What is Next-Generation Antivirus (NGAV)?
Next-generation antivirus (NGAV) is a new breed of software that was created to bridge the gap left by traditional antivirus.
What exactly constitutes NGAV in the cybersecurity industry is still unclear since there’s not a widely-accepted definition for the term. At a minimum, next-generation antivirus products need to go beyond performing signature-based detection while also incorporating some type of advanced technology.
Most NGAVs go beyond the use of indicators of compromise (IOCs) and metadata such as virus signatures, IP addresses, file hashes, and URLs. Using technologies like advanced data science, machine learning, artificial intelligence and data analytics, next-generation antivirus solutions look for patterns of behavior used by attackers to discover tactics, techniques, and procedures (TTPs).
What is Traditional Antivirus?
Antivirus (AV) software were designed to detect malicious programs, prevent them from executing, and remove them.
An antivirus product includes a library of known, static malware characteristics that needs to be continuously updated in order to remain up-to-date with the thousands of new malware created daily. They scan files and directories, comparing them to this library, and label malicious programs when matches are found. The antivirus will then prevent these programs from running and automatically remove them, or offer the user an option for removal.
As long as the antivirus version on the endpoints is updated by the user and the vendor continuously keeps their library current, the user is presumably protected. But, again, they are only protected by older, known malware that can be detected and blocked.
Can NGAV Replace Traditional Antivirus?
Depending on an organization’s specific use cases and their current antivirus solution, it is possible to replace traditional-based antivirus with NGAV. Protection is still needed from known threats, so NGAV solutions suited to be replacements would need to still perform signature-based threat detection. Also, some organizations need to follow industry-specific regulations like PII and HIPAA, so any acceptable antivirus replacement must meet relevant compliance guidelines.
How Should NGAV Solutions be Assessed?
There are many criteria that can be used when assessing an NGAV solution. In light of the current attack landscape, we believe that a few specific characteristics should be prioritized during any assessment, below.
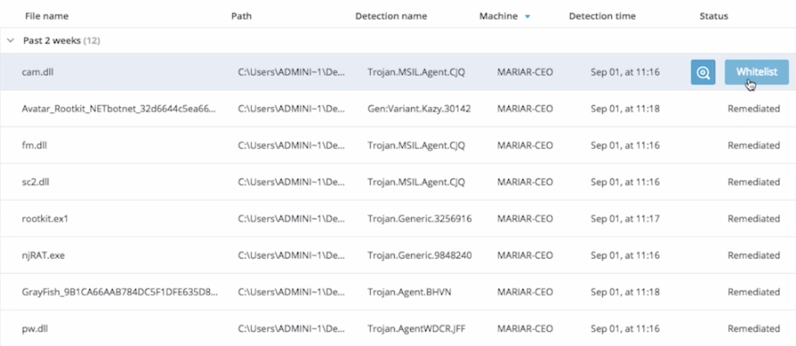
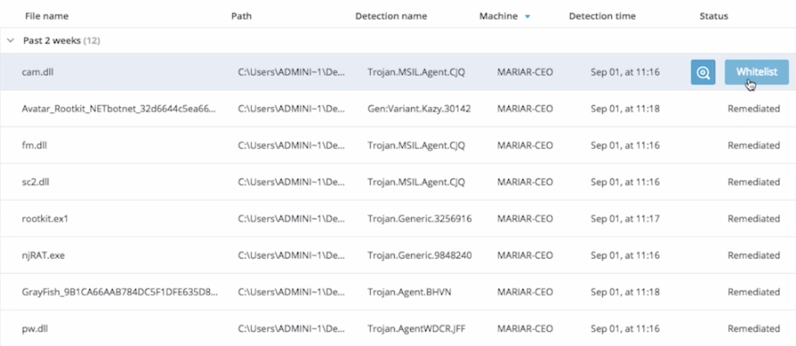
Level of False Positives
NGAV software attempts to identify never-before-seen malware and protect against it. This is a harder, less definitive task that tends to generate a high volume of false positives. When testing NGAV, go beyond the malware provided by the NGAV vendor and check the configuration to assess the product's real-life false positive rate.
Protection Against New Malware
An effective NGAV employs advanced machine learning, data analysis and AI to identify new attack methodologies, define them as malicious and protect against them. When possible, it is highly recommended to test the abilities of the considered tool against a set of advanced threats.
Additionally, we estimate that about half of today's attacks use fileless malware techniques, which utilize Windows scripting languages like PowerShell. Since these scripting languages are used heavily by IT admins during their daily duties, avoid any NGAV solutions that take blacklisting/whitelisting approach.
Protection Against New Ransomware
It is critical for an NGAV solution to use effective mechanisms to protect against new ransomware strains, including ones that encrypt the Master Boot Record, such as NotPetya.
Should NGAV be Combined with EDR?
The ultimate endpoint security platform is the one formed by combining NGAV, for upfront blocking of malicious execution, with an endpoint detection and response (EDR) for detecting and responding to malicious activities that may bypass the antivirus.
EDR provides the context that NGAV cannot. An NGAV analyzes behavior on a single endpoint, while EDR platforms brings in data from across the enterprise, collecting data from all endpoints. This combination enables organizations to see behaviors that cannot be spotted by NGAV, such as lateral movement of an attacker inside their network.
In addition, the combination of NGAV with EDR helps minimize the amount of false positives issued by an NGAV alone, as the full enterprise context brought by an EDR helps determine if abnormal-but-benign behaviors are actually malicious.
To learn more about how Cybereason combines EDR and NGAV and improves threat intelligence, watch our video below: