The Cybereason Nocturnus Team has identified an active campaign targeting customers of a larger e-commerce platform with newly identified multi-stage malware that evades antivirus tools dubbed Chaes.
The info-stealing malware is designed to harvest sensitive consumer information, including login credentials, credit card numbers and other financial information. The full report can be downloaded here (ungated).
 E-commerce platforms have been a favored target for cybercriminals, and the sharply increased volume of online shopping spurred by the COVID-19 pandemic have made attacks potentially even more profitable.
E-commerce platforms have been a favored target for cybercriminals, and the sharply increased volume of online shopping spurred by the COVID-19 pandemic have made attacks potentially even more profitable.
According to data from the recent IBM U.S. Retail Index released in August of this year, “the pandemic has accelerated the shift away from physical stores to digital shopping by roughly five years,” and “e-commerce is projected to grow by nearly 20% in 2020” (TechCrunch).
The Cybereason Nocturnus Team has been tracking threat actors leveraging the previously undetected Chaes malware to primarily target Brazilian customers of the largest e-commerce company in Latin America, MercadoLivre.
The researchers noted that the Latin American cybercrime scene has evolved a great deal in recent years, with some of the more notorious malware variants gaining prominence in just the last year, including Grandoreiro, Ursa and Astaroth.
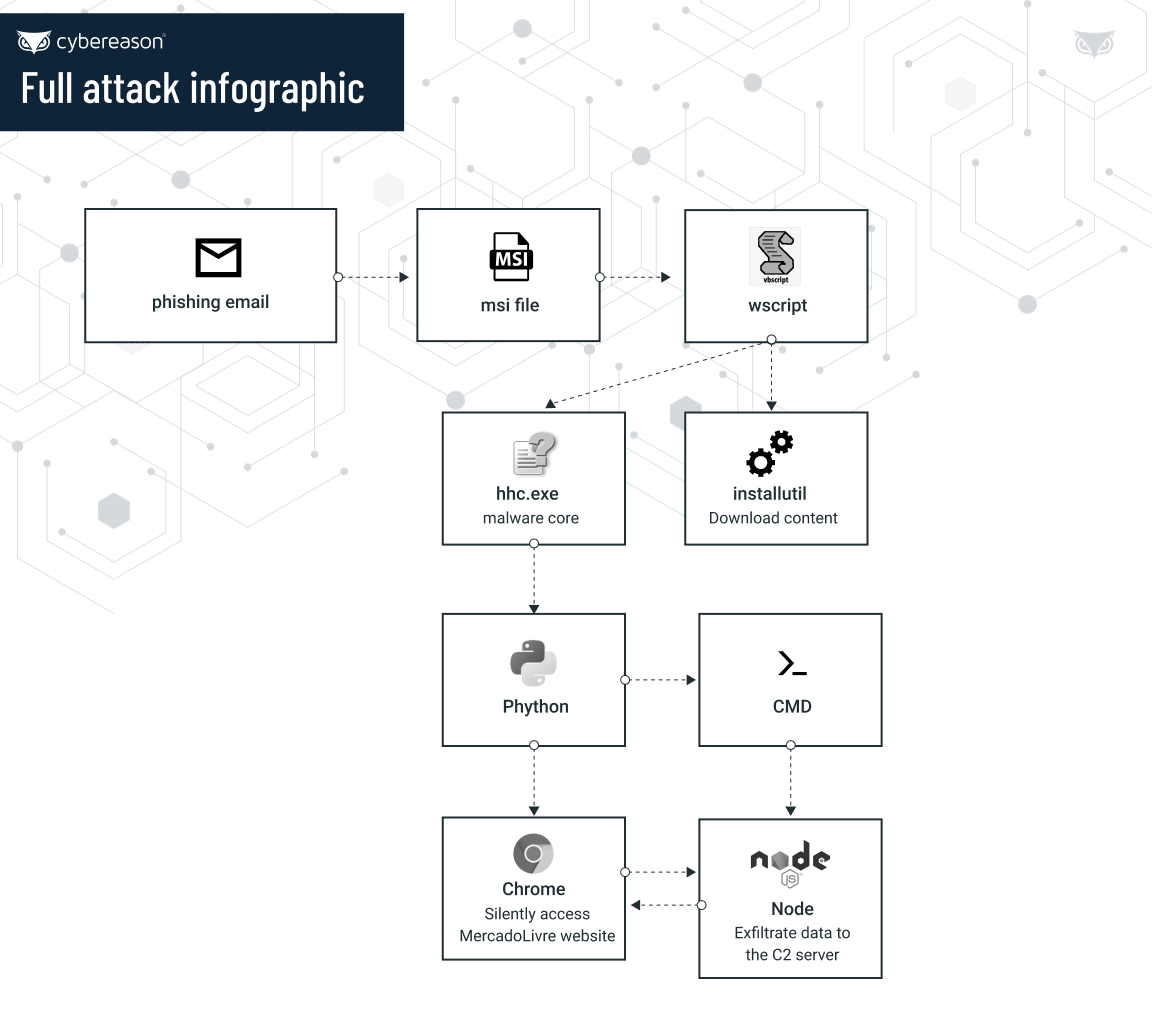
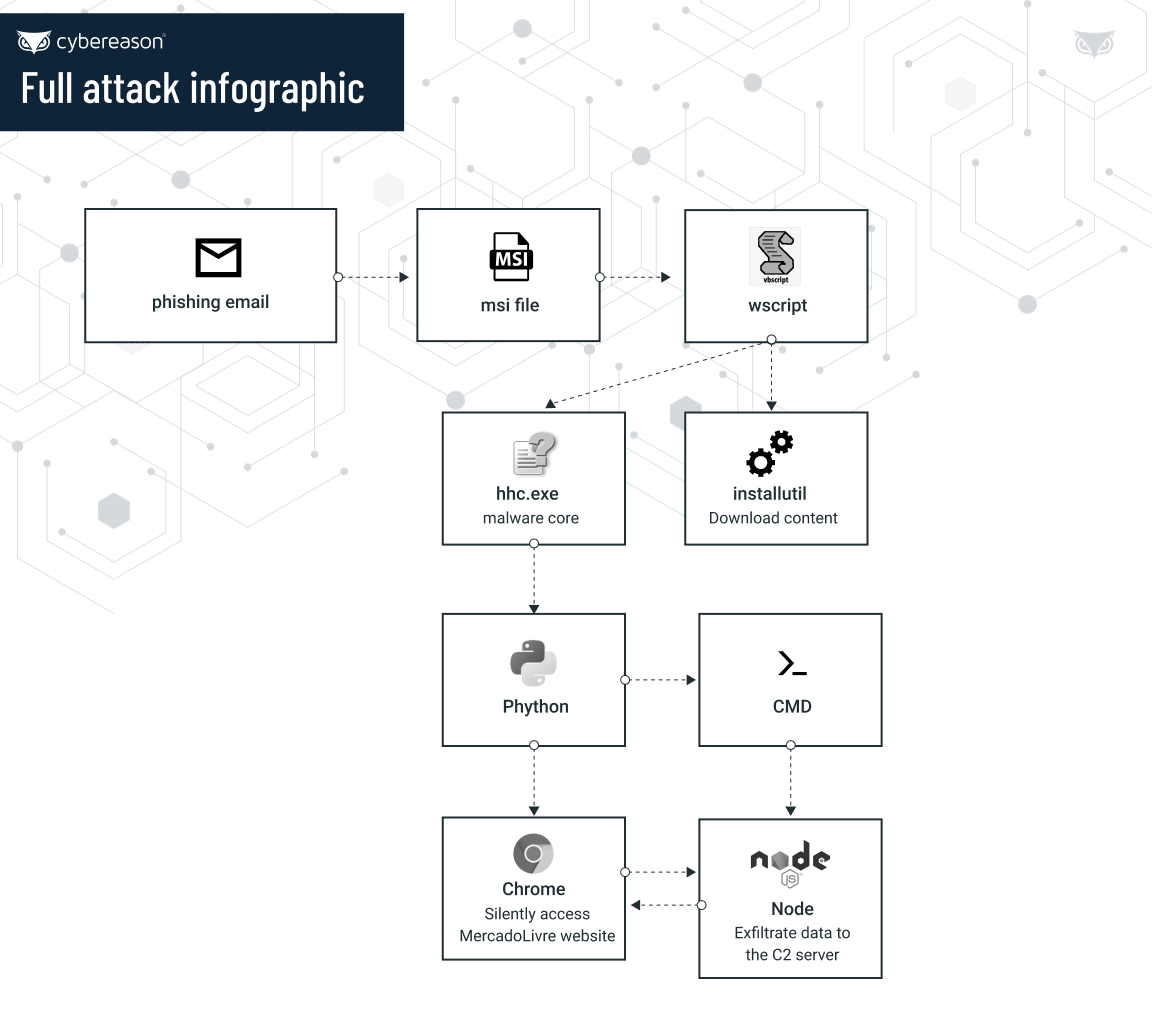
These Latin American operations typically demonstrate some unique features when it comes to the tactics, techniques and procedures (TTPs) employed, as well as how the malware is propagated to infect victims. These trends include the use of .MSI files as an initial way to start the infection chain, the use of Delphi as the preferred language to code the malware, extensive use of LOLBins to execute content, and the downloading of legitimate tools to expand the malware’s capabilities and aid in evasion of antivirus software.
Key Findings:
Targeting the Biggest E-Commerce Company in Latin America: Chaes specifically targets the Brazilian website of e-commerce company MercadoLivre and its payment page MercadoPago to steal its customers’ financial information. The final payload of Chaes is a Node.Js information stealer that exfiltrates data using the node process.
Credential Stealing, Screen Capture, Browser Monitoring, Reconnaissance: Chaes is designed to steal sensitive information from the browser such as login credentials, credit card numbers, and other financial information from MercadoLivre website customers. Chaes also takes screenshots of the infected machine, hooks and monitors the Chrome web browser to collect user information from infected hosts.
Multistage Delivery, Multi-Language Malware: Chaes infections consist of several stages that include use of LoLbins and other legitimate software, making it very challenging to detect by traditional antivirus tools. Chaes also executes multiple stages and is written in several programming languages including Javascript, Vbscript, .NET , Delphi and Node.js.
Downloads Legitimate Software, Designed for Stealth: Chaes operates using legitimate tools such as Python, Unrar and Node.js, and functional stages consist of several techniques such as use of LoLbins, open source tools, fileless actions and use of legitimate node.js libraries designed to increase the malware’s stealthiness.
“Threat actors put a great deal of time, resources and effort into choosing their targets for criminal operations such as this, and a return on their investment is always top of mind. Undoubtedly, the dramatic increase in the volume of online shopping transactions has not escaped their notice, so it’s not surprising to see new and ever-more sophisticated malware variants emerging to take advantage of the current circumstances,” said Lior Div.
“Individuals should be vigilant when it comes to cyber hygiene to avoid malware infections in general, and should maintain situational awareness when engaged in online shopping or banking to avoid becoming the victim attackers trying to take advantage of the pandemic and the recent increase in online financial activities.”
The full report, titled Chaes: Novel Malware Targeting Latin American E-Commerce, is available for download HERE.
Eli Salem


Eli Salem, Lead Threat Hunter and Malware Reverse Engineer at Cybereason, enjoys improving the methodologies for the threat hunting team through his knowledge of relevant security industry incident response frameworks, such as MITRE ATT&CK. He also conducts research on advanced threat actors and their Tools, Techniques, and Procedures (TTPs).




 E-commerce platforms have been a favored target for cybercriminals, and the sharply increased volume of online shopping spurred by the COVID-19 pandemic have made attacks potentially even more profitable.
E-commerce platforms have been a favored target for cybercriminals, and the sharply increased volume of online shopping spurred by the COVID-19 pandemic have made attacks potentially even more profitable.