Webinar
![]()
CYBER SUMMER WITH CURRY, EPISODE 2: STATE OF RANSOMWARE
ON DEMAND
Ransomware attacks continue to make headlines, and for good reason: on average, there is a new ransomware attack every 11 seconds, and the losses to organisations from ransomware attacks is projected to reach $20 billion over the course of 2021
Sam Curry revisits ransomware research and insights delivered by Cybereason's Nocturnus and incident response teams. You'll hear the team explore insights based upon what is happening in the underground and first hand experience from what customers have encountered in the wild.
Get a snapshot of the current state of ransomware, some highlights include:
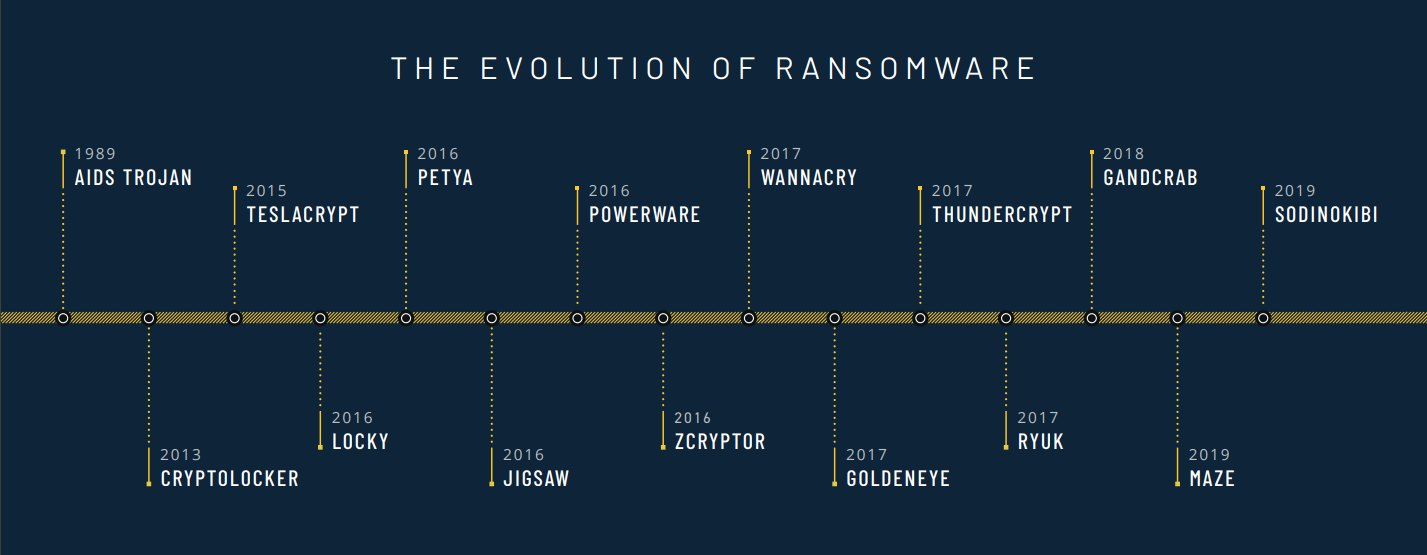
• Evolution of ransomware
• Current trends and new tactics
• Lessons from the field
• Lessons from the field
• How to better protect your organization from ransomware
.png)