Cybereason Posts Best Results in History of MITRE ATT&CK Evaluations
Cybereason leads the industry in the MITRE ATT&CK Enterprise Evaluation 2022, achieving the best results ever in the history of these evaluations...

Cybereason Team
Today, we announced that the Cybereason Defense Platform has been evaluated by MITRE to show how we approach threat detection in the context of the MITRE ATT&CK framework. This open and transparent methodology for evaluating vendor capabilities seeks to educate and empower the defender, which is why Cybereason chose to participate. The MITRE ATT&CK evaluation demonstrates that the Cybereason Defense Platform sets the standard by providing the most complete coverage across MITRE ATT&CK, the most real-time alerts, and the most correlated (tainted) detections of any tool or vendor tested.
Detections are only as valuable as the insights they provide. The MITRE ATT&CK evaluations test how effectively vendors enable defenders to discover, understand, and respond to the full attack with valuable awareness.
In this sophisticated set of tests, we believe the only outcome that matters is the one that best empowers the defender to stop attacks before harm happens. To achieve this, you need to see the full attack clearly and in real time, while simultaneously managing alert fatigue. In order to best understand these results, let's take a look at what it truly means to bring informative detections and high visibility to your environment.
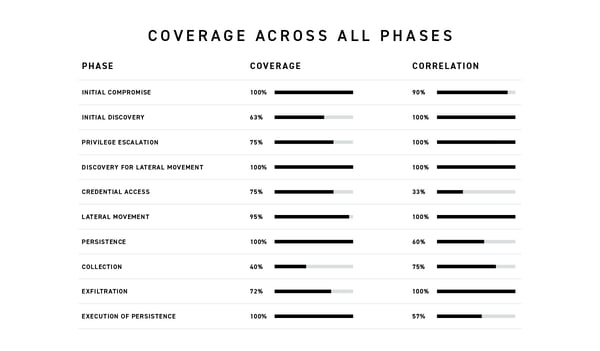
Receiving correlated detections at all phases of an attack, from initial access to exfiltration, is priceless to a defender. Gaps in coverage and alerting make it harder for teams to piece together an attack. During the MITRE ATT&CK evaluation, the Cybereason Defense Platform’s detections and alerts were created in real time and evenly distributed throughout the attack sequence. Defenders can see the full scope of an attack as it happens, pinpoint the exact stage an attack is in, and remediate attacks faster.
The ability to correlate data, unaided and in real-time, provides an immense advantage to defenders. Using correlated data to create a full attack story within moments of initial detection can mean the difference between an attacker stopped, and damage to an organization. Nearly 90% of our detections are correlated to preceding malicious events (tainted). This gives you an intuitive understanding of the path an attacker takes through and across endpoints, which significantly shortens your time to respond and remediate.
.png?width=600&name=Mitre_Alerts_Light%20(1).png)
Cybereason has the highest coverage of MITRE ATT&CK techniques, barring a configuration change. Defenders have complete visibility into what attackers are doing on their network. The Cybereason Defense platform’s ability to provide clarity into your environment automatically and without configuration changes is unparalleled in this evaluation.
Once information is collected and correlated, defenders need a tool able to alert intelligently across all stages of the attack. With the Cybereason Defense Platform, all phases of the attack are prioritized properly so that alerts reveal activity at all stages, from initial access onwards, and are not clustered into one or two specific areas of the attack.
.png?width=600&name=Mitre_Correlation_Light%20(1).png)
An abundance of alerts on one phase and a dearth in another can shift priorities and slow defenders down as they churn through alerts. Overloading defenders leads to unnecessary alert fatigue, which decreases productivity. With the Cybereason Defense Platform, we do not cluster alerts in certain phases, and no detection is delayed. This allows defenders the to connect the dots much faster.
One of the most noteworthy sections of the evaluation of the Cybereason Defense Platform is when it comes to behavioral, real-time detections, where we had the largest number of unassisted, automatic alerts.
As mentioned above, when a large number of alerts are clustered around a specific segment of an attack while other parts of the attack go relatively unnoticed, a defender is at risk of missing critical data. Although they may look statistically better, a disproportionate number of alerts focused on a few sections of the attack will hinder defenders from painting the bigger picture in a timely manner.
How much of your data can be exfiltrated in an hour? That is the question you need to ask yourself when dealing with delays. Reportedly, it can take a Russian APT a mere ten minutes from the moment of initial foothold until domain admin privileges are gained. With such little precious time to waste, delayed alerts take away the defender’s control of the situation and can be quantified in damage, dollars, and data.
Real-time is the best time. The Cybereason Defense Platform prioritizes real-time detections. All of Cybereason’s detections in the MITRE evaluations occurred in real time, unaided, and without configuration changes. With our Cross-machine Correlation Engine, defenders can expect to be alerted about attacks as quickly as possible, with as much information as possible.
Defenders need to be able to act as quickly and effectively as possible. Any missed time is a moment the attacker has the advantage. The Cybereason Defense Platform automatically correlates, enriches, and detects malicious events in real time so defenders can act quicker and more effectively. Since this is all automatic, we are able to provide knowledge faster, so defenders can know what happened and how to handle it before damage occurs.
We are pleased to have participated in the MITRE ATT&CK evaluations. The ability to publicly test the Cybereason Defense Platform against real-life attack scenarios is a rare opportunity. We pride ourselves on having built our platform from the ground up with real-life attack scenarios in mind, which is clearly evident in the evaluation.
The Cybereason Defense Platform empowers defenders to discover, understand, and respond to attacks in real time.
Read to talk about our MITRE evaluation results? Click here

Cybereason is dedicated to partnering with Defenders to end attacks at the endpoint, in the cloud and across the entire enterprise ecosystem. Only the AI-driven Cybereason XDR Platform provides predictive prevention, detection and response that is undefeated against modern ransomware and advanced attack techniques. The Cybereason MalOp™ instantly delivers context-rich attack intelligence across every affected device, user and system with unparalleled speed and accuracy. Cybereason turns threat data into actionable decisions at the speed of business.
All Posts by Cybereason Team
Cybereason leads the industry in the MITRE ATT&CK Enterprise Evaluation 2022, achieving the best results ever in the history of these evaluations...
In the 2024 MITRE ATT&CK® Enterprise Evaluation, Cybereason demonstrated why out-of-the-box detection coverage and operational efficiency matter more than ever.
Cybereason leads the industry in the MITRE ATT&CK Enterprise Evaluation 2022, achieving the best results ever in the history of these evaluations...
In the 2024 MITRE ATT&CK® Enterprise Evaluation, Cybereason demonstrated why out-of-the-box detection coverage and operational efficiency matter more than ever.
Get the latest research, expert insights, and security industry news.
Subscribe