Log4Shell is a vulnerability (CVE-2021-44228) impacting Apache Log4j which was disclosed on the project’s GitHub on December 9, 2021. The flaw has the highest possible severity rating of 10 and is pervasive.
Cybereason has completed verification that this issue does not affect Cybereason products or services. Furthermore, Cybereason researchers released a "vaccine” for Log4Shell that is freely available, providing defenders with a relatively simple temporary workaround that requires only basic Java skills to implement and gives organizations some level of protection while they complete due diligence in the patching process.
If you believe your organization has potentially been compromised through the exploitation of CVE-2021-44228, please contact the Cybereason Incident Response Team.
Prevent Attacks Leveraging Log4Shell
In addition to ensuring all of your systems are protected by Cybereason, we also continue to advise on remediation for the Log4Shell vulnerability directly, either through the vaccine released by Cybereason or through the manual remediation steps detailed at the end of this blog.
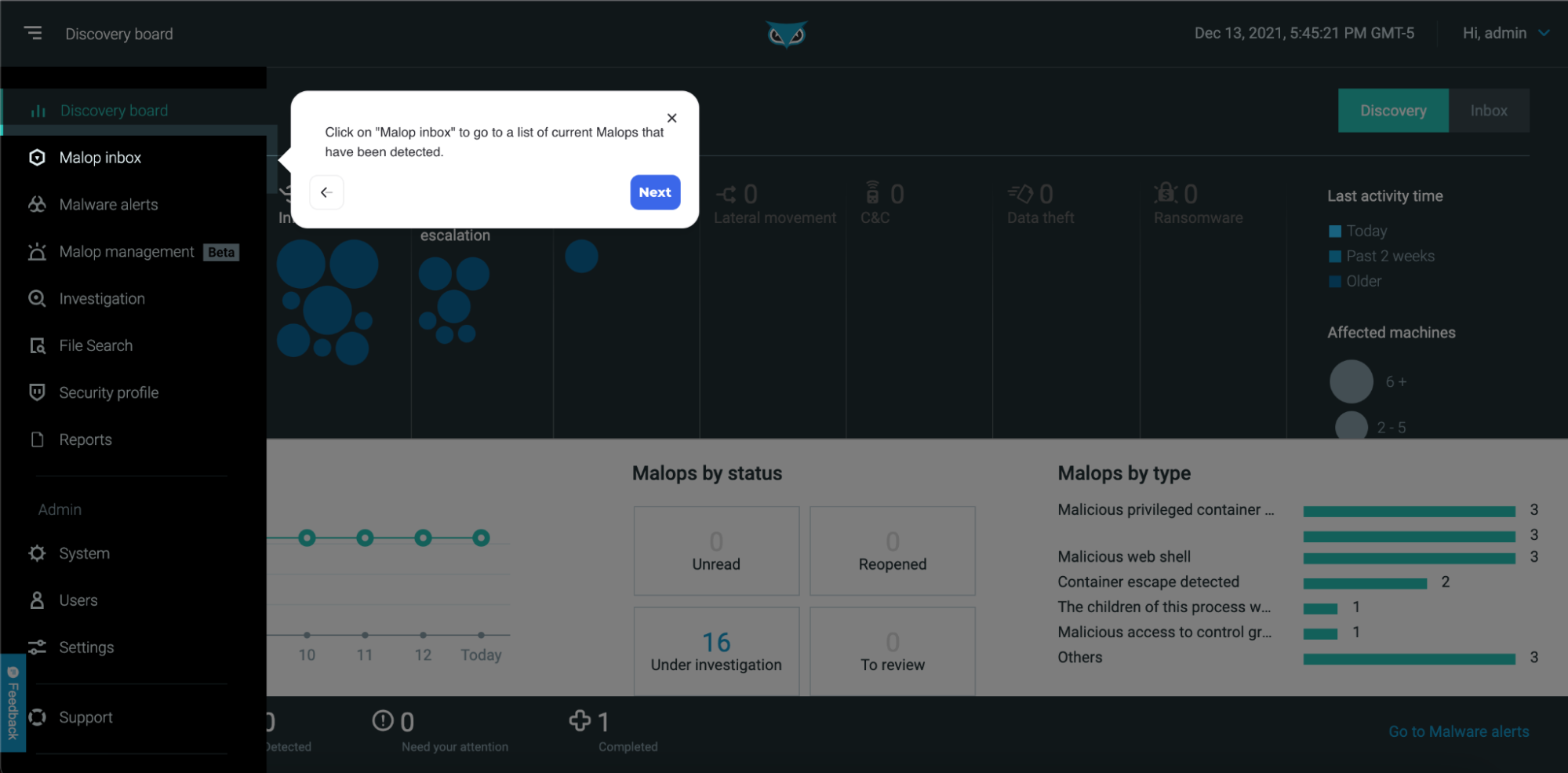
In the interactive demonstration linked below, you can walk through an active MalOp™ where a Tomcat server has been compromised as a result of the Log4Shell vulnerability and the attacker is able to deploy a malicious webshell. Upon completion of the investigation, you will remediate the threat from within the AI-driven Cybereason XDR Platform.
In this walkthrough, Prevention features were disabled to show the depth of the detection process; however, enabling the Prevention feature would have blocked the execution of the malicious webshell demonstrated as part of the Cybereason multilayered defense:
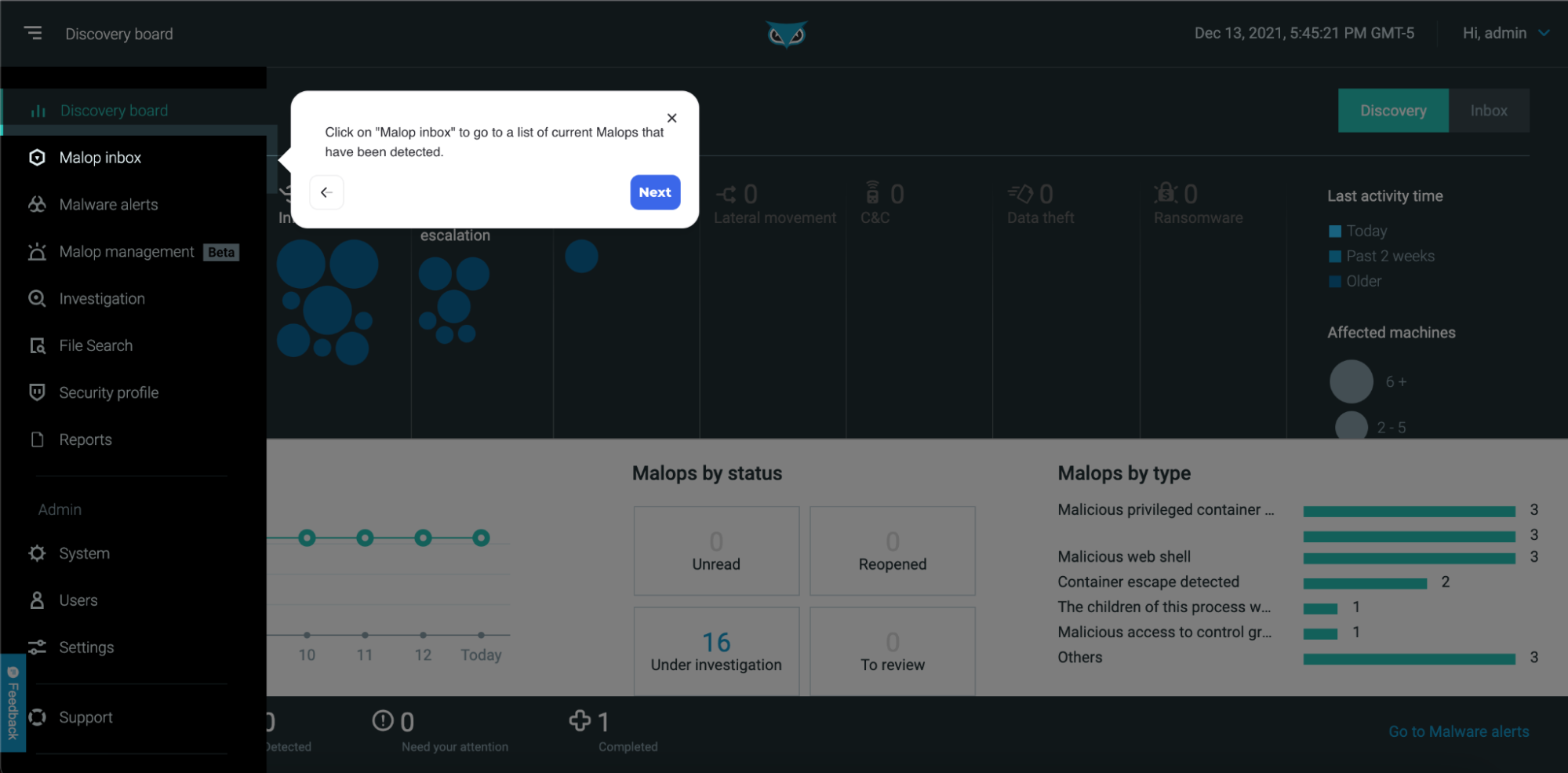
You can view a complete demo illustrating how the Cybereason XDR Platform can uncover malicious activity resulting from the exploitation of the Log4Shell vulnerability HERE.
Threat Hunting for Log4Shell Activity
In the event that you have identified potentially impacted systems that were not running Cybereason, or if you have recently deployed Cybereason as part of your incident response, we recommend threat hunting in your environment for malicious activity resulting from the exploitation of this vulnerability.
Cybereason customers can use the following queries by attaching the query to the Cybereason URL like so: customer.cybereason.net/[paste hunt query here]:
- Java processes with incoming connections on LDAP ports: /#/s/search?queryString=0<-Process"name:%3Djava"->connections"serverPort:%3D3268%7C389%7C636"
- Bash or SH processes spawning on Linux hosts from web server processes: /#/s/search?queryString=1<-Machine"osType:%3DLINUX"->processes"name:%3Dapache%7Capache2%7Chttpd%7Cjava%7Cjavaw"->children"elementDisplayName:%3Dbash%7Csh"
-
- Connections to IOCs confirmed in exploitation of the vulnerability:
/#/s/search?queryString=4<-Connection->remoteAddress"elementDisplayName:$45.155.205.233%7C44.240.146.137%7C45.137.155.55%7C185.154.53.140%7C185.191.32.198%7C44.240.146.137%7C45.137.155.55%7C185.154.53.140%7C185.191.32.198"->Connection.remoteAddress->ownerProcess->children
-
- Find applications that use Log4j2:
/#/s/search?queryString=0<-Process"commandLine:@Log4j2"&sorting=creationTime&sortingDirection=-1&viewDetails=false
First to Your Fight
Cybereason is dedicated to teaming with Defenders to end cyber attacks from endpoints to the enterprise to everywhere. Learn more about Cybereason XDR powered by Google Chronicle, check out our Extended Detection and Response (XDR) Toolkit, or schedule a demo today to learn how your organization can benefit from an operation-centric approach to security.
About the Authors:
 Ken Westin
Ken Westin
Ken Westin is Director of Security Strategy at Cybereason. Ken has been in the security field for over 15 years, working with companies to bolster their security posture through threat hunting, insider threat programs and vulnerability research. In the past, he has worked closely with law enforcement, helping to unveil organized crime groups. His work has been featured in Wired, Forbes, New York Times, Good Morning America and others, and he is regularly reached out to as an expert on cybersecurity, cybercrime and surveillance.
 Justin Buchanan
Justin Buchanan
Justin Buchanan, Director of Product Marketing, is responsible for the go-to-market strategy of Cybereason’s Endpoint Protection Platform (EPP) offerings. Driven by his background in IT and his deep understanding of customers’ desired outcomes, Justin is passionate about how Cybereason can help customers—and the security industry as a whole—reverse the adversary advantage and empower defenders.



 Ken Westin
Ken Westin Justin Buchanan
Justin Buchanan
