
THREAT ALERT: DarkGate Loader
The execution of DarkGate Loader ultimately leads to execution of post-exploitation tools such as Cobalt Strike and Meterpreter. This Threat Alert provides an overview of an attack involving DarkGate Loader.

Cybereason Global SOC Team
The Cybereason Global Security Operations Center (SOC) issues Cybereason Threat Alerts to inform customers of emerging impacting threats. The Alerts summarize these threats and provide practical recommendations for protecting against them.
The GSOC Cybereason Managed Detection and Response (MDR) Team is investigating a series of recent infections that use the SolarMarker backdoor. SolarMarker enables attackers to execute commands, PowerShell scripts, and Windows executables on compromised systems, and to deploy additional malware. The malware author uses the .NET framework to implement SolarMarker.
A SolarMarker infection exhibits the following malicious activity:
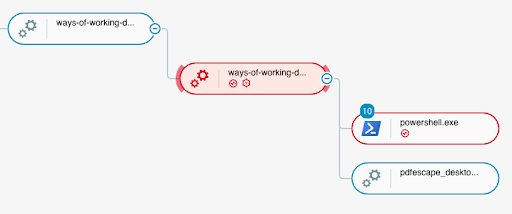 The .tmp file (ways-of-working-document-template.tmp) executes PowerShell code and a legitimate installer file (pdfescape_desktop_installer.exe)
The .tmp file (ways-of-working-document-template.tmp) executes PowerShell code and a legitimate installer file (pdfescape_desktop_installer.exe)
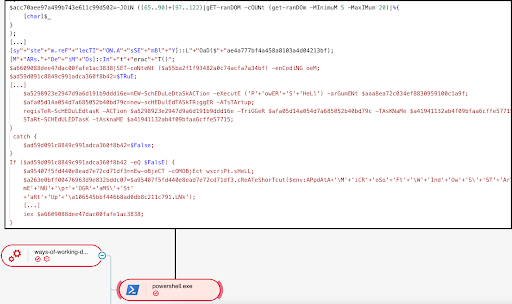 Execution of the decrypted PowerShell code
Execution of the decrypted PowerShell code
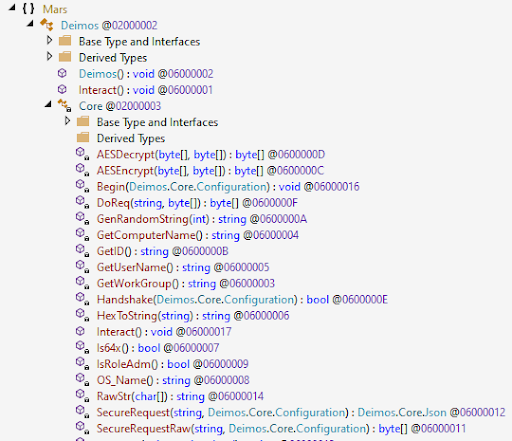 Functions implemented as part of the reflectively loaded .NET assembly, including [Mars.Deimos]::Interact
Functions implemented as part of the reflectively loaded .NET assembly, including [Mars.Deimos]::Interact
Cybereason recommends the following:
Aleksandar Milenkoski, Senior Threat and Malware Analyst, Cybereason Global SOC
 Aleksandar Milenkoski is a Senior Threat and Malware Analyst with the Cybereason Global SOC team. He is involved primarily in reverse engineering and threat research activities. Aleksandar has a PhD degree in the area of system security. Prior to Cybereason, his work was focusing on research in the area of intrusion detection and reverse engineering security mechanisms of the Windows 10 operating system.
Aleksandar Milenkoski is a Senior Threat and Malware Analyst with the Cybereason Global SOC team. He is involved primarily in reverse engineering and threat research activities. Aleksandar has a PhD degree in the area of system security. Prior to Cybereason, his work was focusing on research in the area of intrusion detection and reverse engineering security mechanisms of the Windows 10 operating system.
Eli Salem, Senior Security Analyst, Cybereason Global SOC
 Eli Salem is a lead threat hunter and malware reverse engineer at Cybereason. Eli has worked in the private sector of the cyber security industry for a couple of years now. In his free time he publishes articles about malware research and threat hunting.
Eli Salem is a lead threat hunter and malware reverse engineer at Cybereason. Eli has worked in the private sector of the cyber security industry for a couple of years now. In his free time he publishes articles about malware research and threat hunting.

The Cybereason Global SOC Team delivers 24/7 Managed Detection and Response services to customers on every continent. Led by cybersecurity experts with experience working for government, the military and multiple industry verticals, the Cybereason Global SOC Team continuously hunts for the most sophisticated and pervasive threats to support our mission to end cyberattacks on the endpoint, across the enterprise, and everywhere the battle moves.
All Posts by Cybereason Global SOC Team
The execution of DarkGate Loader ultimately leads to execution of post-exploitation tools such as Cobalt Strike and Meterpreter. This Threat Alert provides an overview of an attack involving DarkGate Loader.

A Microsoft Office code execution vulnerability dubbed “Follina” allows delivery of malware without needing the victim to allow macro execution and is very likely to be mass-exploited. The Cybereason Defense Platform detects and prevents the exploitation of Follina and enables effective hunting of this vulnerability...

The execution of DarkGate Loader ultimately leads to execution of post-exploitation tools such as Cobalt Strike and Meterpreter. This Threat Alert provides an overview of an attack involving DarkGate Loader.

A Microsoft Office code execution vulnerability dubbed “Follina” allows delivery of malware without needing the victim to allow macro execution and is very likely to be mass-exploited. The Cybereason Defense Platform detects and prevents the exploitation of Follina and enables effective hunting of this vulnerability...
Get the latest research, expert insights, and security industry news.
Subscribe