
Fake Installer: Ultimately, ValleyRAT infection
In this Threat Analysis Report, Cybereason explores the fake installer, ValleyRAT
Lital Asher-Dotan
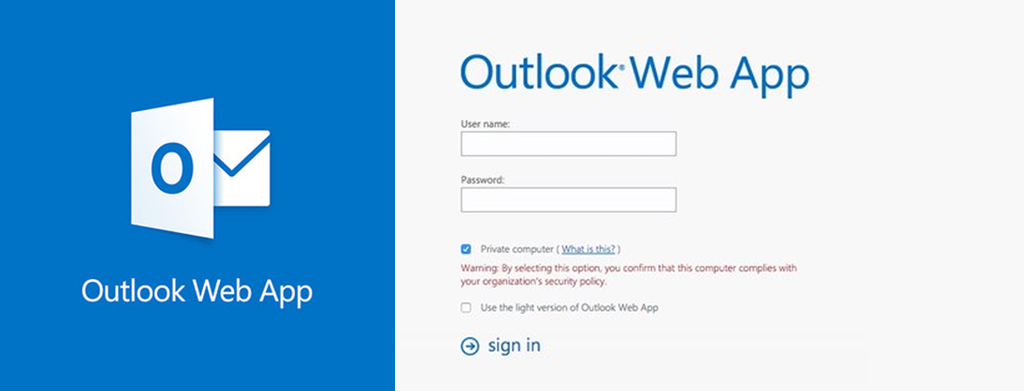
We are excited about the vast press coverage we have received due to the publication of our latest discovery: A targeted APT attack leveraging Microsoft OWA server. Like any other startup, we greatly appreciate the publicity; but beyond that, we are happy to see this research reach a broader audience because it is an important attack vector that security teams should be aware of. While we wanted to give a brief overview of our research below, if you would like to read a more in-depth discussion about the implications of this type of attack, read Michael Mimoso's post in Threat Post and Graham Cluley's blog post.
This attack was not just a compromise of the corporate email server: it compromised the company's entire Windows domain, giving the attacker the proverbial keys to the kingdom.
This attack highlights one of Cybeareason's core capabilities: our unique ability to detect malicious activity using automated behavioral analysis. Through continuous observation of related behavior, Cybereason was able to recognize the malicious DLL file associated with the customers OWA and report on them.
The attack was designed specifically to evade anti-virus and human analysis. One of the methods used to throw off casual observers was hiding itself in .NET assembly cache. The .NET assembly cache is a temporary local file mechanism used by the .NET framework and often stores files that are unique to the computer in which they are running. This directory is created dynamically so it would be highly unlikely for any detection software or human analysis to make sense of what they were viewing.
Using our behavioral detection engine, Cybereason noticed:
It is highly unlikely that other endpoint detection and response solutions would automatically detect it. Some solutions might have shown, upon an explicit query, that there was a single unsigned DLL file in the OWA process; but then again, such behavior is only anomalous in the right context. Such solutions would offer no other context or understanding of the significance of the situation.

Lital is a Marketing Team Leader, Storyteller, Technology Marketing Expert. She joined Cybereason as the first marketing hire and built a full marketing department. Specializing in brand building, product marketing, communication and content. Passionate about building ROI-driven marketing teams.

In this Threat Analysis Report, Cybereason explores the fake installer, ValleyRAT

Cybereason detects and prevents the ongoing 3CXDesktopApp supply chain attack.

In this Threat Analysis Report, Cybereason explores the fake installer, ValleyRAT

Cybereason detects and prevents the ongoing 3CXDesktopApp supply chain attack.
Get the latest research, expert insights, and security industry news.
Subscribe