ON-DEMAND
![]()
R3 MITRE ATT&CK EVALUATIONS EXPLAINED
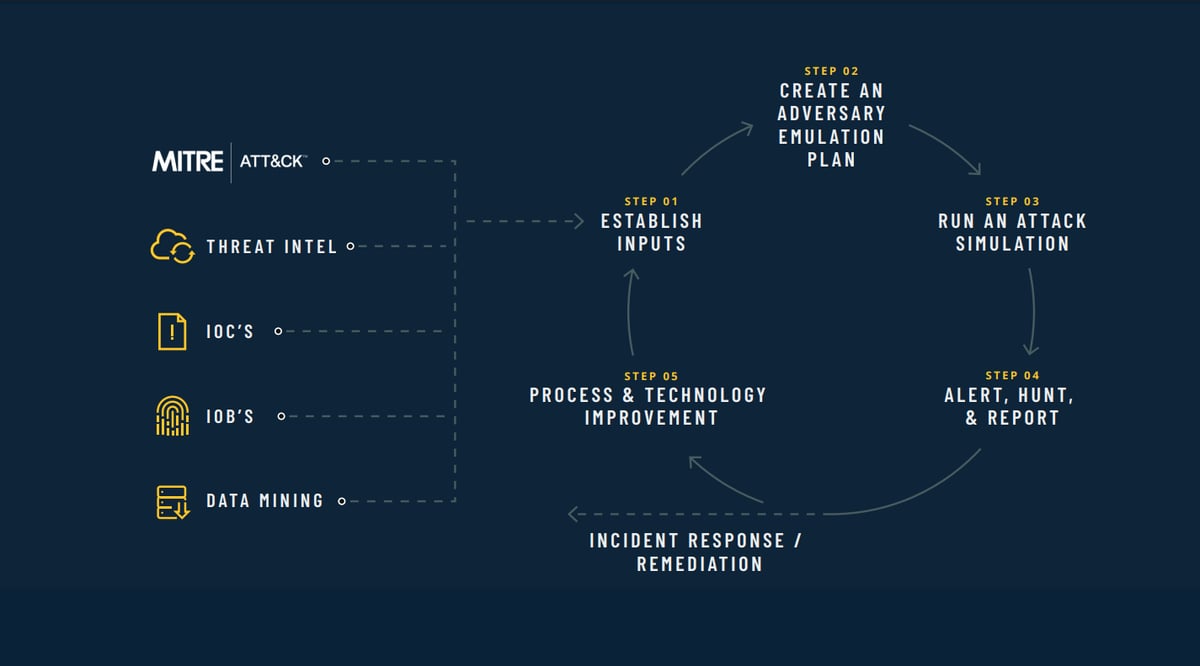
The MITRE ATT&CK evaluations test security vendors’ ability to quickly detect and stop tactics and techniques used by today’s threat actors. In this session, we're going to boil down the complexity of the MITRE ATT&CK framework so your organization can understand:
-
How to interpret the results across Protection, Detection and Linux.
-
The difference between Technique, Tactic, and Telemetry detections.
-
Why organizations are mapping to the MITRE ATT&CK framework and what’s next.
Looking for your time zone?
Attend the EMEA session | Attend the APAC session
.png)