As we enter Q4 of a hyper-growth year for XDR, Cybereason is in full gear: We’re just getting started! We remain undefeated in protecting our customers from headline-stealing attacks like SolarWinds, the Microsoft Exchange Server attacks, and dangerous ransomware attacks from DarkSide, REvil and other adversaries.
Today, we’re proud to announce that the AI-driven Cybereason XDR has been named a Contender in the debut of the The Forrester New Wave™: Extended Detection and Response (XDR) Providers, Q4 2021, continuing the company’s tremendous momentum in the XDR space following the acquisition of security analytics company empow. In addition, following the XDR New Wave evaluation cycle, Cybereason and Google Cloud announced a strategic partnership to bring a unified, planetary-scale XDR solution to market in 2021.
Cybereason XDR was one of only 14 solutions included in this first ever XDR report from Forrester, which we believe is a testament to our ability to prevent high-impact attacks, accelerate incident response, and simplify investigations and threat hunting, from the endpoint to across the enterprise.
In addition to top-tier product talent and 70+ IT & security integrations, our empow acquisition brings Prediction algorithms, capable of anticipating an attacker’s likely next steps through machine learning models applied to XDR data. This intelligent decision engine highlights areas of risk and suggests proactive prevention and response actions to take:
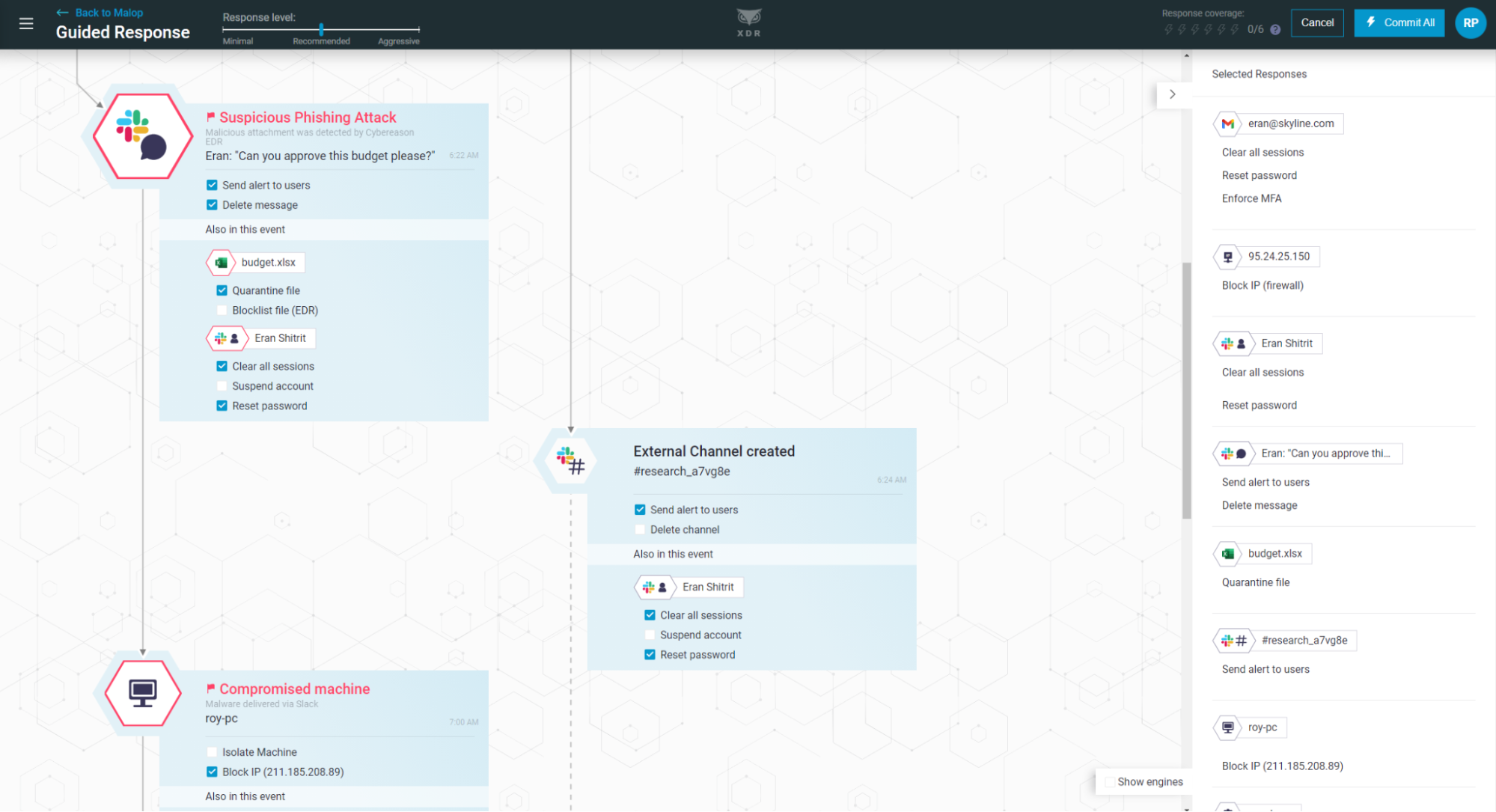 Cybereason Defense Platform MalOp Display
Cybereason Defense Platform MalOp Display
Cybereason XDR provides a novel way to manage security operations by visualizing key stages of a MalOp™ (malicious operation). This includes root cause, any affected users & assets, a full timeline of the incident, suggested response actions, and attack predictions. Cybereason XDR leverages the power of the Cybereason Defense Platform in combination with our SOCs who conduct proactive monitoring and threat hunting around the clock and across the globe.
Inclusion in this debut XDR report from Forrester follows:
Why Extended Detection and Response?
Our employees, IT infrastructure, and data are more dispersed than ever before. As security leaders, it’s now essential we extend protection beyond our corporate assets and networks to identities, applications -- wherever our employees and critical data reside.
The traditional defense stack includes tens of tools and technologies, each monitoring and protecting an important facet of the environment: Endpoint Detection and Response, Firewall, Email Protection, Identity Protection:
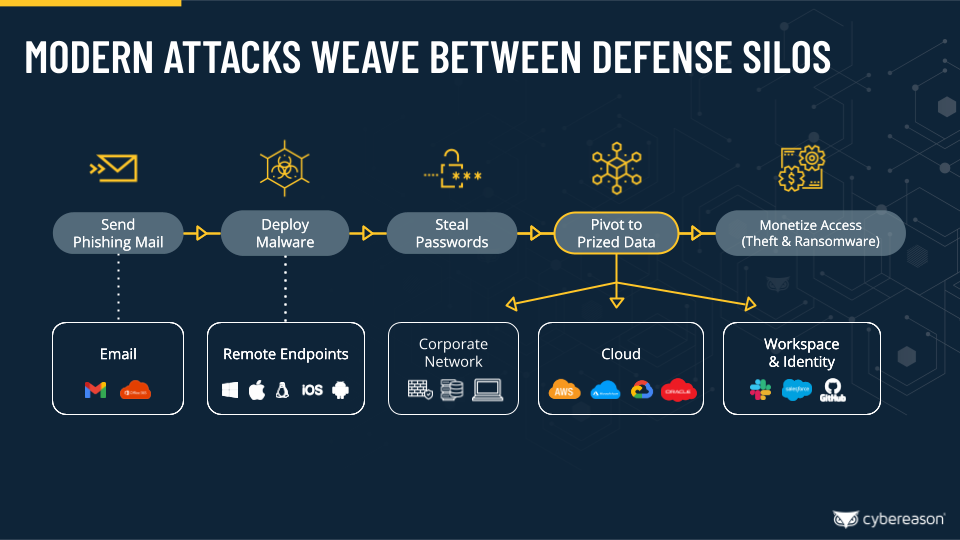 Malicious Operations Attack Kill Chain
Malicious Operations Attack Kill Chain
Then, key events and data get centralized into a SIEM for investigation, and then off to a SOAR tool for orchestration and response. The challenge is, running this type of stack is expensive to build and maintain, it requires skilled operators to run (and the work isn’t fun), and ultimately, it’s still a step behind the attacker in terms of response times and ending a malicious operation.
The promise of the XDR market is a better way. By combining Google’s petabyte-scale infrastructure and Google Cloud data engine with Cybereason’s best-of-breed MalOp (malicious operation) engine for threat detection and response, our XDR offering is able to provide:
-
- Planetary-Scale Protection: Out-of-the-box, prevent ransomware and other high-impact attacks across your complete environment.
- Multi-Layer Response: Guided and automated response capabilities accelerate response times and end the complete attack operation.
- Attack Predictions: Through an operation-centric approach, XDR can predict likely next steps for any attack chain. This reduces human error and helps prioritize future areas of risk.
At Cybereason, we’re dedicated to teaming with Defenders to end cyber attacks from endpoints to the enterprise to everywhere. Learn more about AI-driven Cybereason XDR here or schedule a demo today to see how your organization can benefit from an operation-centric approach to security.



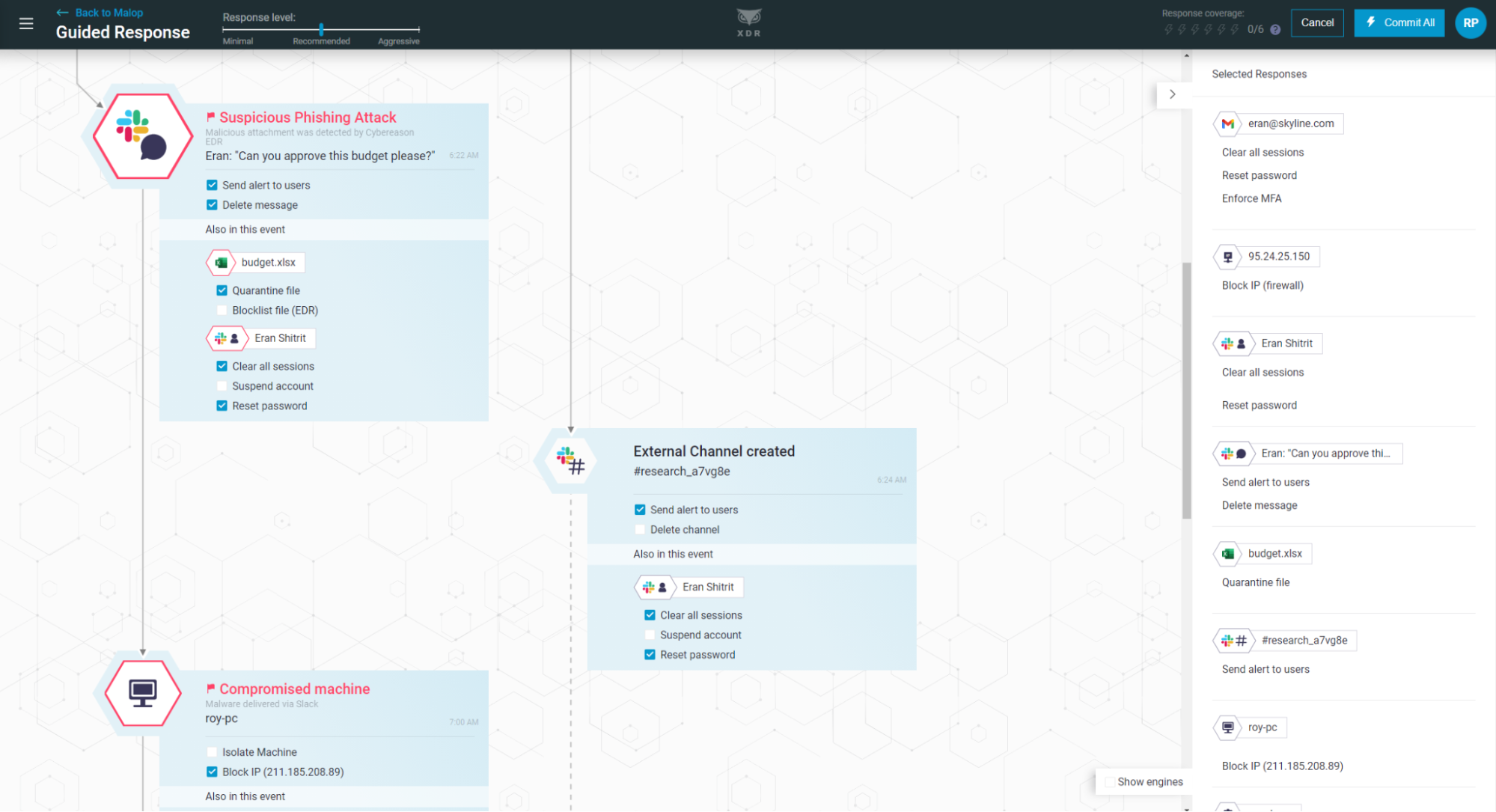 Cybereason Defense Platform MalOp Display
Cybereason Defense Platform MalOp Display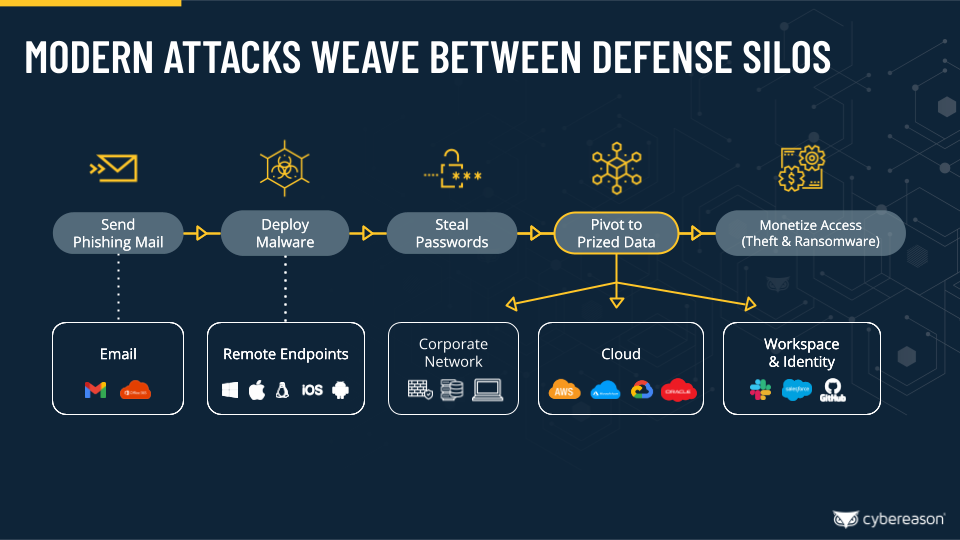 Malicious Operations Attack Kill Chain
Malicious Operations Attack Kill Chain
.png)