries within the environment, identify vulnerabilities within those attack surfaces and proactively take steps to improve your security posture.
Hunt for targeted malware
The Cybereason Services Team will hunt for malware that may be specific to an industry or vertical, designed to run a specific course of action. Identifying targeted malware before it detonates will help organizations stop an attack in its tracks, preventing a breach before it can occur.
Network IT hygiene checks
A Security 101 Assessment will help organizations identify software running on endpoints that may introduce additional risk and security vulnerabilities, uncover commonly abused network services, and expose credentials in files, scripts and commands.
Customer Outcomes
Why Cybereason Services
The Cybereason Defense Platform provides threat hunters with the tools and visibility needed to quickly detect, respond to, and remediate threats across the entire network.
Cybereason’s Nocturnus threat intelligence team delivers deep insights on the tools, techniques, and procedures of threat actors from around the world. This robust library of intelligence helps Cybereason Incident Responders identify, predict, and prevent the spread of an attack.
The Cybereason IR Team is comprised of threat hunters and security experts with decades of experience from some of the most respected organizations within both public and private sectors. A dedicated incident responder will be with you every step of the way from deployment through remediation.
Leveraging robust tools such as EDR, Forensics-as-Code, FaC and DFIR, Cybereason’s threat hunters deliver fast and efficient incident response that quickly restores back to business.
INCIDENT RESPONSE RESOURCES
Data Sheet
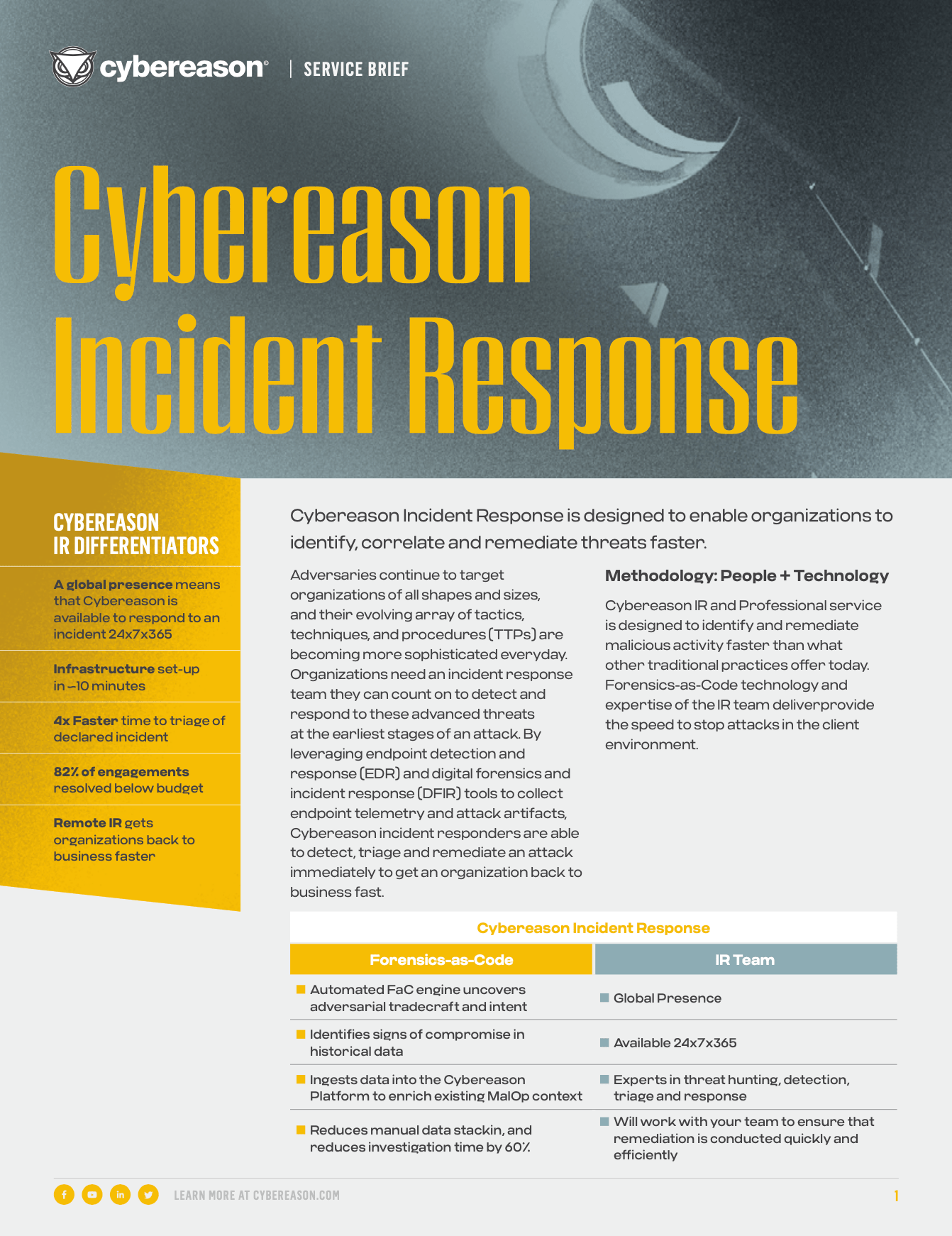
Cybereason Incident Response
Learn more about Cybereason’s Incident Response capabilities, services and deliverables.
Read the Data SheetData Sheet
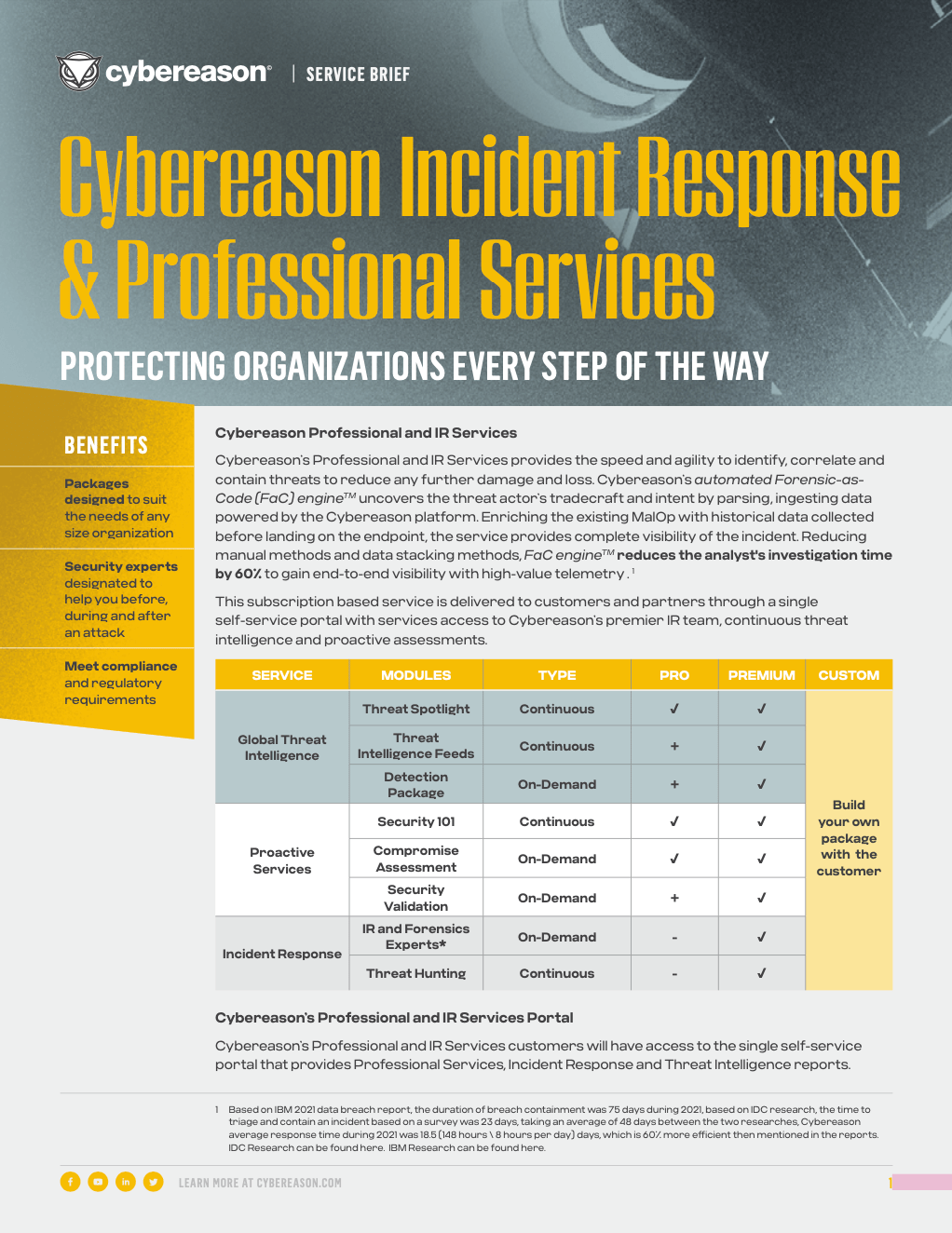
Cybereason IR & Professional Services
Learn more about Cybereason IR & Pro Services Bundles and Cybereason’s unlimited IR.
Read the Data Sheet