Two of the key capabilities defenders must have include detection and response. Detection and response often take the form of a security operations center (SOC). A SOC is the holistic approach to the people, processes, and technology involved in detecting, analyzing, and engaging the first level response to a cybersecurity incident. SOCs start with this core mission and employ a variety of individuals from junior level analysts to senior malware analysts.
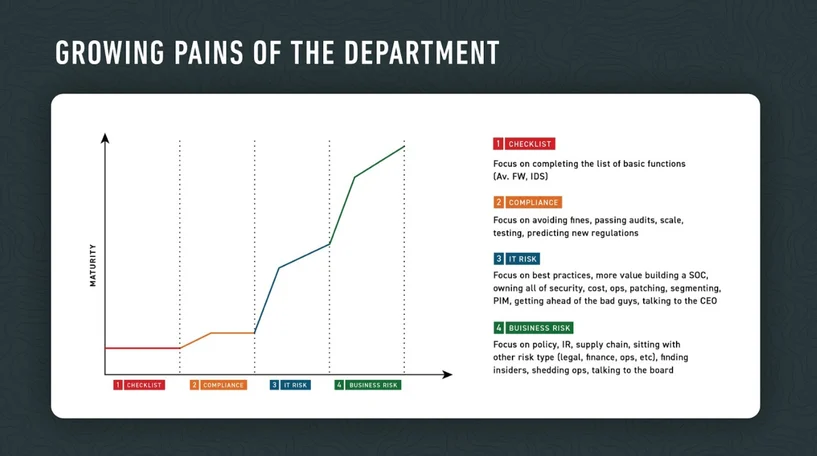
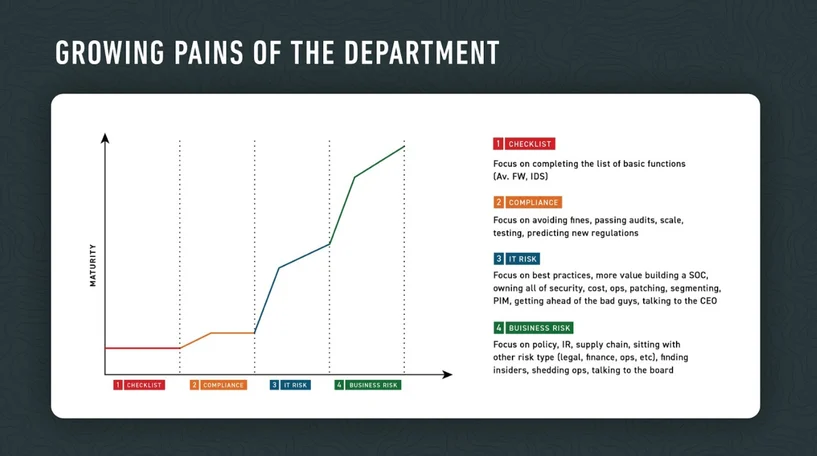
In many organizations, a SOC is built organically and inherits responsibilities that lead to additional processes to manage. Many factors contribute to SOCs, and it’s important to understand there is no one-size-fits-all approach to the SOC. The size of the SOC depends on the organization’s security maturity level and relies on the goals of the overall organization. It needs to be properly aligned to protect the fundamental risk scenarios that impact an organization, whether compliance related or leveled up to business risk.
SOCs are the first line of defense for businesses when addressing cyber threats. At the very least, they handle the beginning stages of containment actions during an incident. They actively monitor the environment, hunt for threats, and establish plans to escalate breaches or initiate incident response procedures.
When trying to address the question “Is my SOC as effective as possible?”, one of the most challenging components you will face is staffing. Some common, difficult to answer questions can include:
- How do you find the right people?
- How do you retain the right people?
- Do you need to staff overnight or on weekends?
- What responsibility do you want to directly manage?
- What work can you outsource?
- How do these decisions impact your overall mission to effectively stop a breach before damage occurs?
Staffing is a complex issue for any department that just compounds with highly intensive security roles.
How Do You Build an Effective SOC?
What type of SOC you want to build depends on the resources available to you and the experience of your team. It’s critical to consider the technologies and processes you want to use.
What skill level is needed to use these technologies? What experience is required to handle the processes you envision or have established?
These questions become more difficult to answer as you consider additional factors, such as the need for security 24/7, across geographies. If you have advanced resources and an existing team, you may be more inclined to have an in-house SOC. In contrast, with limited resources and a small team, you are more likely to have a fully outsourced SOC.
There are three common ways to build a SOC:
- In-house: The security organization owns hiring and defines all processes.
- Semi-outsourced: Some staff and processes are outsourced.
- Outsourced: All hiring and most processes are a third-party responsibility.
Building an In-house SOC
Building an in-house SOC gives you total control over the security process. This can be invaluable for organizations with existing, knowledgeable teams that use customized workflows and have a complete understanding of their environment. These teams are typically well-funded, have multiple junior and senior analysts, and may even have a dedicated threat hunting team.
The difficulty with an in-house SOC comes from resource requirements. In-house SOCs need to be managed and require funding and other resources from the larger organization. They need to be staffed with the right talent, and they need to have outlined metrics for success. In-house SOCs are most valuable for organizations that are ready to handle the responsibility and have the time to develop a critical department that has the resources to succeed.
Pros: Granular control of the security process and of the team.
Cons: Takes a long time to establish, to hire, and train the team.
Insight from the Cybereason CSO, Sam Curry:
"To some degree, the talent gap in cybersecurity is a self-inflicted wound: we have both designed for only the best among us and have required that before becoming a security expert analysts have to become experts in dozens of subskills. The path can be made more welcoming and approachable. Our goal should be to take anyone with an inclination and no technical phobia and get them started on the cybersecurity path: doing security early and learning as they go. The tools could be made more approachable and more transparent to the tasks of security with design changes and focus on users without falling afoul of leaky abstraction and not understanding how it works under the hood. Our goal should be to take a math major, a physics major, a history major or a curious car mechanic who has the right attitude and make a novice on the path to an intermediate analyst within 6 months if not less!"
Building a Semi-outsourced SOC
Building a semi-outsourced SOC gives you control over your security process with the added benefit of an expert, external team on hand. This gives you the flexibility to assign night shifts or other inconvenient shifts like weekends and holidays, to an external team you can trust to handle incidents. It also gives you more freedom on the hiring process, as you can have a smaller internal team augmented with a larger external team.
For example, having a semi-outsourced SOC is a great option for security teams that want to be fully in-house, but aren’t ready for the responsibility yet. Starting with an inexperienced team that is backed by a group of experts can give your team the freedom to grow into expert analysts without the risk.
Alternatively, an experienced internal team can benefit and retain talent by focusing on critical events while offloading monotonous work to an external team. This is a great way to help prevent internal team burn out. This strategy can also be used to up-level a SOC to address incident response issues, or allow for a hybrid team that can handle advanced analysis, incident response, and threat hunting.
Pros: Flexibility, the opportunity for growth, and improved talent retention.
Cons: Takes time to hire a team and manage talent. May also have additional cost considerations.
Building an Outsourced SOC
An outsourced SOC is the total handoff of the security operations center to an external third party. Fully outsourced SOCs are convenient for organizations that don’t want to hire security analysts or establish processes to build a security program. You offload the work onto a managed service that has an expert team ready to take care of the heavy lifting for you. If you want, you can hire in-house threat hunters and incident responders or outsource those as well. This is the hands-off, let-me-be-safe approach to cybersecurity.
While a fully outsourced SOC is an attractive option, the complexity of some environments and the lack of control can make achieving security objectives more challenging. While this is not the case with every environment, it’s important to have a good understanding of the risk profile of your environment and how to detect an attack so you can choose the appropriate way to build a SOC for your organization.
Pros: Much easier to operate, with excellent risk management with less investment from your organization.
Cons: Can be difficult to implement in complex environments.
Insight From Justin Bell, Senior Engineer, Trustwave:
"At Trustwave, we have 9 SOCs distributed globally which allows us to provide 24/7x365 coverage for triage and response no matter what time or where in the world assets are located.
We provide a portal that allows direct interaction with analysts, view data and perform actions with your security services/devices ensuring you still close with the defenders protecting your organization
Another advantage to an outsourced SOC is the deep expertise access you get. Our Spiderlab’s team is composed of 250+ researchers, ethical hackers and incident responders. This deep bench alleviates an organization from having to find the right talent and freeing up management to focus on other pressing security issues."
Outsource Wisely
With the existing talent shortage, it makes sense for the majority of organizations to incorporate some form of outsourcing into their SOC. These are the three effective models for establishing a SOC, though they are not strict guidelines for how every security team must organize. Each security team has different needs, and it’s important to customize your SOC accordingly. What are your thoughts on SOCs? Do you outsource?
IT and security teams need support now more than ever, as teams struggle with balancing cooperative remote work and meeting the needs of an entire organization. If you need additional support to maintain business continuity while also defending a totally remote workforce, check out our business continuity toolkit.