TRANSCRIPT:
China's Unrestricted Cyberwarfare Part 1
What is cyberwar?
It’s such a trendy term these days that it’s hard to tell. On the news, you hear that the U.S. is in a cyber war with Russia, or with China, or with Iran. Russia is in a cyber war with the U.S., and Ukraine, and half the continent of Europe. And there’s China, and Israel, and…
Who cares? Seriously, if Russia hacks into the U.S. Department of Things That Don’t Concern Me, or into some politician’s emails, does it even matter? It doesn’t seem like war. Remember real war? You could get shot in a real war. Cyber wars seem kind of sucky in comparison.
“[Nate] I was thinking about this, recently, after a discussion I had with Bill Hagestad.”
BILL HAGESTAD
“[Hagestad] Yes. Good day! My name is Bill Hagestad, a Retired Lieutenant Colonel of the US Marine Corps, served almost three decades serving our country, a couple of tours in Iraq.”
Bill has a different kind of view on what cyberwar is all about. To get the full picture, you have to understand where he’s coming from.
“[Nate How would you describe your relationship with the Chinese government because I have trouble doing so?
[Hagestad] [Laughs] Yes. I make – I’m very transparent about it. I am actually a visiting scholar at the People’s Liberation Army’s number one think tank out of Jiangsu Province in the People’s Republic of China known as the Knowfar Institute.”
The number one think tank for the PLA. A place no Westerner should be allowed within 1,000 yards of.
“[Nate] And I mean no offense when I ask, what did the Chinese gain by keeping you around but find you over and whatnot?
[Hagestad] Well, what the Chinese gain is more historical than it is anything pre-issued. Since I am what is called considered a laowai or an old China hand, since I have visited China in 1981, many – ’83, many of the Chinese military and civilians that I interact with we’re not even born.”
China in the early ‘80s was vastly different than it is today. The Mao era had ended, and under the leadership of Deng Xiaoping the country was beginning to lighten up. This was before Tiananmen Square—a kind of sweet spot between the old authoritarian regime and the current one.
“[Hagestad] going back to 1983, I actually had to apply to the Headquarters Marine Corps to go visit. I said, “Hey, this would be a great opportunity. Why not take advantage of an educational exchange?” And I remember this gunnery sergeant from the Headquarters Marine Corps calls me up and he’s like, “Hagestad, what are you doing? Why would you want to go to the People’s Republic of China? [. . .] And I said, “No, gunny. I think it’s important that we study the cultural history and military capabilities of our adversaries for one day we may face them on the battlefield.”
Bill lived in China as a soldier, and a student. In the process, he developed relationships with people who later rose in the ranks of China’s military.
“[Hagestad] So they look at me as someone who is historically more ensconced in their culture, language, history, even in economy at all a very low level than they are. And they find it curious because they want to know what it was like in China before the foreigners came and before they became this economic power.”
Nowadays, Bill operates as a kind of unofficial attache, making the trip every year or so.
“[Hagestad] Upon arriving, generally in the evening about 10:00 PM or so, I’ll be met by my handlers. And they know that I like Starbucks coffee, so part of that relationship is they want me to feel comfortable. So they’ll bring a beverage which is the last thing you want to do it 10:00 PM is drink a caffeinated beverage. But you do so because of the genuine friendship. Typically, over the following days of the generally a week to two-week stay there, we’ll have discussions regarding different types of military activities.”
In all his years bumping shoulders with Chinese military men, one trip to Beijing stands out above all the rest.
MEETING W/ QIAO & WANG
In 2015, Bill attended one of the most important events that year: a conference for the One Belt, One Road initiative, China’s plan to create a modern Silk Road throughout the eastern hemisphere. One of the most significant government projects of the 21st century, probably one of the most significant since Egypt built three big triangles in a desert.
“[Hagestad] there were no other westerners there. You can imagine these Chinese military in uniform looking at me with my short hair. [. . .] in this tiered room which was supposed to be an economic military exchange to really roll out the one belt one road, certainly not for my benefit. I think I was just more window dressing there from a foreign perspective. They were – the Chinese military across the way, male, female of all ranks from you know… there was mostly field grade from Major to you know General on the other side, very serious you know looking at me, asking questions.”
In a sea of unfamiliar faces, Bill made his way to his assigned seat.
“[Hagestad] it was very daunting. And I recall reading Chinese, I looked down at the nametags because they’re in Chinese and I’m like, you got to be kidding me!”
His handlers had set up a present for him. Seated to one side was a short man with short hair, soft features but a stern look. On his other side, a somewhat older-looking fellow with a round face, short, wavy black hair and a bit more smiley. The two men are essentially unheard of in the West, but to Bill they’re nothing short of celebrities.
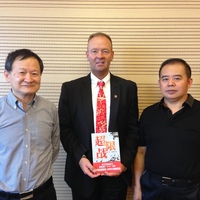
“[Hagestad] even now as I was a trying describe it, it is really almost surreal to sit down between General Qiao Liang, a 3-Star General in the People’s Liberation Army Air Force and Wang Xiangsui who had been a Senior Colonel that he contributed as a co-author of Unrestricted Warfare or War Without Limits.”
Qiao Liang and Wang Xiangsui shaped the way that Bill Hagestad, as well as many in the PLA, conceive of the role of cyber in modern warfare. And it dates back to a time when hacking was hardly a known concept in military circles.
TAIWAN STRAIT CRISIS
Back in March, 1996, the PLA sent 150,000 men to the Fujian province of southern China for a weeks-long series of military exercises. The reason for such a major military gathering was not explicitly stated, though it was universally understood. Fujian is as close as the Chinese mainland gets to the country of Taiwan.
Taiwan was about to hold an election for President. The leading candidate, Lee Teng-hui, had just made a speech at Cornell University in New York which promoted his country’s independence from China. So China, which views Taiwan not as its own country but as a renegade province, did that thing your big brother does where he makes like he’s punching you, but stops just before his fist hits your face. Chinese ships exercised with live fire, and even ballistic missiles, coming within a just few dozen miles of Taiwan’s coast and two major ports.
Qiao Liang and Wang Xiangshui were among the 150,000 men involved in those exercises. They met and, together, realized just how strange the whole scenario was. Qiao recalled, quote:
“At the time, the situation was becoming daily more tense on the Southeast coast, both sides of the straits were all set for a showdown, and even the task force of the two American aircraft carriers rushed a long way to add to the trouble. At that time, the storm was brewing in the mountains and the military situation was pressing so that people were suddenly moved to “think up strategies when facing [such] a situation”
What did it mean to have 150,000 soldiers, ships with live fire, American planes flying overhead, and 400,000 Taiwanese troops at the ready, and yet nobody was actually killing each other? It wasn’t exactly a war, but it was really close to it. Qiao and Wang decided, together, that a different kind of war was emerging before their eyes–a characteristically modern kind of war which didn’t accord with the old rules everyone had gotten used to for centuries. They gave their concept a name–“Unrestricted Warfare”–and began to describe it in what would become one of the most significant, yet little-known military strategy books of recent history.
It was published through the PLA in 1999, receiving acclaim within Chinese military circles. Soon after, the United States Naval Academy got hold of it, and translated the work into English. They published an English version under the name “Unrestricted Warfare: China’s Master Plan to Destroy America.” On the cover: an image of the second tower exploding on 9/11.
“[Nate] That, of course, was just a ploy to sell more books. I read Unrestricted Warfare–it’s not scary, or evil. It portrays America less as an enemy than as spoiled rich kids. It does describe how a smaller country, like China, might defeat America in war, but only in a theoretical sense.”
Aside from the sensationalism, there’s another reason for that book cover. From page 144, quote:
“Whether it be the intrusions of hackers, a major explosion at the World Trade Center, or a bombing attack by bin Laden, all of these greatly exceed the frequency band widths understood by the American military.”
Qiao and Wang, as part of their concept of new warfare, predicted 9/11 two years before it came true.
UW ON CYBER WAR
And 9/11 wasn’t the only thing Qiao and Wang correctly predicted. They were also early in conceiving of cyberspace as a medium for warfare.
“Hacking” was not yet a mainstream phenomenon in the ‘90s. In places like China, especially–where the internet was only a few years old–people were only just getting used to opening emails. But Qiao and Wang wondered whether, in modern warfare, computer experts might be used like soldiers. Quote:
“Who is most likely to become the leading protagonist on the terra incognita of the next war? The first challenger to have appeared, and the most famous, is the computer “hacker.” This chap, who generally has not received any military training or been engaged in any military profession, can easily impair the security of an army or a nation in a major way by simply relying on his personal technical expertise.”
If a hacker could be used to significantly impair an army or a nation, would they be even more effective than a soldier with a gun? And if they were more effective than soldiers with guns, what would warfare look like in the future? Nations would battle over networks, bombarding one another yet without a single human casualty. Wars in cyberspace. Weirdo science-fiction stuff. Quote:
“Computer logic bombs, network viruses, or media weapons, all are focused on paralyzing and undermining, not personnel casualties. [. . .] they will bring about forms of war or revolutions in military affairs which we cannot imagine or predict today. They represent a change with the most profound implications in the history of human warfare to date.”
In the decade following “Unrestricted Warfare,” China took this prediction and ran with it. They began to carve out military-cyber capabilities–putting soldiers in chairs at computer monitors–all under strict secrecy.
“[Hagestad] It’s interesting that in many of my trips to the People’s Republic of China is expressly forbidden to discuss the term “cyber.” [. . .] The Chinese were very reticent in the early days of this war to admit that they had cyber warfare to come in equivalent to the non-componentized version that the US announced in 2009. From 2010 on, the Chinese continued to deny that they had any sort of offensive or defensive cyber warfare capability.”
Over time, China developed a uniquely Chinese kind of cyber war machine: enlisting huge numbers of military personnel and, perhaps most notorious of all, weaponizing their national corporations in the fight.
If we want to understand what cyber war really is, China has a model. It was seeded by Qiao Liang and Wang Xiangsui, and the image of a future where hackers could be used like soldiers. In the past two decades it has blossomed, causing some of the most significant international incidents of the modern era: hacks that have crippled Western institutions, and reshuffled international order.
So, with Qiao and Wang as our guides, this mini-series will cover two stories of cyber war in the Chinese model. Let’s get started, now, with the first: a textbook case study in how to combine political, economic and cyber weapons to destroy Western power.
NORTEL’S SIZE
It’s difficult to describe just how big Nortel Networks was at their peak. It’s kind of like trying to explain floppy disks to someone under the age of 30.
[Nate] Floppy disc? Is that, like, when you bring a girl back to your place but you had too much to drink so you can’t…you know…
…As I was saying!…
At the turn of the century, during its peak, Nortel was massive. Their revenue exceeded ten billion a year and a market cap exceeding 250. They constituted over a third of Canada’s entire stock index. In other words, they were half as big as all other publicly-traded Canadian companies combined. And here’s another fun fact: at one point, according to The Globe and Mail, over 70 percent of all internet traffic worldwide ran through Nortel fibre optics. 70 percent! Basically, every time you did something on the internet in 2002, it ran on Nortel wires.
And if those numbers don’t quite convince you, it’s probably because you’ve never been to Carling Campus.
Carling–Nortel’s headquarters on the banks of the Ottawa River–is a kingdom–a sprawling, magnificent manifestation of the company’s success.
In its appearance, the campus closely resembles the U.S. Capitol grounds. A long, rectangular lawn is flanked by buildings lined up on either side, and the central building at its head, featuring a triangular roof that provides a focal point for the eye. The buildings, on their own, comprise over two million square feet. And if you count the parking lots, it’s a lot more than that. You can see, in this place, the prototype of future mega-HQs to come: Googleplex, Apple Park, those campuses that are almost cities in and of themselves.
And as those companies began attracting talent from around the world to San Francisco during the boom of Silicon Valley, 90,000 employees chose to ignore the call, hunkering down in chilly Ottawa where some of the best, most innovative development was happening. A longtime Nortel veteran reminisced how, quote: “You were just surrounded by the most interesting and intelligent people that you could find anywhere in the world. Nobody would ever tell me I couldn’t do something.” . Nortel’s success had a knock-on effect in the city of Ottawa, promoting a tech culture which, in its heyday, rivaled California as the place to be. A Bloomberg article painted a picture, quote:
“Back then, Ottawa, not traditionally (or since) known for its glamour, seemed full of sports cars, corporate jets, and even society scandals featuring tech CEOs. In 1999 the co-founder of [. . .] Nortel’s precursor company threw a gala at which his wife showed up in a 1 million [dollar] leather bodysuit with an anatomically correct gold breastplate and a 15-carat-diamond nipple.”
The disadvantage to being so successful–having all the glitz and the glamour to yourself–is that it makes you a target. Carling Campus was both a trophy of commercial success and, in a different view, a juicy, red, 2,000,000-square-foot bullseye. While the Canadians were diamond-encrusting their nipples, people halfway around the world were plotting how to get those diamond nipples for themselves.
UW ASYMMETRIC WARFARE
The second downside to success is that it breeds complacency. In modern, unrestricted warfare, it’s Western powers who are at a comparative disadvantage against newer, more unfamiliar kinds of threats. For instance, the United States might have the best army, but what’s an army good for if you’re not facing an army? If you’re facing hackers, or terrorists–an enemy who follows a different set of rules. Quote:
“In an age when an old order is about to be removed, those in the lead are frequently those who are the first to destroy the rules or those who are the earliest to adapt to this situation. [. . .] For bin Laden who hides under the hills of Islamic fundamentalism, [George] Soros who conceals himself within the forests of free economics, and the computer hackers who hide themselves in the green curtains of networks, no [. . .] boundaries exist.”
Like the U.S. army, Nortel Networks was big, strong, and therefore well-suited to competing against other companies like them. But were they prepared for a different kind of enemy? One who didn’t follow the same rulebook, for whom no boundaries existed?
No, they were not.
INTRO TO REN
Were you to pick one person, more than anyone else on the planet, who stood to gain from seeing Nortel fall, it might’ve been a man with a wrinkled face, short, black hair, with a friendly face that, by some accounts, belies his true nature. A man whose short stature takes nothing away from his massive worldwide influence today. This man is someone you’ve heard about if you’re an avid listener of our show: Huawei’s controversial, jovial CEO, Ren Zhengfei.
“[Hagestad] This is a historical case study for students of military and economic interest [. . .] specifically if one looks back to 1948 and Mao Zedong pushing General Chiang Kai-shek off to the island of – nation of Taiwan. During that period, you either supported Mao Zedong as a true believer of China or you did not. Well, in the case of poor Mr. Ren Zhengfei, who has served in the People’s Liberation Army, he’s the CEO and founder of Huawei, while he was serving in a – I believe a cryptological or a communications type unit within the PLA is they went to do his background check for a communist membership. They discovered that his parents had actually supported Chiang Kai-shek.”
By pure chance, Ren Zhengfei was born on the wrong side of China’s internal political wars. The perceived sins of his parents were transferred unto him, whether he liked it or not.
“‘[Hagestad] Now, in any background situation regardless of whether you’re Chinese or US or whatever country it is […]. They’re a little bit unforgiving and they basically said, “We are not going to authorize you to continue in this man’s PLA because your parents supported the wrong military. We don’t know that we can trust you to carry out the duties of the state as a Chinese military officer.”
Being made an outcast, through no fault of his own, must’ve been frustrating for the young Ren. The government was cutting down its army, and he left for civilian life. But he never became jaded.
“[Hagestad] Ren Zhengfei, although he was field of communist member, he was still Chinese and at the end of the day, he knew that he must support the mother Country that he grew up in regardless of the foibles of his parents in 1948, 1949 China.”
He had an idea that could help China and, in so doing, might propel him back into good standing.
“[Hagestad] Certainly heartbroken and you know just made over his own misfortune, he went off and founded Huawei Telecommunications Company.”
With only 21,000 Yuan–the equivalent of just $5,000–and a small amount of investor money, Huawei didn’t have much to build with. But Ren’s idea didn’t require all the trappings of a normal company, because they weren’t going to actually build anything. They would simply take imported tech from the West, reverse engineer it, then sell it in China. A highly cost-effective approach, and useful to the PLA.
“[Hagestad] The very notion that he had been sacked from the military went itself to his comrades who he left behind needing equipment. He knew that there was a need there commercially because they couldn’t just go and buy it. They would have to essentially steal it. Most militaries don’t have the budget to go on purchase or effectively steal things as they would like to. So he created a market for himself with the Chinese military, Mr. Ren Zhengfei did.”
Huawei’s first big success was a telephone switch, but a real breakthrough came a year later, when the company signed a contract to build the first national telecommunications network for the PLA. Ren personally met with the General Secretary of the CCP, who noted just how important the project was to them. Quote: “switching equipment technology was related to national security, and that a nation that did not have its own switching equipment was like one that lacked its own military.”
For Ren Zhengfei, Huawei was both a business venture and a political tool–from its inception, and then years later, when the Chinese government took aim at Nortel Networks.
CHINESE MOTIVE
How Nortel entered the sights of the Chinese government is in some ways obvious, and in other ways not. For one thing, there was the matter of intellectual property. China was only just starting to build up their network infrastructure as Nortel hit its peak, so it’s only natural that they…took an interest in Nortel’s wares.
“[Hagestad] They saw, the Chinese saw the value of the intellectual property, thus, you know originating in China with the expansion of the network there when the Chinese needed it. And they said, you know what, we could really use this technology.”
IP theft would be enough reason for China to target Nortel but, really, that was only the beginning of it.
We don’t usually conceive of internet infrastructure as a means of control but, really, it is. It is to control the flow of information. Whoever uses Nortel wires to access the internet, to communicate across distances, becomes reliant on Nortel and, in some sense, Canada. China’s very aware of this kind of influence. It’s just like their Belt and Road Initiative where, by building the infrastructure for it, they are in effect becoming the arbiters of international trade in the eastern hemisphere.
So it was perhaps lucky timing that, just as Huawei grew big enough to expand outside China’s borders, the CCP yet again found political interests in Ren Zhengfei’s business ventures. Huawei’s competition against Nortel would soon become a proxy for China’s competition with the West over global dominance in tech.
In other words: while Nortel may not have known it, they were in a battle for control of the internet. They were diamond-encrusting their nipples, and their enemies–who they didn’t even know were their enemies–were plotting how to take them down.
.png)