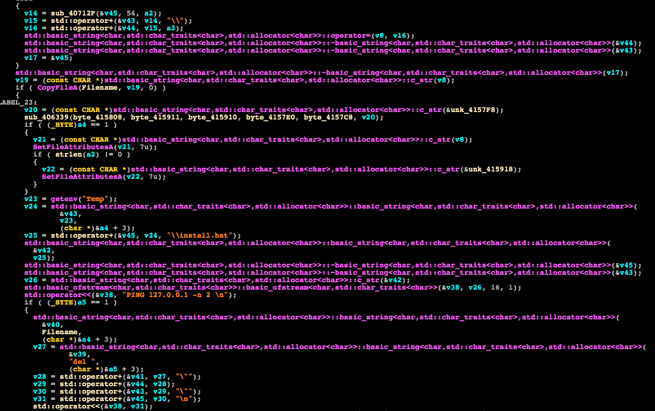
A live command-and-control server is carrying out an attack that’s dropping a few malware programs on victim’s machines, including the Jigsaw ransomware and the Remcos RAT (remote access Trojan) and its dropper. Credit and thanks go to Ido Naor of Kaspersky and Eyal Sela of ClearSky for making this discovery. The attack began on July 15 and has affected 250 victims so far, according to Naor.
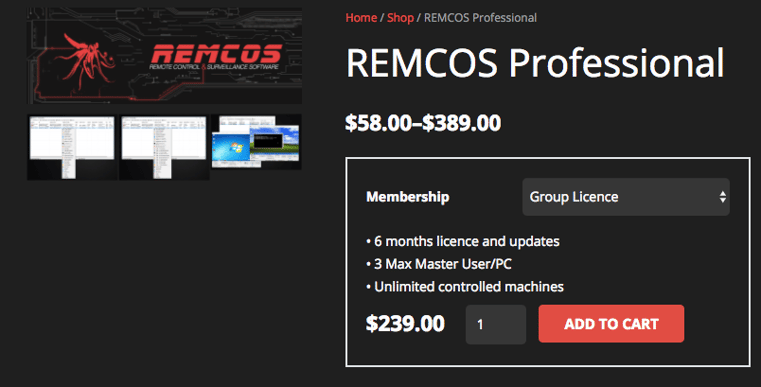
Remcos isn’t new. Security company Fortinet discovered it in February and noted that the RAT is commodity malware, anyone can buy and customize it and that it’s been around since the second half of 2016.
Remcos sells for $58 to $389, according to the company behind the software. The cheapest option is the starter license, which can be used on one machine for one month. The most expensive option is the enterprise license, which can be used on 10 machines for six months. There’s also an individual license ($189 for one machine for six months), a group license ($239 for three machines for six months) and a free version. Some of the capabilities Remcos offers include automatic tasks, surveillance functions, the ability to search for files and a remote screen capture function.
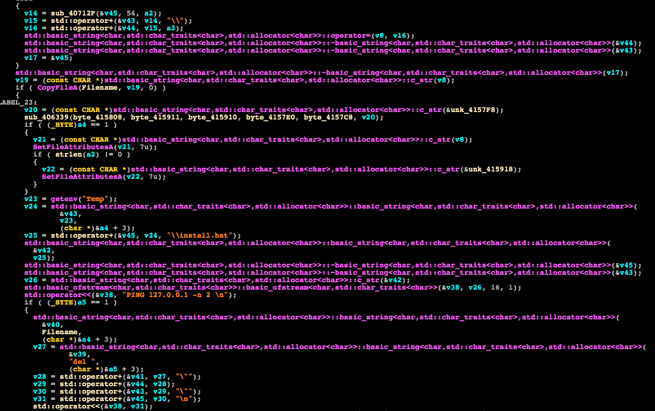
Remcos is marketed as a legitimate tool and can, in theory, be used for remotely managing computers. But in the instance Naor and Sela discovered, it was being dropped along with ransomware, leading us to believe that it’s being used for malicious purposes.
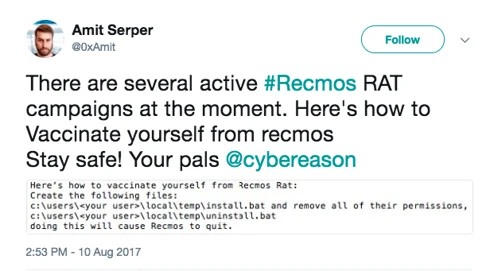
To help people protect themselves from this attack, Cybereason developed a “vaccine” that can be used to neutralize Remcos before it starts to run.
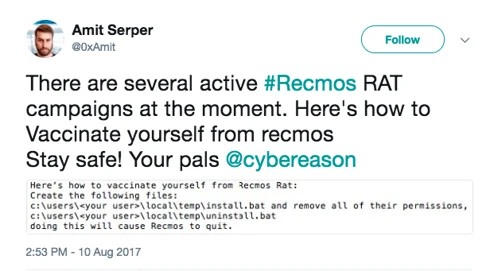
Users can create this vaccine by creating these two files and removing all of their permissions:
c:\users\admin\AppData\Local\temp\install.bat
c:\users\admin\AppData\Local\temp\uninstall.bat
Stay safe out there.