Key Points
- Coronavirus-themed Attacks: The Cybereason Nocturnus team is investigating multiple types of campaigns that specifically target regions most heavily impacted by the coronavirus with coronavirus-themed files and domains.
- Leveraging Anxiety: Attackers are abusing the pandemic for their benefit by manipulating people’s anxiety over the virus to trick them into downloading malware.
- Taking Advantage of Remote Workers: Attackers are taking advantage of the shift to remote work by promoting malware masquerading as VPN installers. This is particularly dangerous as businesses make the transition to remote work and suggest best practices to employees, including the use of VPNs.
- Using Mobile Malware: Attackers are creating malicious mobile applications posing as legitimate apps developed by the World Health Organization to help individuals recover from coronavirus. Instead, the application downloads the Cerberus banking trojan to steal sensitive data.
- Targeting Healthcare Organizations: Attackers are using ransomware to target healthcare organizations, arguably the most vital and overworked among us at this time.
For a deep dive on securing business continuity outside of the IT perimeter, watch our latest webinar On-Demand.
Security Recommendations
The Cybereason Nocturnus team strongly recommends taking steps to prevent phishing attacks. This includes the use of tools like email filtering, but also the education of employees to explain the risks and give them simple, actionable tips they can use in their day-to-day work.
- Be Careful: To significantly reduce the likelihood of falling victim to a phishing attack, it is best to be careful while browsing online and checking email. Check the authenticity of the sender for any email you download information from, and check if the content makes sense to you. If there is any doubt, do not click on it and report it to your security team immediately.
- Watch Out for Shortened Links: If you have any doubt about the validity of a link, open a new browser window and type the URL into the address bar. Be sure to examine the URL and make sure it is authentic.
- Be Wary of Emails Asking for Confidential Information: Emails that ask for information like credentials, credit card information, and other sensitive data are usually not legitimate. Legitimate organizations, including and especially banks, will never request sensitive information via email and will always redirect you to a secure website or other channels.
- Only Download Files from Trusted Websites: Be sure to double check that a website you are using is legitimate and trusted. To download specific VPNs, search for the company’s official website and install directly from there. Avoid downloading cracked versions, since they are usually bundled with other software or malware and can cause damage to the machine.
Introduction
As recent history has taught us, large-scale events affect us not only in the physical dimension, but also in the cyber dimension. Elections, olympics games, wars, and health issues, including the recent coronavirus outbreak, have affected billions of people worldwide and quickly made their way into the cyber world.
Unfortunately, attackers often take advantage of global incidents to find new ways to attack, and COVID-19 is no exception. They abuse citizen’s panic to get them to open “urgent” emails they would otherwise not open. Cybereason’s Nocturnus team is continuing to observe hundreds of phishing attacks that use coronavirus-themed files and domains to distribute malware and infect victims all over the world.
The Initial Phase of Coronavirus-themed Campaigns
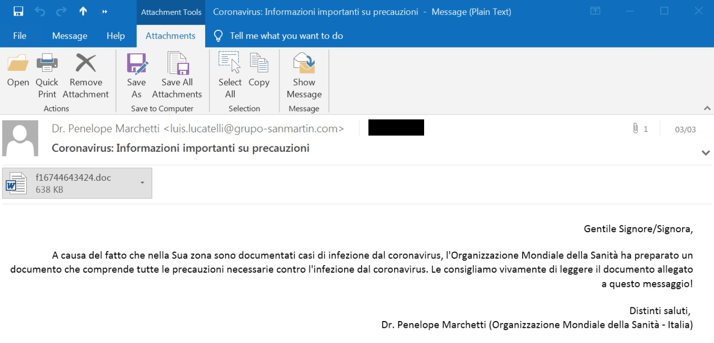
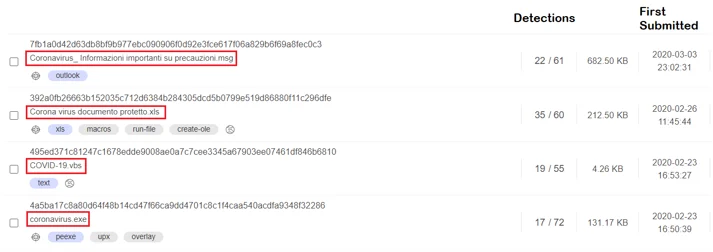
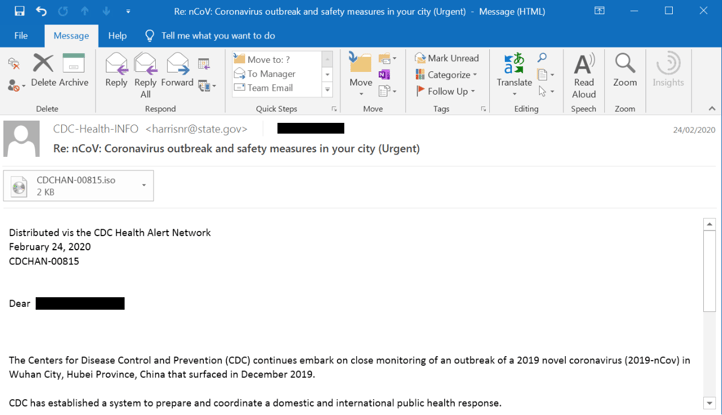
As various researchers have reported, an array of malware was distributed by these “coronavirus” campaigns, including Emotet, RemcomRAT, ParallaxRAT, HawkEye, TrickBot, Agent Tesla and more. The most common technique observed thus far is a spear phishing attack that uses coronavirus-themed emails with malicious attachments.
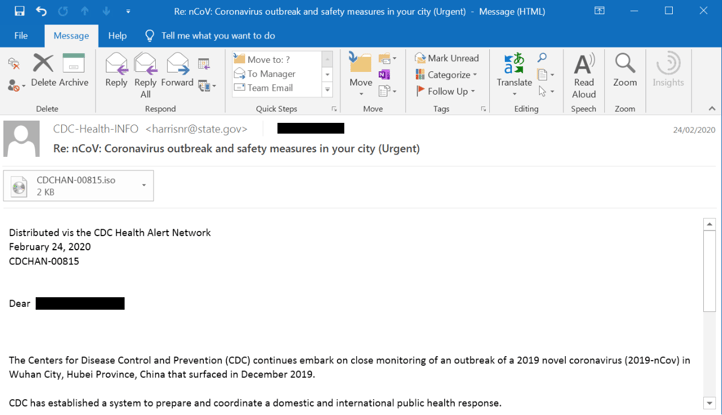
Phishing email related to coronavirus.
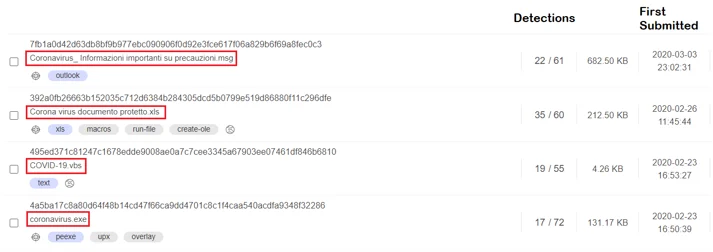
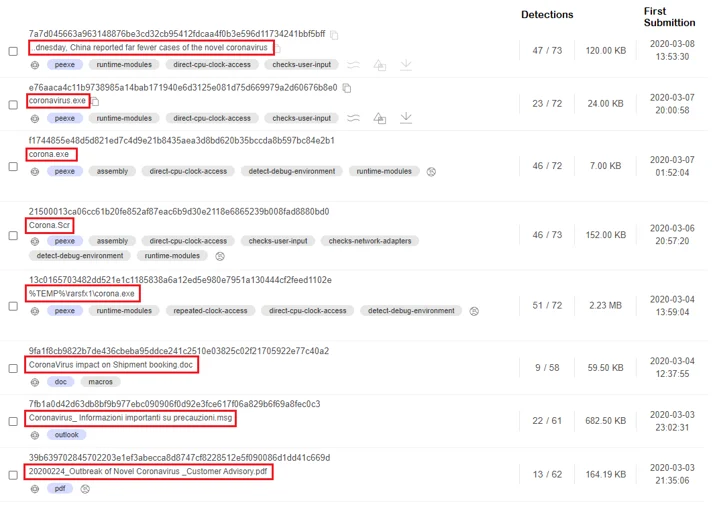
When coronavirus first began to spread in China, the Cybereason team observed that the majority of malicious, coronavirus-themed files were submitted from China and targeted Chinese speakers. As the virus continued to spread and infect more countries, the number of uploads increased in just a few a days from tens to hundreds, where new files were submitted from different countries every day. These new uploads targeted people from Japan, South Korea, Europe, and other infected countries.
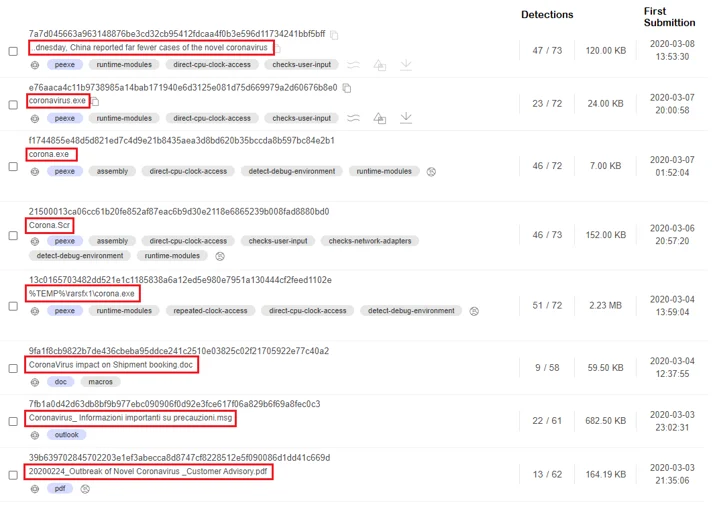
Malicious coronavirus-themed files found in VirusTotal.
South Korea, one of the first countries affected by coronavirus, was targeted with multiple different coronavirus-themed phishing attacks. They were even targeted by fake ransomware campaigns that do not actually encrypt any files, but instead use it as scareware to scare victims into paying money.
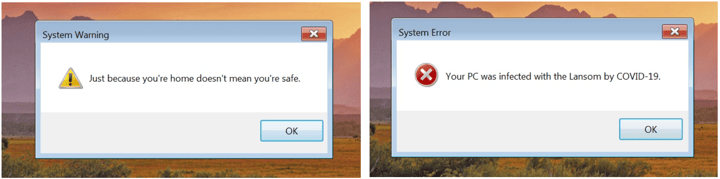
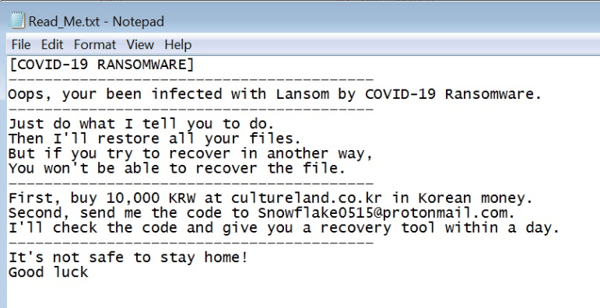 A fake ransom note for the scareware.
A fake ransom note for the scareware.
Switching Targets
As we continue to track the coronavirus, we are seeing China begin the recovery process and the center of the pandemic move to Europe: specifically, Italy. Subsequently, the outbreak of the virus has created an outpouring of coronavirus-themed phishing campaigns targeting Italian speakers.
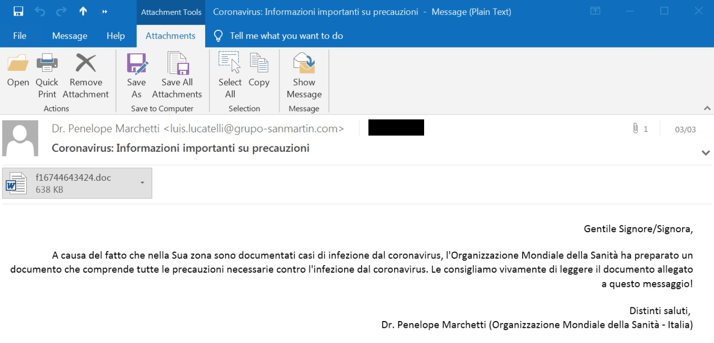
Coronavirus-themed phishing email in Italian.
Malicious coronavirus-themed files submitted from Italy starting in mid-February.
Preying on Those Searching for Information
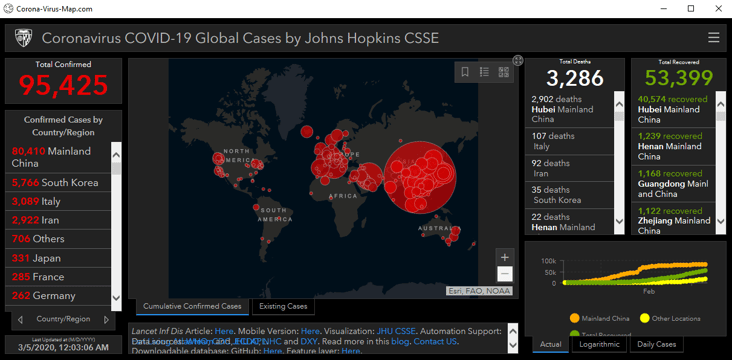
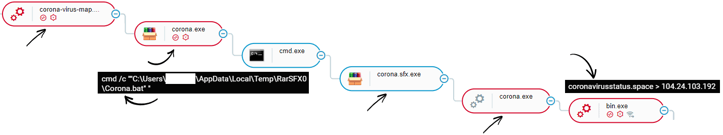
Another more general trend attackers are taking is using a coronavirus map to distribute malware. As published recently, this map hides the malicious download of the Azorult infostealer to the victim’s machine. As we have previously researched, the Azorult infostealer is able to steal sensitive information and send it back to the attacker.
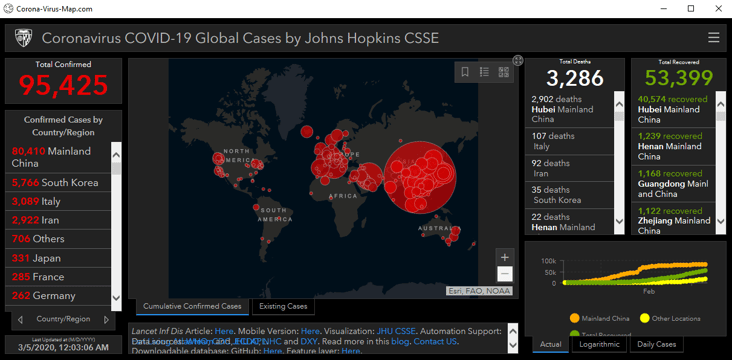
A coronavirus map hiding the malicious download of the Azorult infostealer.
In this campaign, the attackers hide their malicious activity not only in the map UI, but also in coronavirus-themed files and domains.
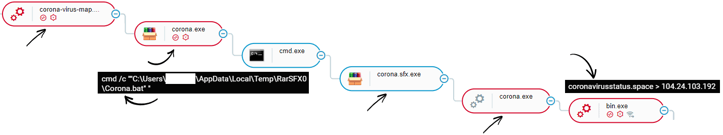
The malicious coronavirus map process tree in the Cybereason Platform.
Leveraging Fake VPNs
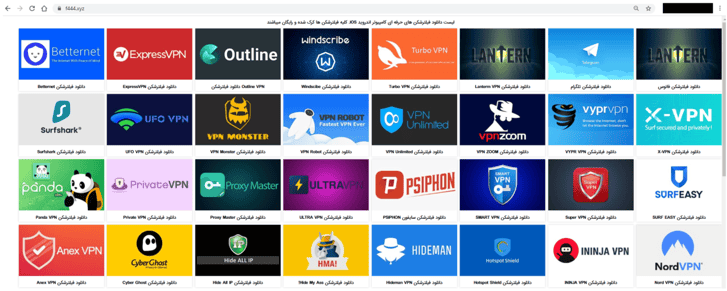
The Cybereason Nocturnus team is also following an increase in the availability of malicious, fake VPN installers. As many businesses turn to remote work to reduce the spread of coronavirus, they are also urging their employees to use a VPN as a best practice. Attackers are taking advantage of this shift by tricking users to download and install malware masquerading as legitimate VPN clients.
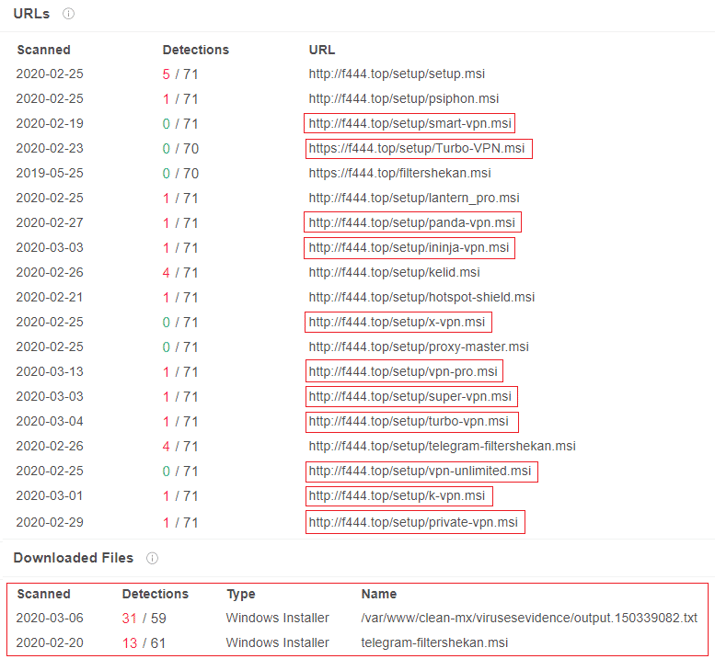
The Cybereason Nocturnus team has uncovered a fake website (fil24[.]xyz) that claims to provide various legitimate VPN installers and installers for other programs like Facebook and Instagram. However, when a user tries to download the “VPN”, they are redirected to f444[.]xyz and download malware.
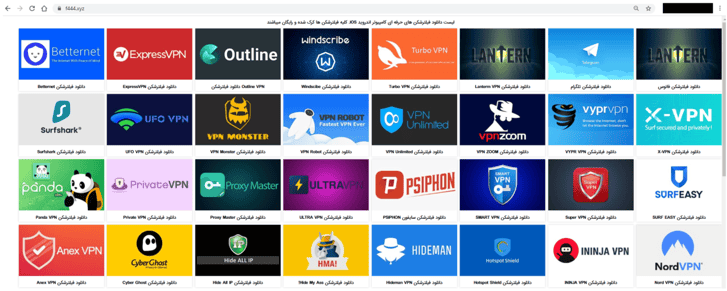
Screenshot of the site f444[.]xyz, which contains malware masquerading as VPNs.
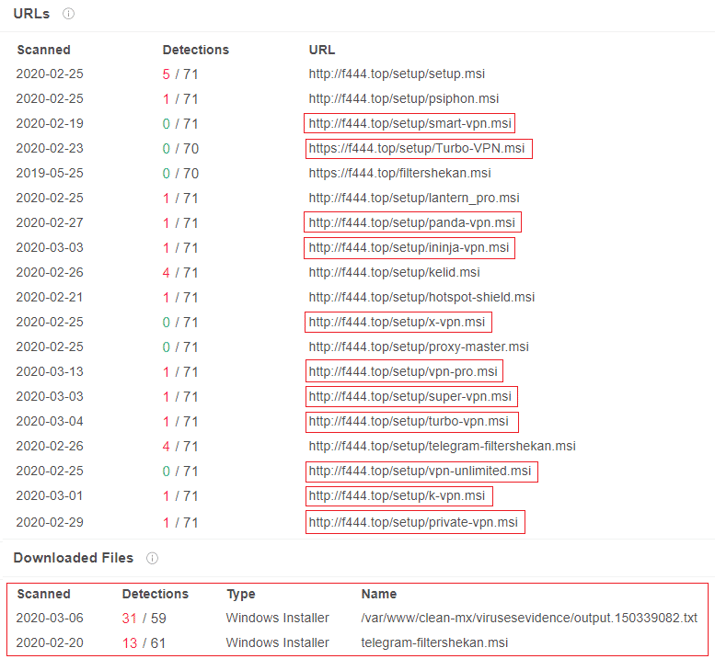
VirusTotal results for files downloaded from f444[.]top.
Mobile Malware
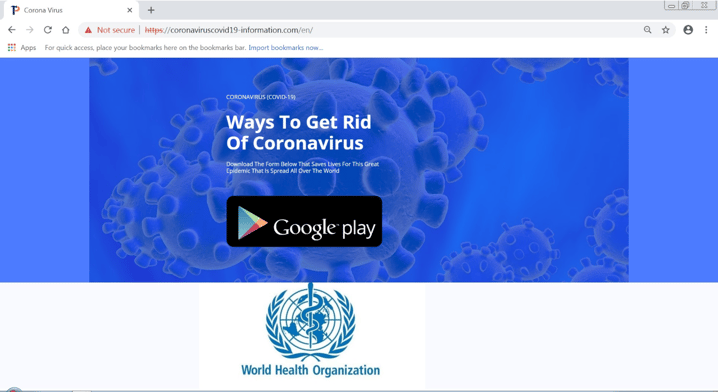
Even the mobile malware industry is looking to take advantage of the coronavirus outbreak. There is an ongoing campaign leveraging a malicious website, available in multiple languages, that misleads users to download malware masquerading as a legitimate application. This “Ways to Get Rid of Coronavirus” application claims to be created by the “World Health Organization” to establish trust and authenticity. However, on download, the application is actually the infamous Cerberus banking trojan, which is used to steal sensitive banking information.
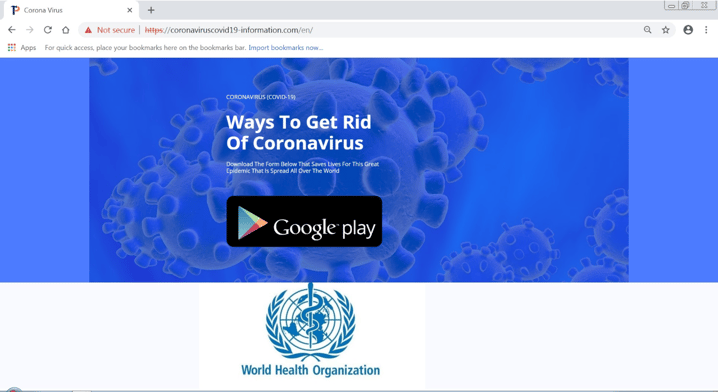
The fake application that actually installs the Cerberus banking trojan.
Attacks Against Hospitals and Research Labs
Attackers have even gone so far as to use this pandemic to target the most overworked and arguably the most vital among us: the healthcare industry. Last week, a ransomware attack was discovered against the University Hospital Brno. This university has one of the largest COVID-19 research labs in the country. However, due to the malware attack, the entire IT network of the clinic was shut down, affecting additional departments across the hospital.
This kind of attack adds tremendous anxiety to an already stressed hospital staff, which can lead to panic among patients. Healthcare workers are an easy target during times of crisis, since they are looking for as many answers and as much information about the situation as possible. This makes them a prime target for phishing attacks, and unfortunately, we expect attackers will continue to take advantage of the situation and continue to target healthcare organizations with destructive attacks.
Closing Thoughts
At this point, there is still uncertainty around the coronavirus: when it will end, how fast it is currently spreading. This is causing a great deal of concern around the world, and especially in Europe, Iran, and the USA, which are the hardest hit at the moment. We suspect that phishing campaigns that leverage this pandemic will continue to be high, especially in areas where the population is most affected by the virus.
Before you go, we've also got an emergency checklist designed to help your security and IT teams prepare for this change. Read the checklist.
IOCs
Download the IOCs for this research here.



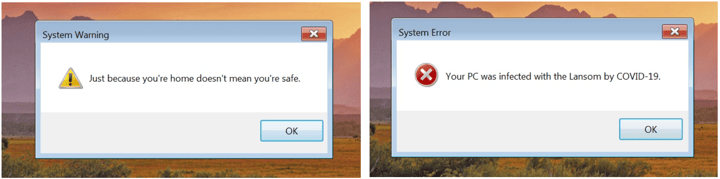
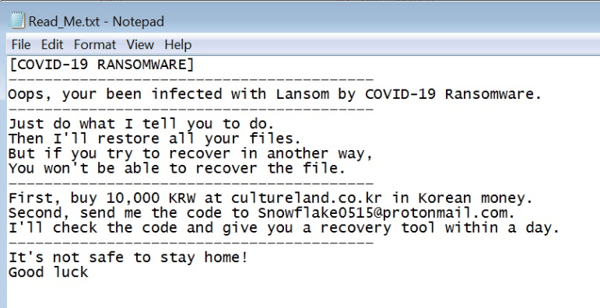 A fake ransom note for the scareware.
A fake ransom note for the scareware.