MITRE ATT&CK: Wizard Spider and Sandworm Evaluations Explained
MITRE is the preeminent third-party security solution evaluator. We explain the key metrics to look for in their upcoming Enterprise ATT&CK Evaluation...
Aoibh Wood
Adversary emulation plans (AEPs) are the way to model adversary behavior based on a particular set of TTPs in MITRE ATT&CK. For example, MITRE has created an AEP for APT3 to showcase exactly how APT3 compromises a system and exfiltrates sensitive information. Security teams use AEPs to create attack simulations based on specific adversaries to test their defense.
Though AEPs are especially important when testing and building a strong defense, they are often overlooked for TTPs by security practitioners versed in the “trench warfare” of day-to-day security operations. Though TTPs are useful in their own right, they are much more effective when coupled with AEPs.
In fact, our team finds that AEPs are the most important feature when constructing an effective operational security effort tailored to your business. While TTPs may change, the general process of bringing TTPs together into a real-world attack simulation whose efficacy can be measured is the real gem. AEPs bring TTPs into a measurable attack simulation based on a specific, real-world adversary for specific, real-world improvements.
Your red team can use AEPs to develop an attack simulation and execute it against your enterprise security infrastructure. These simulations leverage real-world attacks so you can identify and tune gaps in your defense before the actual adversary strikes. They also help reduce your security team load and give them greater visibility into their environment.
For the most significant results, turn this process into a monthly or yearly activity to consistently strengthen and tune your defense over time.
AEPs are made up of several sections, including an overview of the plan, an overview of the adversary group, a detailed listing of the emulation phases, and a biography of sources.
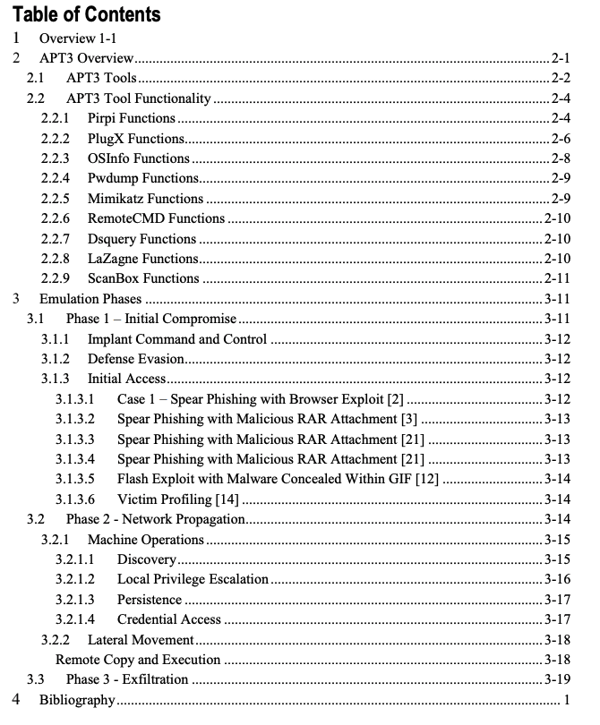
Figure 5: The components of a thorough AEP, from the MITRE ATT&CK APT3 example AEP.
You can find a guide for creating an AEP and an example AEP from MITRE ATT&CK. This example AEP is a great template for teams starting their first adversary emulation.
The overview of the APT is a detailed description of the adversary group and the tools they are known to use. This is a useful section to reference later in the emulation phases, when the red team is outlining how to emulate the adversary group.
When constructing an adversary emulation plan, it’s best to start with known adversary groups that target your organization or industry.
One of the most critical components of a detailed AEP is the section on Emulation Phases. The Emulation Phases section is a specific, detailed breakdown of the tactics of the adversary group.
In order to construct the Emulation Phases, your red team must identify the tactics the adversary group uses for an attack, along with the particular techniques and procedures for each tactic. Much of this information is available in MITRE ATT&CK.
To detail an emulation phase in the AEP, your red team must note the tools they will use to emulate the particular TTP. This information is available as part of the MITRE ATT&CK description of the adversary group, and more detailed information can be found through a simple Google search of the vulnerability exploited or attack methodology. The more detailed your red team is able to make the phase, the better. Ideally, they will also include the detection step in the AEP. Each emulation phase should be constructed individually and compiled together in the AEP.
A detailed and complete AEP is a good resource that newer L1 analysts can use to learn about specific attacks and the security tools they will be working with. A great example of this is Cybereason Nocturnus, who regularly releases detailed research so red teamers and others in the community can learn the exact processes of the most popular adversary groups.
To learn more about how to use MITRE ATT&CK to enhance SecOps, download the white paper.

Aoibh Wood, Senior Director of Partner Service Delivery, has 30+ years of technology industry experience. During the last 14 years, she has provided forensics and incident response support for US Federal and state organizations and as well as Fortune and Global 100 companies.
All Posts by Aoibh Wood
MITRE is the preeminent third-party security solution evaluator. We explain the key metrics to look for in their upcoming Enterprise ATT&CK Evaluation...
The MITRE ATT&CK evaluations test security vendors’ ability to quickly detect and stop tactics and techniques used by today’s threat actors. In this webinar, we strip down the complexity of the MITRE ATT&CK framework so your organization can leverage it for success...
MITRE is the preeminent third-party security solution evaluator. We explain the key metrics to look for in their upcoming Enterprise ATT&CK Evaluation...
The MITRE ATT&CK evaluations test security vendors’ ability to quickly detect and stop tactics and techniques used by today’s threat actors. In this webinar, we strip down the complexity of the MITRE ATT&CK framework so your organization can leverage it for success...
Get the latest research, expert insights, and security industry news.
Subscribe